|  |  | [](https://hub.subspace.services/uploads/images/gallery/2025-05/ring.png) |
A kernel is the most essential and core part of something greater.
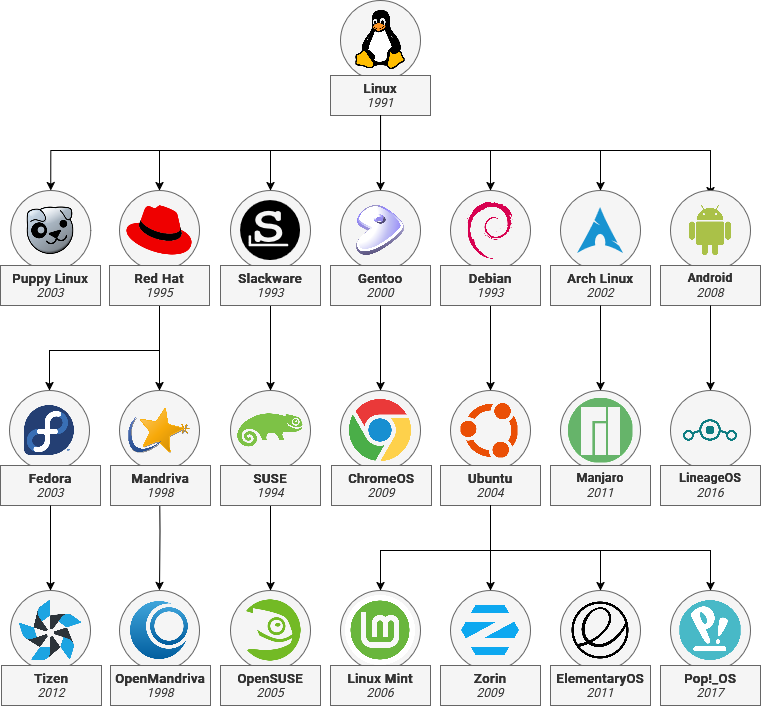
[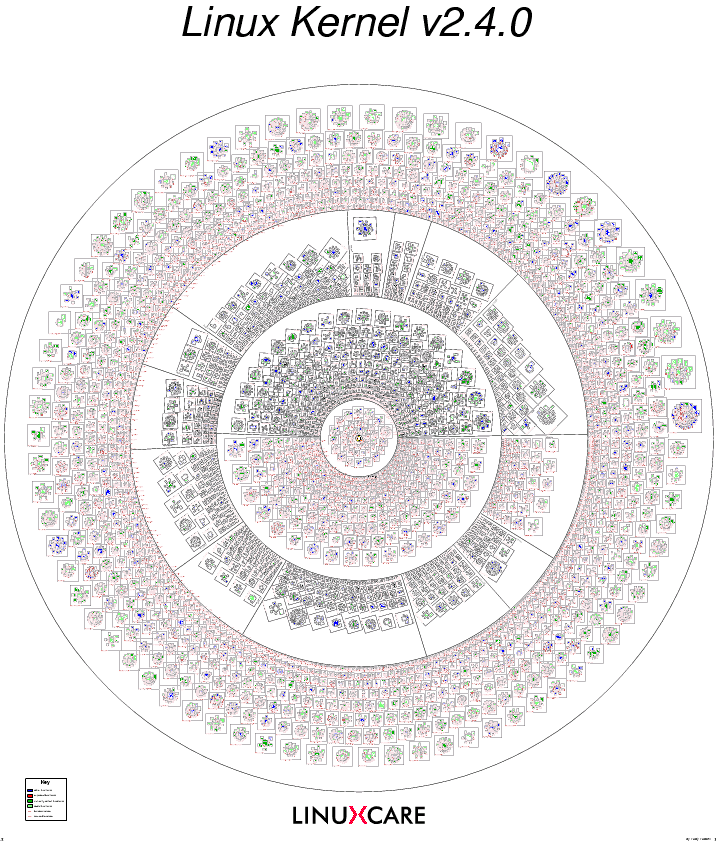](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000352.png)[Visualization of Open-Source Projects in the Linux Kernel](https://fcgp.sourceforge.net/) While the [Linux kernel](https://en.m.wikipedia.org/wiki/Linux_kernel) is perhaps the most well-known open-source kernel, it is [far from the only option](https://en.m.wikipedia.org/wiki/Comparison_of_operating_system_kernels). Notable examples being [FreeBSD](https://en.m.wikipedia.org/wiki/FreeBSD), [OpenBSD](https://en.m.wikipedia.org/wiki/OpenBSD) and [NetBSD](https://en.m.wikipedia.org/wiki/NetBSD), as well as specialized kernels like GNU [Hurd](https://en.m.wikipedia.org/wiki/GNU_Hurd) and [Mach](https://en.m.wikipedia.org/wiki/Mach_(kernel)). Microsoft [Windows](https://en.m.wikipedia.org/wiki/Architecture_of_Windows_NT) and [MacOS](https://en.m.wikipedia.org/wiki/Darwin_(operating_system)) also use their own proprietary "[closed-source](https://en.m.wikipedia.org/wiki/Proprietary_software)" kernel for their operating systems. ### Drivers The Kernel uses modular software known as [drivers](https://en.m.wikipedia.org/wiki/Device_driver) to control hardware components. There are a wide range of drivers available for a diverse range of devices – from proprietary drivers from corporations to open-source drivers that provide basic features. [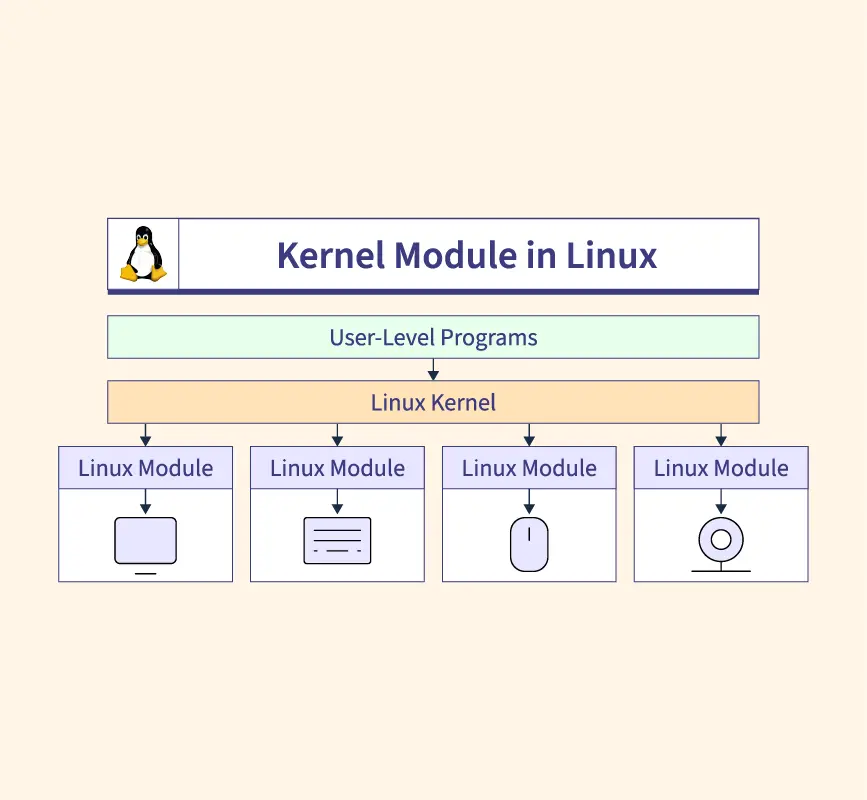](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000347.webp)
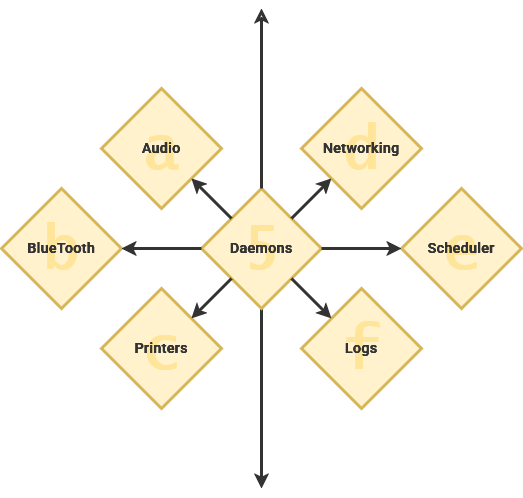
| Daemon | Description |
| [syslogd](https://en.m.wikipedia.org/wiki/Syslogd) | Handles error logs |
| [sshd](https://en.m.wikipedia.org/wiki/Secure_Shell#Use) | Handles SSH connections |
| [PulseAudio-d](https://en.m.wikipedia.org/wiki/PulseAudio) | Handles system audio |
| [D-Bus-Daemon](https://en.m.wikipedia.org/wiki/D-Bus) | Handles communication between applications |
| [cups-daemon](https://en.m.wikipedia.org/wiki/CUPS) | Handles printer integration |
It is named the "shell" because it is [outermost layer surrounding the operating system](http://www.catb.org/jargon/html/S/shell.html).
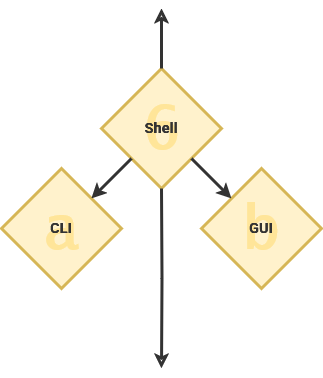
| [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000379.jpg) |
| [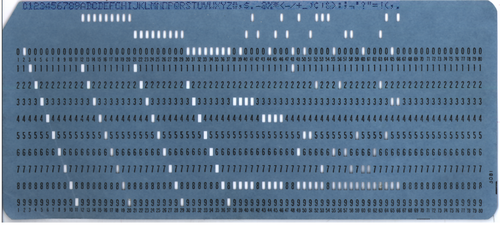](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000380.png) |
| [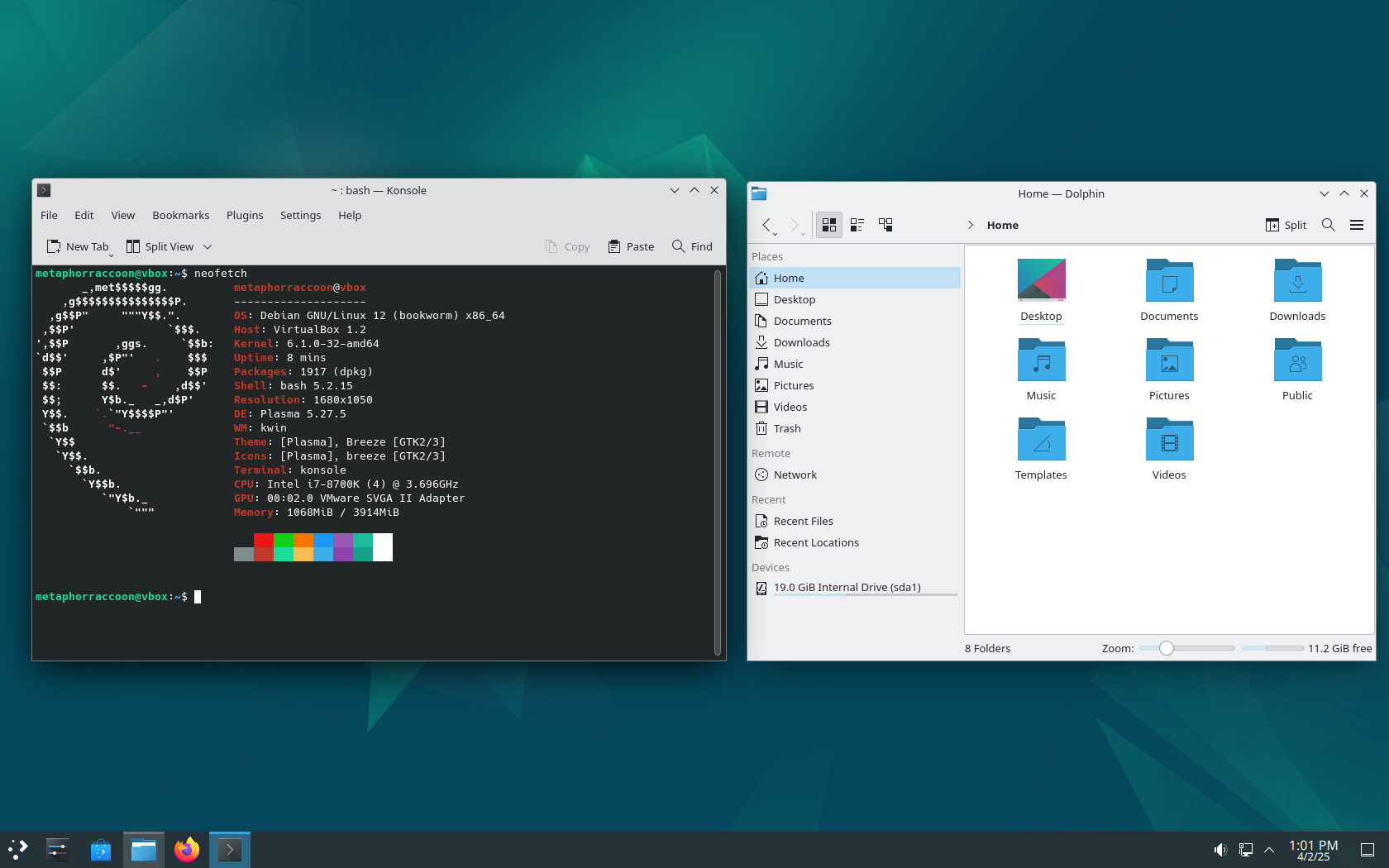](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-plasma-02-04-2025-13-01-16.png) [KDE Plasma](https://kde.org/plasma-desktop/) | [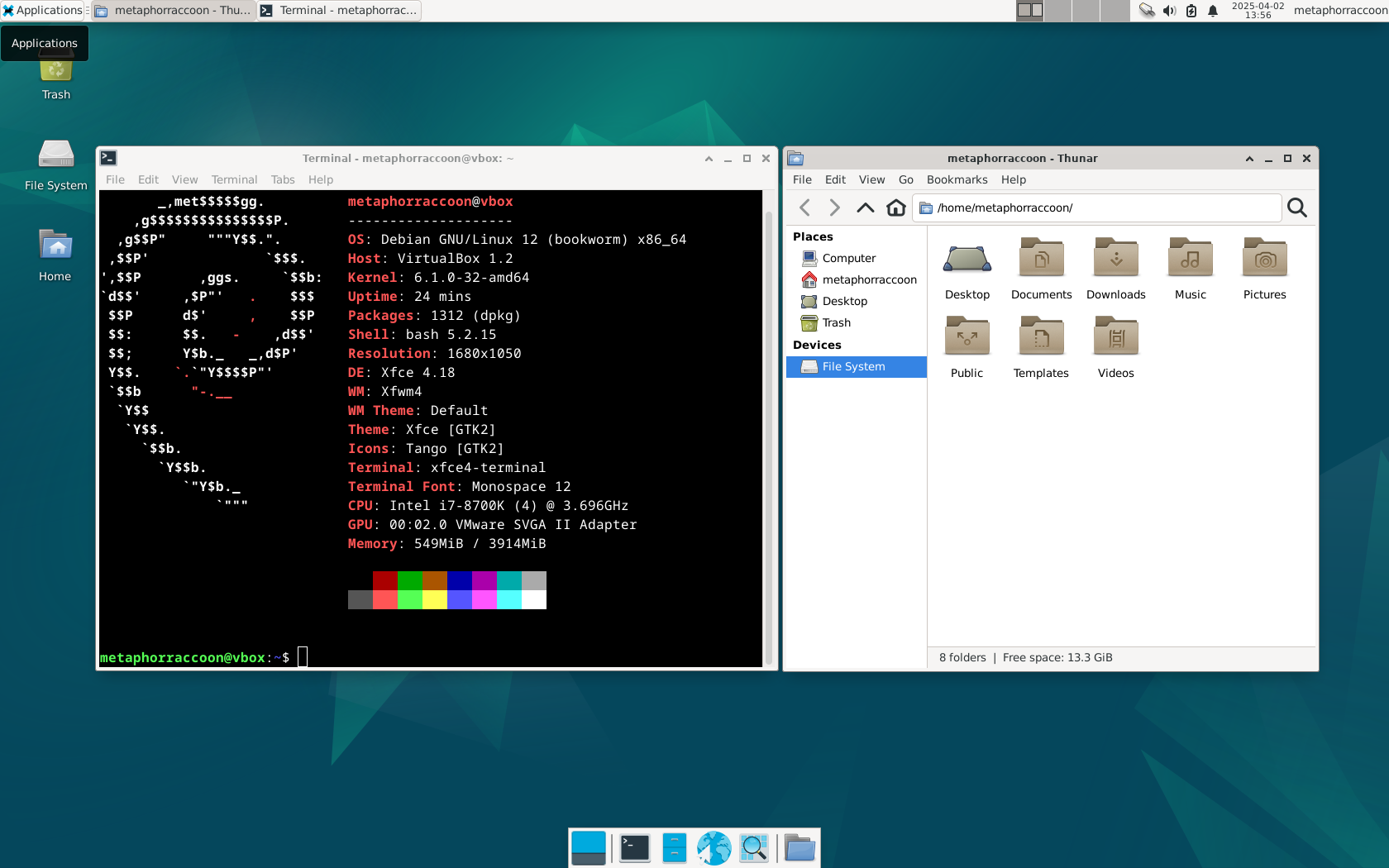](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-xfce-02-04-2025-13-56-51.png) [Xfce](https://www.xfce.org/) | [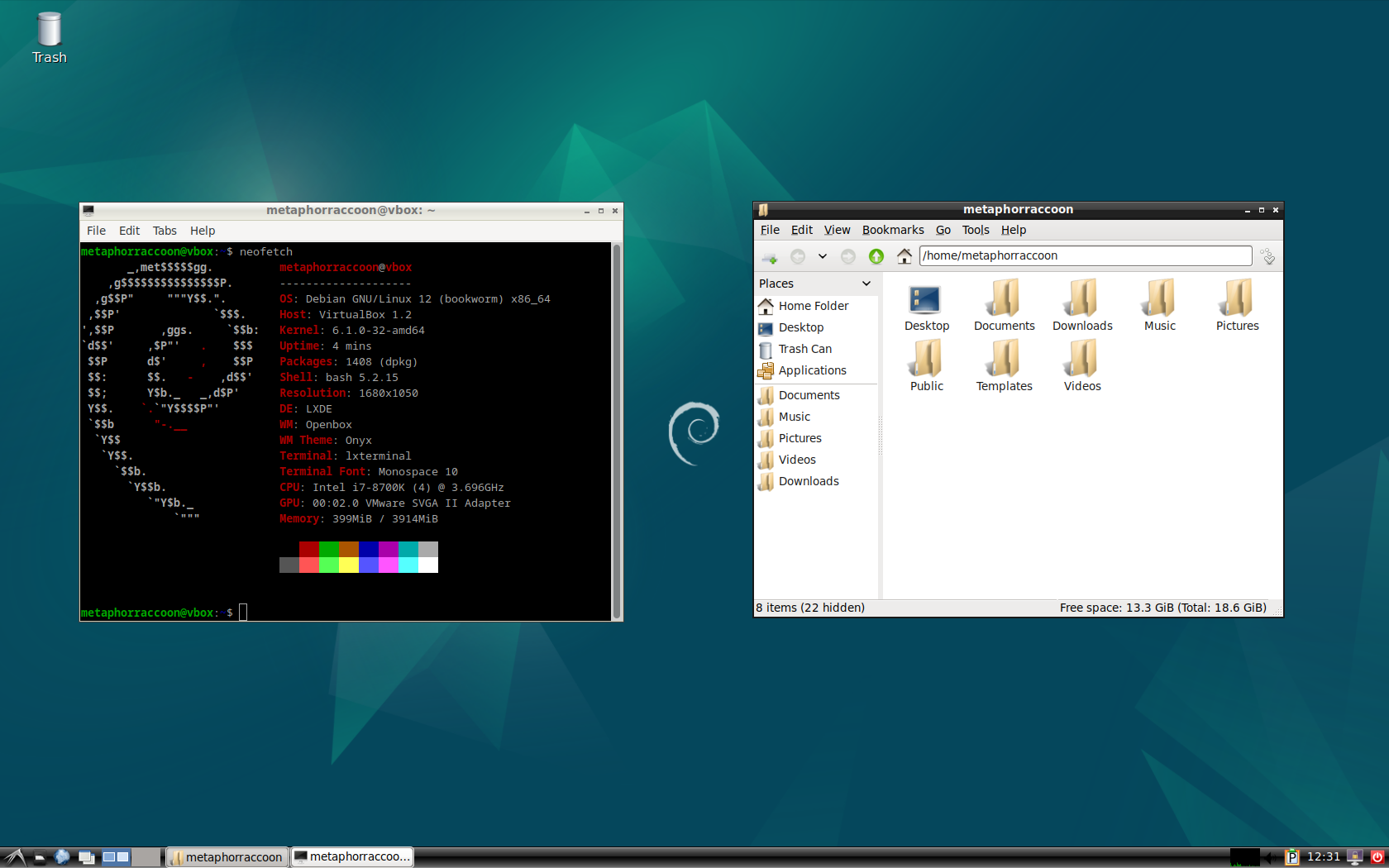](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-lxde-02-04-2025-12-31-42.png) [LXDE](https://www.lxde.org/) |
| [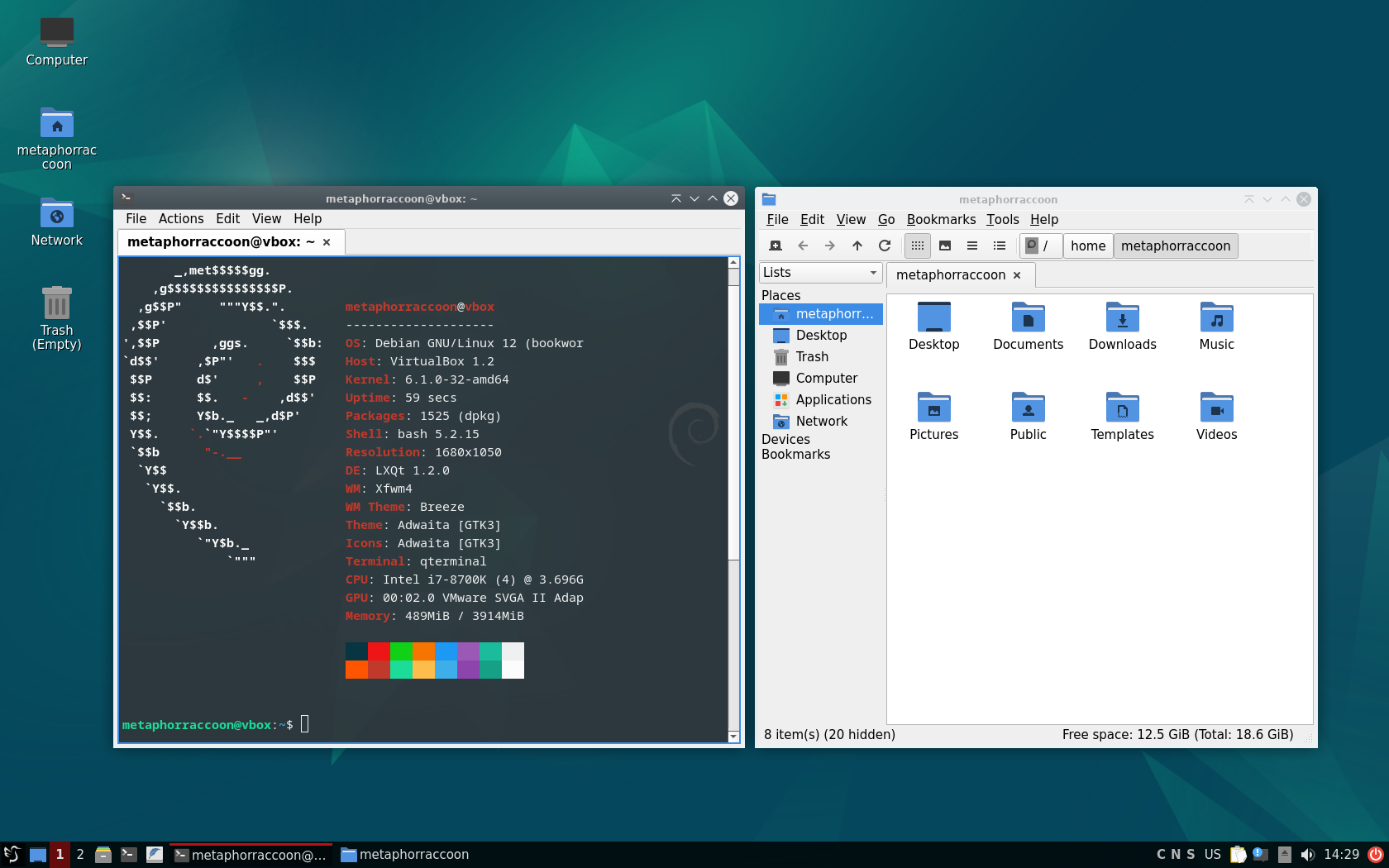](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-lxqt-02-04-2025-14-29-44.png) [LXQt](https://lxqt-project.org/) | [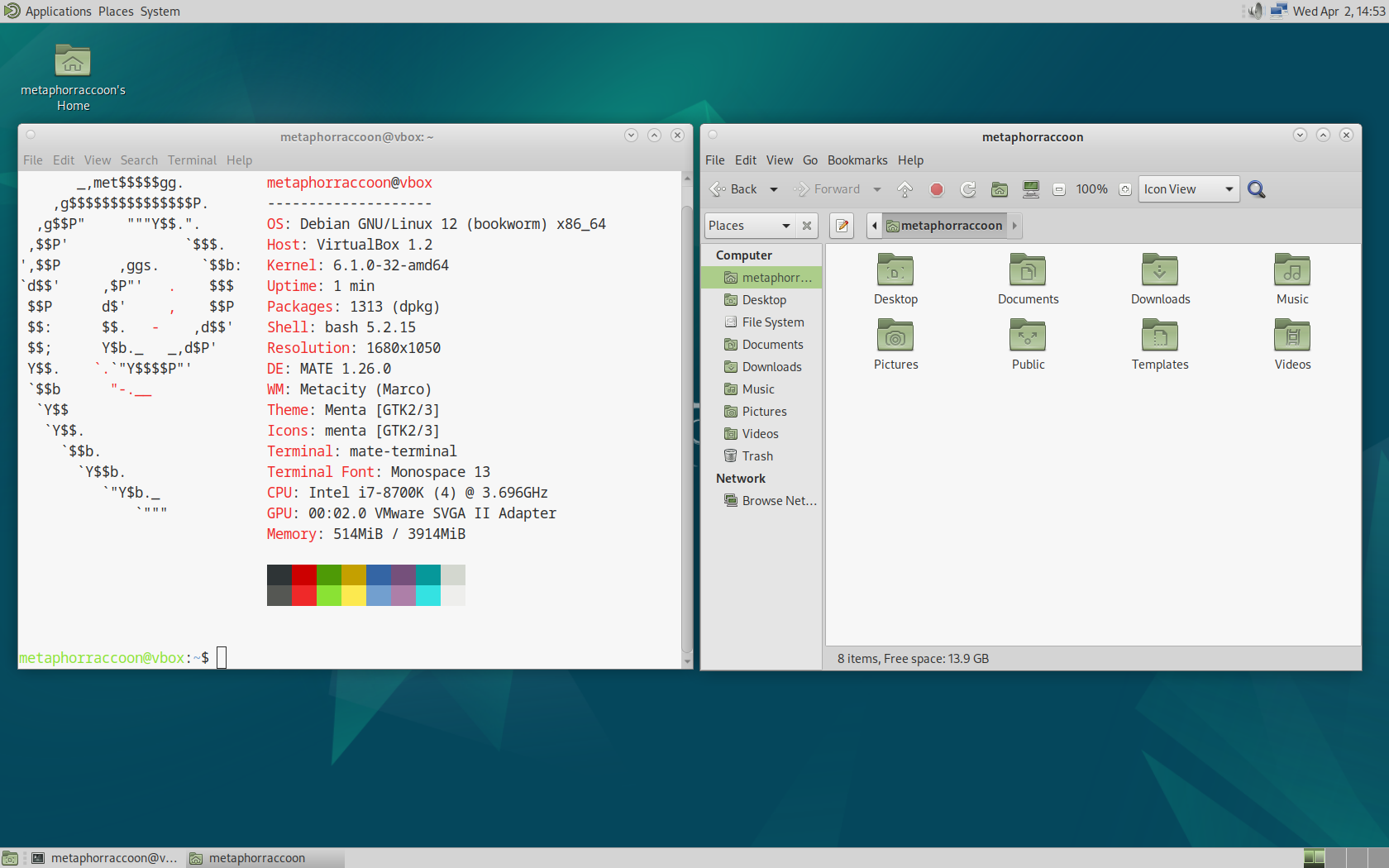](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-mate-02-04-2025-14-52-59.png) [MATE](https://mate-desktop.org/) | [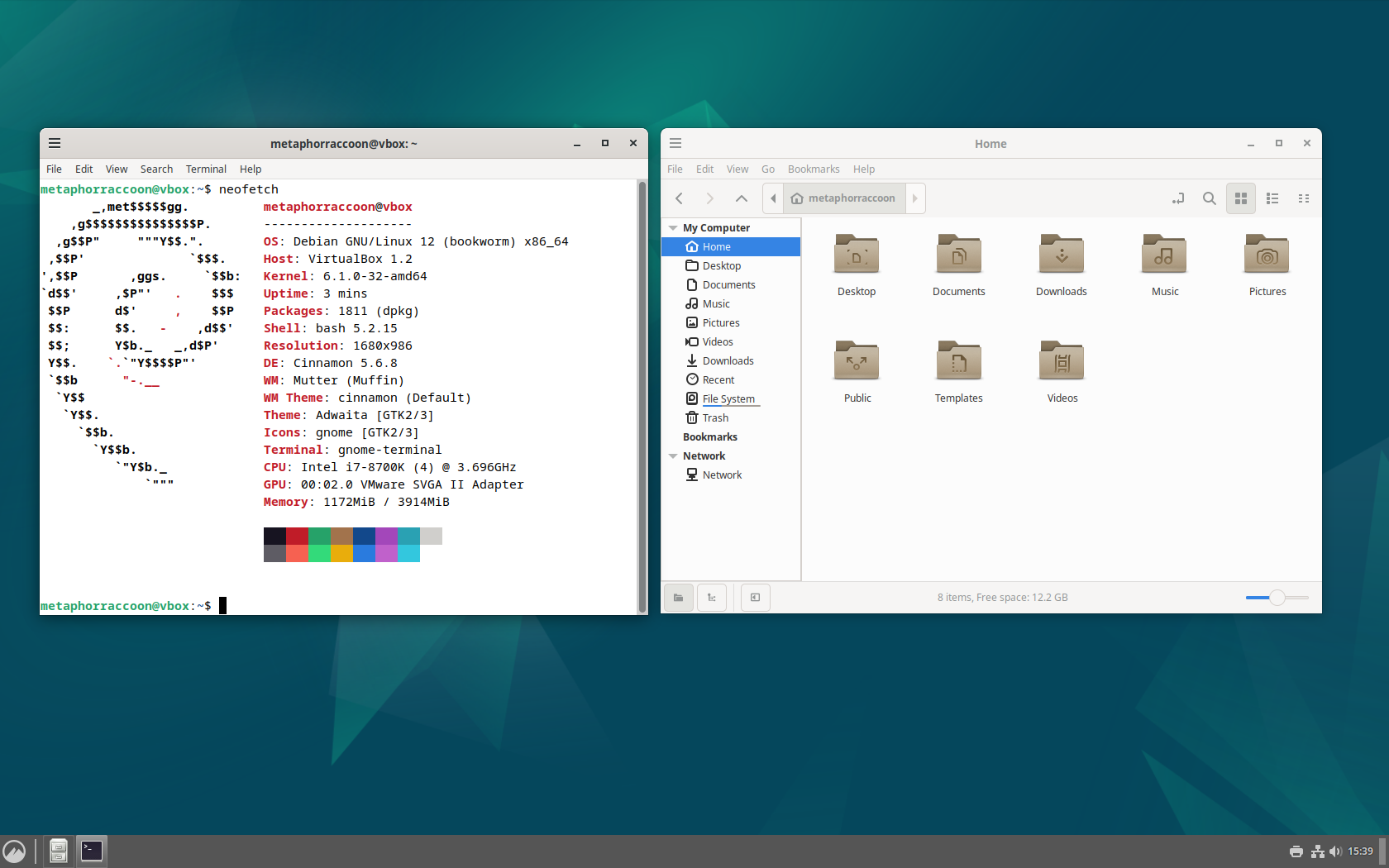](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-cinnamon-02-04-2025-15-39-08.png) [Cinnamon](https://projects.linuxmint.com/cinnamon/) |
Windows path use a backslash ("\\") while Linux uses a forward slash ("/").
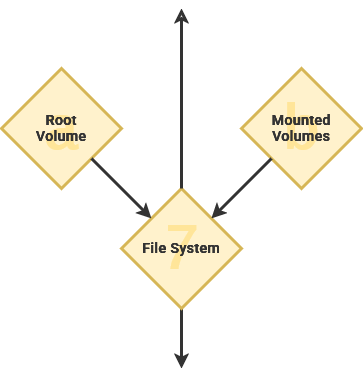
[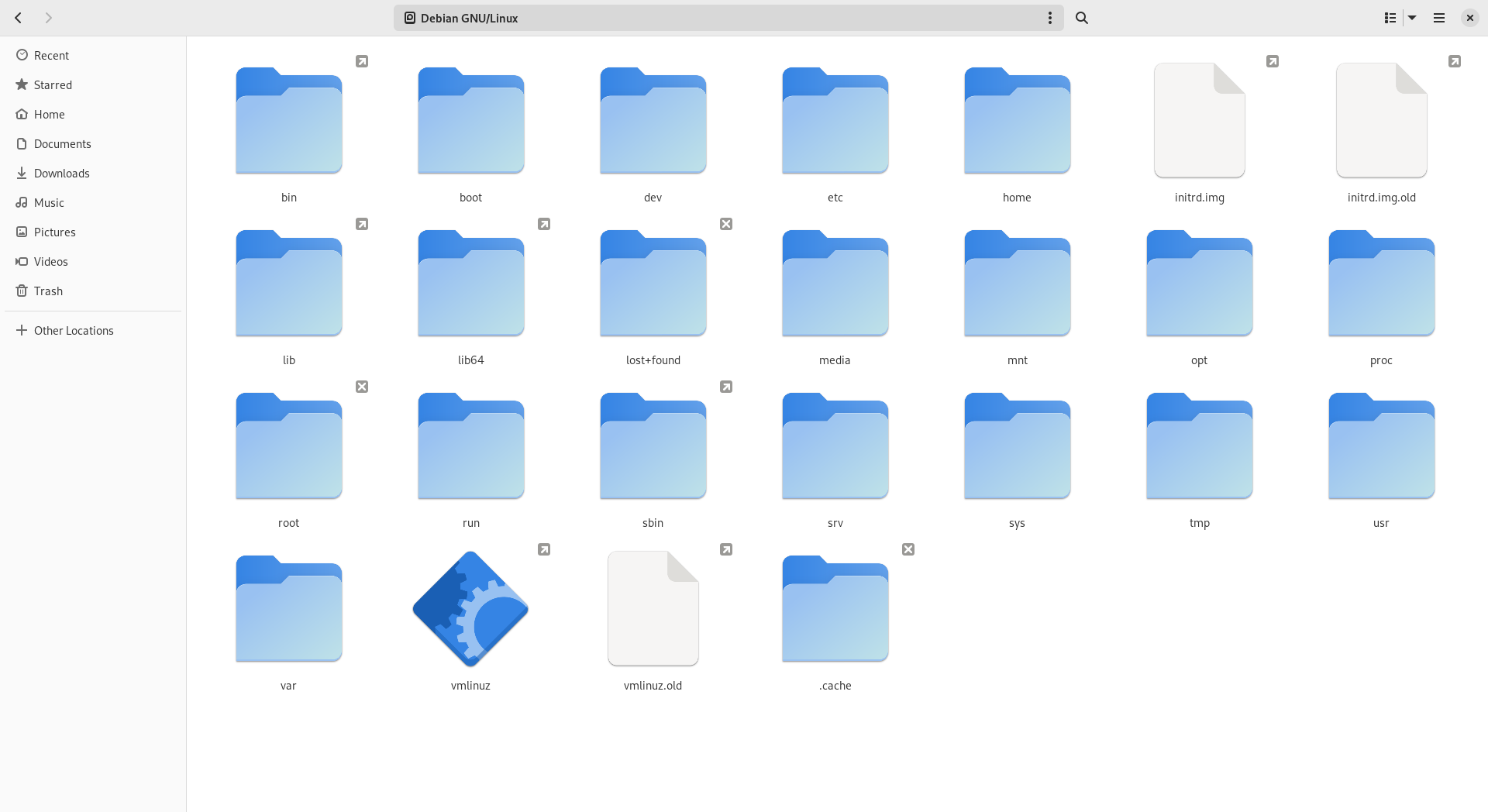](https://hub.subspace.services/uploads/images/gallery/2025-03/AkCimage.png) When a computer system has multiple storage drives, they are located as a subdirectory within "*/mnt*". This enables all of our storage drives to be accessible from the root "/" folder. As an example, we could mount an external USB hard disk drive to "*/mnt/flashdrive*".The Windows operating system assigns a letter designation to each drive, effectively creating multiple root folders – such as "*C:\\*" and "*D:\\*".
Linux follows an "[everything is a file](https://en.m.wikipedia.org/wiki/Everything_is_a_file)" design philosophy. This functionally means that information about hardware and software appear within the root folder as a file. As an example, the directory "*/proc*" doesn't exist on your storage drive. It is instead a [virtual filesystem showing real-time data](https://en.m.wikipedia.org/wiki/Procfs) about the kernel and other running software.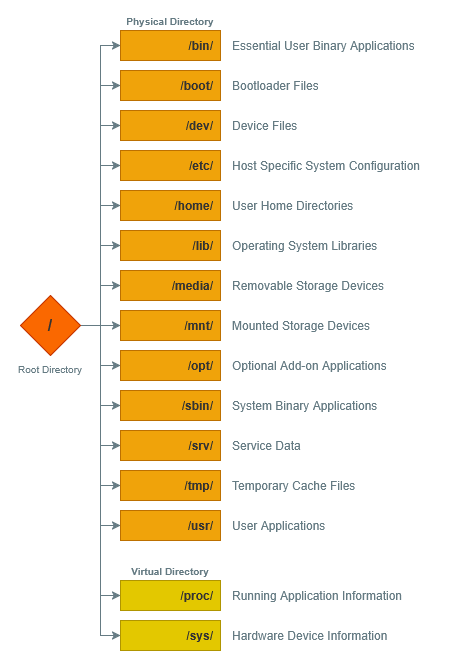
The 1978 book "The C Programming Language" introduced the now traditional "[Hello, World!](https://en.m.wikipedia.org/wiki/%22Hello,_World!%22_program)" code example employed by many programming languages.
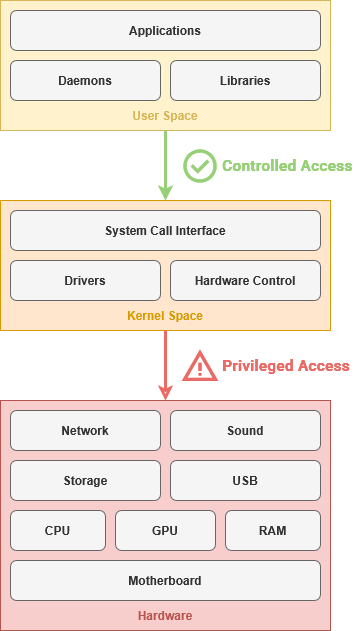
[High-level programming languages](https://en.m.wikipedia.org/wiki/High-level_programming_language) like Fortran are highly abstracted from the underlying 1s and 0s needed to control hardware. These focus on creating human-readable computer instructions and are [primarily based on the English language](https://en.m.wikipedia.org/wiki/English_in_computing). This made coding more intuitive while also allowing software to be portable across computers. Completed software code written using a program language can be run on compatible hardware. Compiled languages like Fortran are broken down into easy-to-use "binary" applications for a specific architecture – such as MacOS, Windows or Debian. These languages take the human-readable logic and convert it directly into machine code. [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000438.png) Interpreted languages like JavaScript are run line-by-line from their written form – commonly known as a script. The computer executes the code in the same way a human would read it. By contrast, these languages interpret the human-readable logic into machine code on-the-fly as needed to complete tasks. ### A Common Language The [System Call Interface](https://en.m.wikipedia.org/wiki/System_call) allows the applications to access computer hardware without needing to communicate with specific hardware components. This way, an application doesn't need to know how to communicate with your exact hard drive model – instead, it can just use the System Call Interface to ask the operating system to write data to the hard drive on its behalf. This abstracts a great deal of underlying information, much like the delineation between hardware and software. [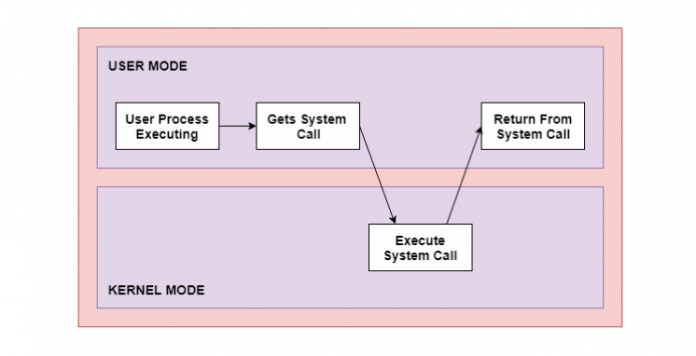](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000435.png) This is an example of an [Application Programming Interface](https://en.m.wikipedia.org/wiki/API) – or API – that allows software to communicate through a mutually agreed upon language. This is how your web browser can access a web camera connected to your computer though a USB cable, or a word processor can edit a document file on your external hard drive. ### User Applications These programs are intended for end-users to perform tasks that are not related to the general operation or administration of the computer. These may be installed by an administrator for everyone, or installed by a specific user for their own needs. Program, application, software – and even script – are often used interchangeably to refer to this type of code. This category includes – but is [not limited to](https://en.m.wikipedia.org/wiki/Application_software) – office productivity suites, media players, web browsers and photo editors. Many modern operating systems provide digital storefronts to download and install open-source and proprietary software to your local computer system. ### Server Applications While user applications are geared towards a person sitting in a chair in front of that computer, server software is intended for use by other computers and the people who use them. When you visit most websites and web apps – such as [diagrams.net](https://app.diagrams.net/) – you are using your personal computer to remotely load a server application. The [client—server model](https://en.m.wikipedia.org/wiki/Client%E2%80%93server_model) structures applications so that individual people or computers – known as [clients](https://en.m.wikipedia.org/wiki/Client_(computing)) – can retrieve information from a centralized location – known as a [server](https://en.m.wikipedia.org/wiki/Server_(computing)). Instead of installing and managing user applications on a personal computer, administrators can create a server application accessible by people over our local network. When a server shares it's resources, it is providing a *service*.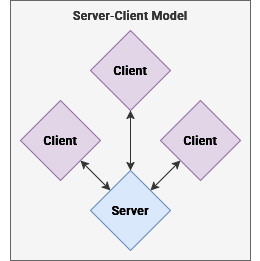
The [PDP-7](https://en.m.wikipedia.org/wiki/PDP-7) ran the first Unix code – used for creating the demo video game [Space Travel](https://en.m.wikipedia.org/wiki/Space_Travel_(video_game)).
| [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000479.jpg) | [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000480.png) |
[Cathedral and the Bazaar](https://en.m.wikipedia.org/wiki/The_Cathedral_and_the_Bazaar) was a foundational book by [Eric S. Raymond](https://en.m.wikipedia.org/wiki/Eric_S._Raymond "Eric S. Raymond") about opposing software project management styles.
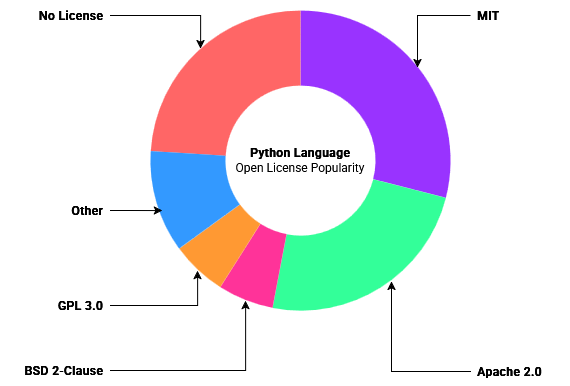
Unix was revolutionary not only as an operating system, but because it came bundled with a complete copy of the source code used to build it. This allowed researchers to modify the code to fulfill their needs while also enabling corporations to create their own custom Unix distributions – for use in-house or as a marketable product. This led to a proliferation of Unix operating systems, each with exciting new features. Windows vs Mac vs Linux vs Unix timeline graphic [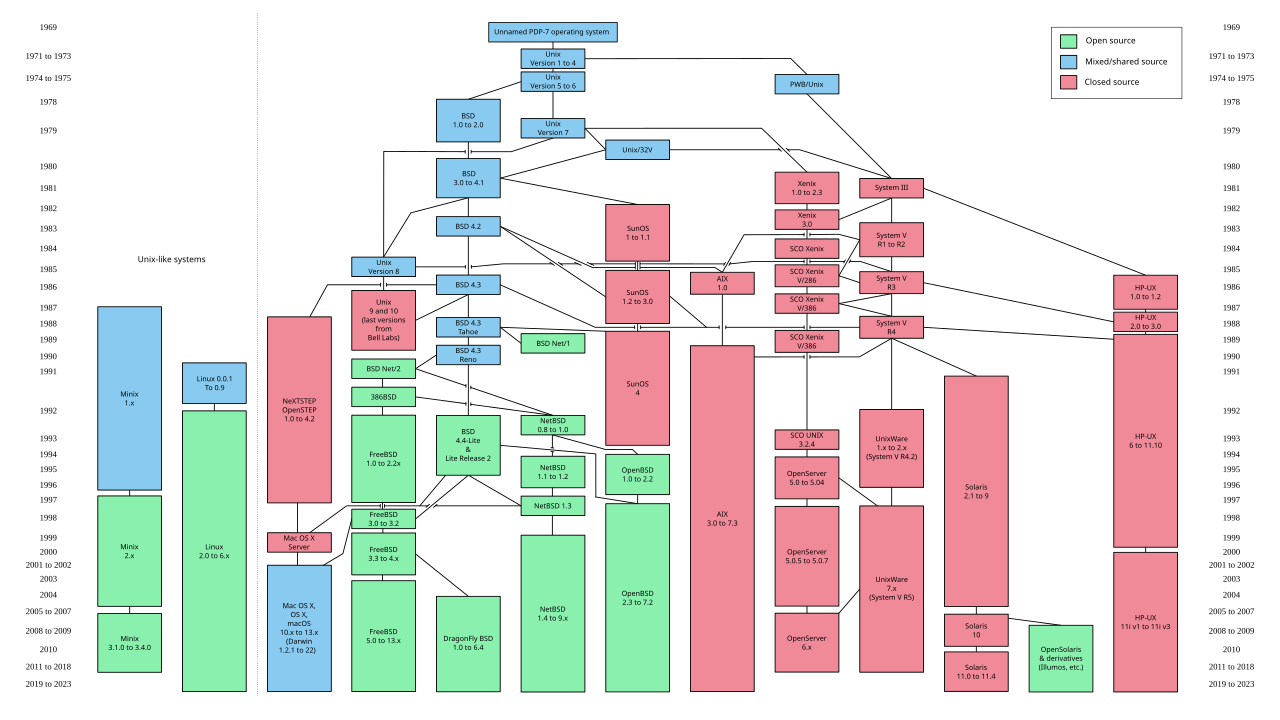](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000439.png) [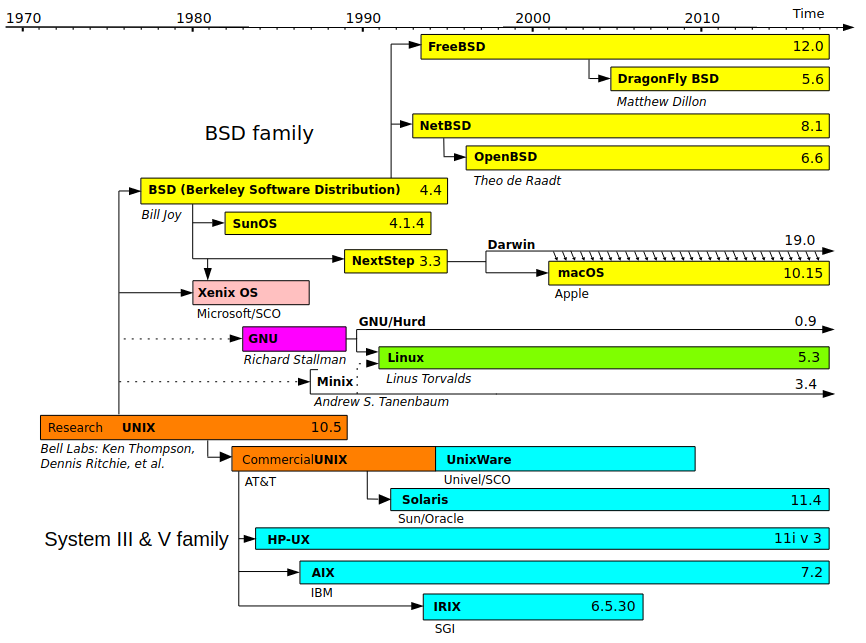](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000440.png) [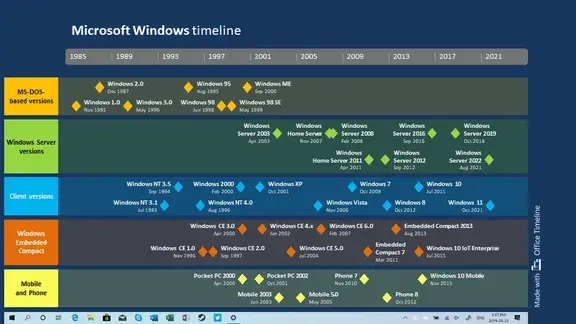](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000443.webp) Software – like hardware – became increasingly commercialized throughout the 1970s. Corporations sought to mold hardware into compact personal devices while simultaneously fashioning software into the [killer application](https://en.m.wikipedia.org/wiki/Killer_application) that would draw consumers to their products. The [Unix Wars](https://en.m.wikipedia.org/wiki/Unix_wars) throughout the 1980s exacerbated the friction between vendors as the operating system became fragmented between multiple competing standards. As corporations navigated this space, many preferred to follow the proprietary development model. These release cycles are often measured in years – meaning that software was released as polished product with meticulous planning put into [final 'gold' release](https://en.m.wikipedia.org/wiki/Software_release_life_cycle#RTM). On the flip side, bug fixes and feature requests could take years to manifest in the publicly available product. Important software updates may never emerge – or may even be released as part of the product's successor. This 'release late—release rarely' philosophy arises when the software developers [regard their project as a consumer product.](https://dsbscience.com/freepubs/linuxoverwindows/node3.html) While the product is marketed towards consumers, their role in the creative process is rather limited. Their feedback is often collected reactively during formative beta testing – or even after the product is released to the public. [Proprietary software](https://en.m.wikipedia.org/wiki/Proprietary_software) is often "closed-source", meaning that the code to create it is private and legally protected – or even a [trade secret](https://en.m.wikipedia.org/wiki/Trade_secret). The code is compiled into a [binary file](https://en.m.wikipedia.org/wiki/Binary_file) containing the raw binary data – ones and zeros – used to control a computer system. This data it is not human-readable and only works on a specific platform – such as Windows, MacOS or Debian Linux. This makes it relatively difficult to [reverse engineer](https://en.m.wikipedia.org/wiki/Reverse_engineering), but it also means that the code wasn't compiled to run efficiently on your specific computer system. Instead, it is compiled to meet 'minimum system requirements' and more advanced hardware is rarely leveraged to your advantage. ### Software Freedoms During the 1970s, the original computer [hacker culture](https://en.m.wikipedia.org/wiki/Hacker_culture) – who enjoyed the creative challenge of overcoming hardware and software limitations – formed within academic institutions. It was around this time that the [Free Software Movement](https://en.m.wikipedia.org/wiki/Free_software_movement) began to take shape. Researchers continued to develop software collaboratively by sharing their discoveries and the source code that powered them. This was foundational to the continued growth of the [Unix experiment](https://en.m.wikipedia.org/wiki/Research_Unix). [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000506.jpg) In 1984, [Richard Stallman](https://en.m.wikipedia.org/wiki/Richard_Stallman) resigned from his position at MIT citing that proprietary software stifled collaboration by limiting his labs ability to share source code. He began work on the GNU Project – which stands for *GNU's Not Unix* – and represented an idealized ,"free" operating system. It behaved almost exactly like Unix to attract developers, but the source code would be available for anyone to modify. [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000463.png) > The word "free" in our name does not refer to price; it refers to freedom. First, the freedom to copy a program and redistribute it to your neighbors, so that they can use it as well as you. Second, the freedom to change a program, so that you can control it instead of it controlling you; for this, the source code must be made available to you. > > — [GNU's Bulletin, Volume 1](https://www.gnu.org/bulletins/bull1.txt) The [Free Software Foundation](https://en.m.wikipedia.org/wiki/Free_Software_Foundation) he sparked – through his call-to-action known as the [GNU Manifesto](https://en.m.wikipedia.org/wiki/GNU_Manifesto) – initially caused some confusion. He often had to explain that he meant "free" as in "freedom" not as in "beer". This led to the foundation of the movement: [the four software freedoms](https://en.m.wikipedia.org/wiki/The_Free_Software_Definition).| Counter\_1 | **Freedom 1** The freedom to run the program as you wish, for any purpose. |
| Counter\_2 | **Freedom 2** The freedom to study how the program works, and change it so it does your computing as you wish. |
| Counter\_3 | **Freedom 3** The freedom to redistribute copies so you can help your neighbor. |
| Counter\_4 | **Freedom 4** The freedom to distribute copies of your modified versions to others. By doing this you can give the whole community a chance to benefit from your changes. |
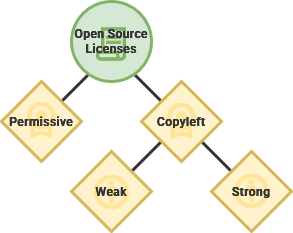
| **Copyleft Licenses** | |
| License | [**GPL**](https://choosealicense.com/licenses/gpl-3.0/) *1989* A [strong copyleft license](https://www.gnu.org/licenses/licenses.html) that comes with many conditions for usage within derivative software while providing express consent to use related patents. |
| License | [**The Unlicense**](https://choosealicense.com/licenses/unlicense/) *2010* This license foregoes intellectual copyright and [attributes all work to the public domain](https://www.gnu.org/licenses/license-list.en.html#Unlicense). While not technically copyleft, this [anti-copyright](https://en.m.wikipedia.org/wiki/Anti-copyright) license is [compatible with the GNU GPL](https://www.gnu.org/licenses/gpl-faq.html#WhatDoesCompatMean). |
| License | [**Mozilla Public License 2.0**](https://choosealicense.com/licenses/mpl-2.0/) *2012* This license balances the concerns of free software proponents and proprietary software developers. |
| **Permissive Licenses** | |
| License | [**Apache**](https://choosealicense.com/licenses/apache-2.0/) *2004* A permissive license that allows that this software can be incorporated into larger projects that themselves are released under a different license. |
| License | [**MIT**](https://choosealicense.com/licenses/mit/) *1987* This straightforward license only requires that the licensing information is shown, otherwise the software can be used freely for any reason. |
| License | **[BSD 4-Clause](https://choosealicense.com/licenses/bsd-4-clause/)** *1990* The first in a [family of permissive licenses](https://en.m.wikipedia.org/wiki/BSD_licenses) with the original requiring acknowledgement in the advertisement of all derivative works. |
Debian codenames come from the *[Toy Story](https://en.wikipedia.org/wiki/Toy_Story_(franchise) "Toy Story (franchise)")* film universe.
[](https://hub.subspace.services/uploads/images/gallery/2025-06/debian-bo.png) *Debian v1.3 "Bo"* Debian is a volunteer-operated software project and [accompanying non-profit organization](https://en.m.wikipedia.org/wiki/Software_in_the_Public_Interest) that operate entirely over the internet. Guided by an annually [elected leader](https://en.wikipedia.org/wiki/List_of_Debian_project_leaders), their operation is governed by three foundational documents that outline the mission and vision for their software:| Counter\_1 | [**Social Contract**](https://lists.debian.org/debian-announce/1997/msg00017.html) This [document](https://en.wikipedia.org/wiki/Debian_Social_Contract) outlines core principles of the project, as well as the expectations and requirements of developers who create on its behalf. |
| Counter\_2 | [**Free Software Guidelines**](http://lists.debian.org/debian-announce/debian-announce-1997/msg00017.html) This [document](https://en.wikipedia.org/wiki/Debian_Free_Software_Guidelines) defines "free software" and sets the requirement for software that can be used to build the operating system. While similar to the GNU Manifesto, these guidelines specifically lay out avenues for a relationship with commercial "[non-free](https://en.m.wikipedia.org/wiki/Proprietary_software)" software. |
| Counter\_3 | [**Constitution**](http://www.debian.org/devel/constitution) This document explores formal power structures, lying out the responsibilities of the Debian project leader and other organizational roles. |
The Four Software Freedoms were not known to the Debian project at the time.
From their perspective, the modular nature of Linux allowed people to work together despite differences in project philosophy and organization. They defined open-source software licenses that supported the spirit of the project while explicitly opening the door to commercial "non-free" software. They placed their bet on the contributions of both corporations and communities to propel mutual growth. ## Crowdsourcing Security [Security](https://en.m.wikipedia.org/wiki/Security) can be slippery defintion that encompasses so many different things. It manifests as a [noun](https://en.m.wiktionary.org/wiki/security): in the moment, when we are safe from harm in our beds at the end of the day. It also takes shape as a [verb](https://en.m.wiktionary.org/wiki/secure): occurring over time through our proactive measures to ensure our safety. Security is [both a feeling and a reality](https://www.wired.com/2008/04/securitymatters-0403/). We contribute to our own feeling of safety by locking the door and enacting this simple layer of security. While the locked door may be technically easy to overcome, an ongoing relationship with our neighbors and communities lends weight to this assurance. Our society frowns on the theft of property and our laws create consequences for a trespasser's actions. Security is a mindset and an ongoing relationship, not a task or a checklist that can be completed. Protective measures shouldn't occur in isolation, but within a holistic system that values and respects security overall. We build ourselves communities who impart onto us the feeling of safety. ### Decentralized Defenses [Cybersecurity](https://en.m.wikipedia.org/wiki/Computer_security) carries this vigilance into the digital systems we create to connect us. By using proprietary software, people must often tacitly accept the security [provided by the developers](https://www.researchgate.net/publication/3437446_Software_security_for_open-source_systems). The open-source Linux operating system approaches security in a fundamentally different way than "closed-source" ones – like Windows and MacOS. Proprietary software rely on the concept of [security by obscurity](https://en.m.wikipedia.org/wiki/Security_through_obscurity) – the idea that it is difficult to exploit what you cannot see. This has been [proven untrue time and time again](https://csrc.nist.gov/pubs/sp/800/123/final). Without the source code available, hackers can still exploit a system but the community cannot always respond. By contrast, the code powering Linux is openly available on the internet for review. At first thought, this may seem insecure and ill-advised – to advertise potential exploits to would-be hackers. However, a system that relies solely on obscuring vulnerability is not truly secure. [Linus's Law](https://en.m.wikipedia.org/wiki/Linus's_law) – named after the creator of the Linux kernel – asserts that "[given enough eyeballs, all bugs are shallow](http://www.catb.org/~esr/writings/cathedral-bazaar/cathedral-bazaar/ar01s04.html)". The philosophy claims that the more independent people are working on a project, the greater the chances of uncovering bugs early. With regards to emergent "[zero-day](https://en.m.wikipedia.org/wiki/Zero-day_vulnerability)" exploits, there are numerous communities searching for the same fix. While there have been no large-scale experiments or peer reviewed studies, [empirical evidence can offer some clues](https://arxiv.org/abs/2007.10912). Popular open-source software had a higher ratio of big fixes than less popular projects by the same company. Relatedly, [open-source GNU programs have demonstrated](https://ftp.cs.wisc.edu/pub/paradyn/technical_papers/fuzz-revisited.ps) they're [more reliable than their proprietary Unix counterparts](https://pages.cs.wisc.edu/~blbowers/fuzz-2001.pdf). We shouldn't allow ourselves to be [lulled into false sense of security around open-source software](https://www.researchgate.net/publication/222983408_The_Open_Source_approach_-_opportunities_and_limitations_with_respect_to_security_and_privacy). Simply making source code available to a broader community does not guarantee that vulnerabilities will immediately be found and fixed. While a large community of people may use the software, [there is no promise that they are engaging](https://www.researchgate.net/publication/2955595_Open_source_security_Opportunity_or_oxymoron). A potent illustration of this debate has been the [Heartbleed](https://en.m.wikipedia.org/wiki/Heartbleed) security bug persisting in a popular project for two years. An accidental vulnerability within [openssl](https://en.m.wikipedia.org/wiki/OpenSSL) – software that securely encrypts Internet connections – was [maintained entirely by fifteen unpaid volunteer developers](https://www.vox.com/2014/6/19/18076318/heartbleed). > [In these cases, the eyeballs weren't really looking.](http://www.esecurityplanet.com/open-source-security/why-all-linux-security-bugs-arent-shallow.html) > > — [Linux Foundation](https://en.m.wikipedia.org/wiki/Linux_Foundation) Director, Jim Zemlin ### Intentional Design Linux employs a [secure by design](https://en.m.wikipedia.org/wiki/Secure_by_design) philosophy that develops a robust architecture from the ground up with conscious planning put into design at every layer. The [Open Source Initiative](https://en.m.wikipedia.org/wiki/Open_Source_Initiative) works toward a vendor-neutral ecosystem welcoming contribution from all sectors. Corporations and communities can lend their voices to the future of open-source software. This offers healthy competition, enabling people with choices about how to use their electronics. The Linux ecosystem has built-in support from a diversity of distributions – such as the community-supported Debian, the corporate-focused Fedora, or a hybrid-approach like Ubuntu. [Crowdsourcing](https://en.m.wikipedia.org/wiki/Crowdsourcing) volunteers from open communities requires developers to consider how their software might be exploited from the start. By presenting source code, open communities can engage with [software review](https://en.m.wikipedia.org/wiki/Software_review) – which had been repeatedly shown to [address security issues](https://books.google.com/books?id=O3VB-zspJo4C&pg=PA154). Despite every precaution, exploits are bound to arise within a software program – especially as the code base grows larger, including code written and maintained by other developers. By the [security company Synopsys' estimates](https://www.synopsys.com/software-integrity/resources/analyst-reports/open-source-security-risk-analysis.html?intcmp=sig-blog-ossra1), over 80% of codebases have at least one known vulnerability – on average, a codebase may have upwards of 150 vulnerailities with documented solutions available for at least two years. [](https://hub.subspace.services/uploads/images/gallery/2025-06/1000000530.png) The [Open-Source Security Foundation](https://en.m.wikipedia.org/wiki/Open_Source_Security_Foundation) (known as OpenSSF) is dedicated to offering security testing. Through [Security Score Cards](https://securityscorecards.dev/), developers can quickly test their software for vulnerabilities. By extension, they can advertise their rating to help build community trust with the project. ### Coordinated Response Debian has created systems for [crowdsourcing and responding to emergent threats](https://www.debian.org/security/). They employ a [public bug tracking service](https://www.debian.org/Bugs/) that enables anyone to report inconsistencies with the operating system. Developers, researchers and [white hat hackers](https://en.m.wikipedia.org/wiki/White_hat_(computer_security)) can identify eminent threats, separating them from relatively minor programming errors.| Bug\_report | [**Bug**](https://en.m.wikipedia.org/wiki/Bug_(engineering)) This is a design or coding defect within a program that can lead to undesired effects – such as a crash. |
| Skull | [**Vulnerability** ](https://en.m.wikipedia.org/wiki/Vulnerability_(computer_security)) This is a weakness in a system – sometimes the result of a bug or design flaw – that can be leveraged to compromise the security of a system. |
| Crisis\_alert | [**Exploit** ](https://en.m.wikipedia.org/wiki/Exploit_(computer_security)) This is a procedure or program that take advantage of vulnerabilities within a system and allows a malicious actor to use it to their advantage. |
They [provide more in-depth installation procedures](https://www.ventoy.net/en/doc_start.html) should you need them.
[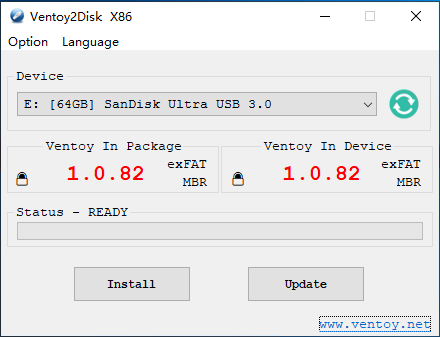](https://hub.subspace.services/uploads/images/gallery/2025-02/image.png) ## Downloading Debian Next, we need to get an installation disk image for our desires Linux distribution. For the broadest compatibility we'll be using [Debian, the "universal operating system"](https://www.debian.org/). Before we can install Debian on our computer, we must first download the appropriate installation image.The [AMD64 DVD installer](https://cdimage.debian.org/debian-cd/current/amd64/iso-dvd/) will work for most cases.
Download the appropriate ISO file using your web browser. ## Finalizing the USB Boot Disk Once downloaded, it needs to be copied to the USB flash drive. This can be accomplished by opening Windows Explorer and navigating to the USB drive named Ventoy. Copy the downloaded ISO file to this mounted drive. [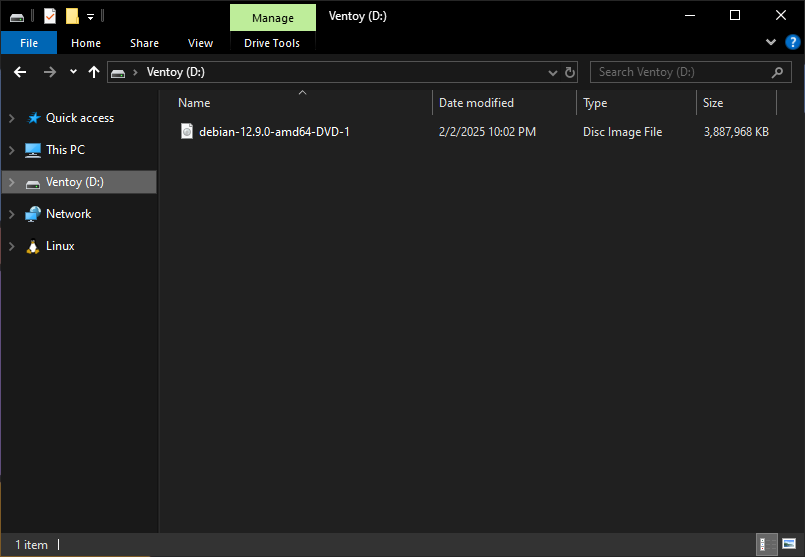](https://hub.subspace.services/uploads/images/gallery/2025-02/iWVimage.png) You now have a USB flash drive that can be used to install Debian Linux on most traditional computer systems.This USB flash drive can be used to install other user-friendly distributions
## Starting the Installer In order to install Debian Linux, we need to boot into our [newly created Ventoy flash drive](https://hub.subspace.services/books/software/chapter/creating-a-bootable-usb "Creating a Bootable USB"). Due to a lack of standardization, different hardware will go about this differently.**Disable or unplug any hard drives that will not be used for the operating system.** This includes media, documents, and other data storage.
Most commonly, the boot device can be selected by hitting a specific key while the computer is starting up. [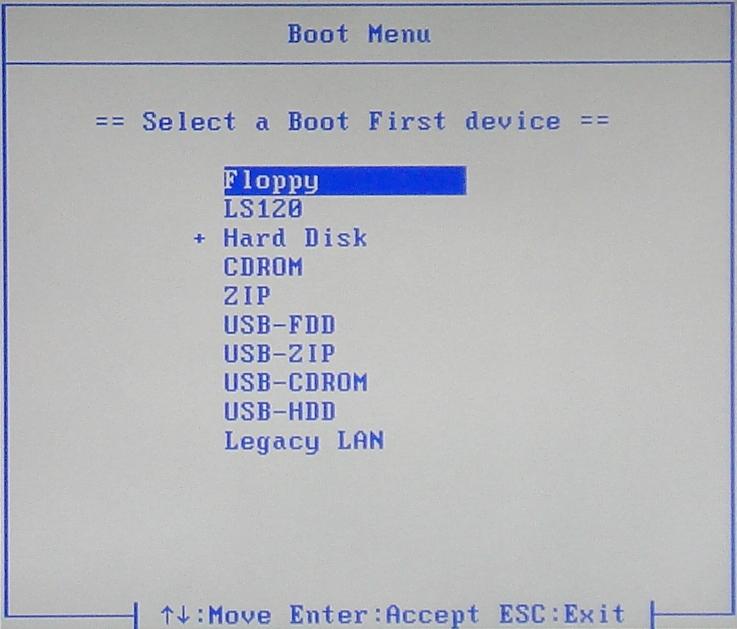](https://hub.subspace.services/uploads/images/gallery/2025-02/1000006167.jpg)Refer to your computer or motherboard manual for more information.
These are some common keyboard commands to enter the boot menu by manufacturer:| **ASRock** | F11 |
| **Asus** | F8 |
| **Acer** | Esc, F9 or F12 |
| **Dell** | F12 |
| **Gigabyte** | F12 |
| **HP** | Esc or F9 |
| **Intel** | F10 |
| **Lenovo** | F8 or F12 |
| **MSI** | F11 |
| **Samsung** | Esc or F2 |
| **Toshiba** | F12 |
Some media keyboards require that you press an FN key located along the bottom row in order to activate the function keys.
Through the Boot Menu, we use the keyboard to navigate down to your USB flash drive. Depending on your system's manufacturer, the boot menu could list your USB flash drive as: - "USB-HDD" - Model Number (i.e. KingstonDT) - Partition Name (i.e. Ventoy)Make sure to boot in UEFI mode if this is presented as an option.
## Installing Debian Linux Once your computer has been booted using the USB flash drive, we should be presented with the Ventoy boot screen. We should only have one option available "debian-12.9.0-AMD64-1" or similar, depending on the current Debian version. Select this option by hitting Enter, then select "Boot in Normal Mode" to begin loading the Debian installer program.**Connect a hardwired Ethernet cable to your server directly from the router.** This is required for automatic updates and driver installation, including your wireless internet card.
The Debian Installer will now ask us the preferred installation method and we will opt to use the "Graphical install." [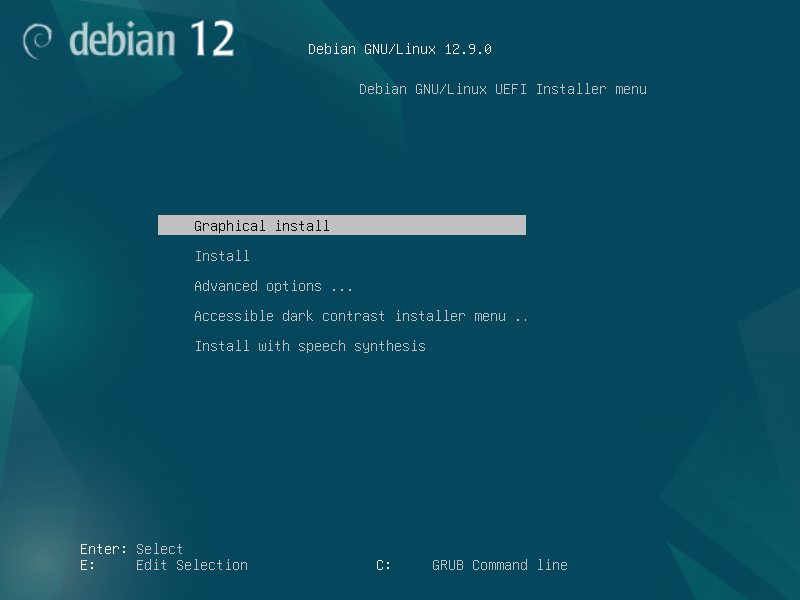](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-11-45.png) We can then select our preferred language, our geographic location, and which keyboard language we want to use.If you are unsure, "Generic 104-key PC" is a good default setting for any keyboard with a Windows key.
After we input this information, the installer will detect your computer's hardware and begin loading the required files for installation. [](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-13-13.png) Once this is finished, we'll be asked to configure our network connection. We will be using LAN which requires your computer to be hardwired to your router with an Ethernet cable. The Debian installer should automatically get an IP address and connect to the internet. [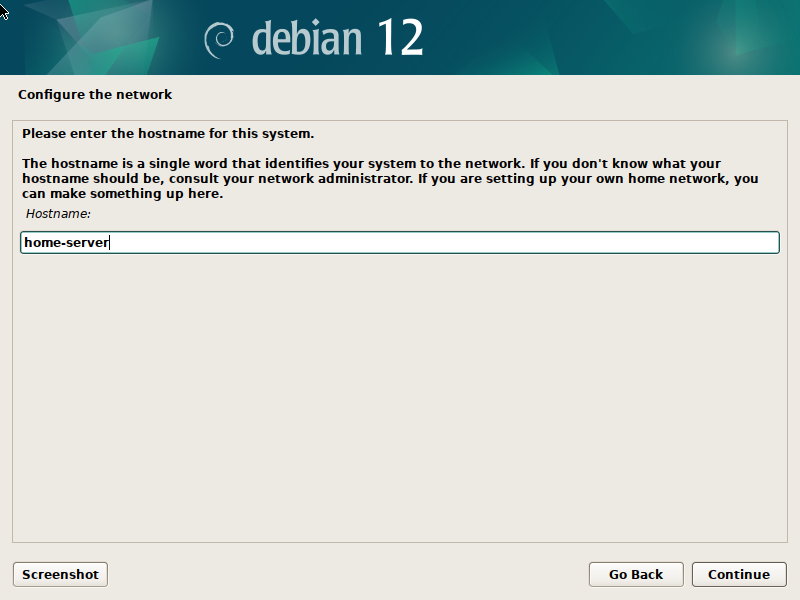](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-17-00.png) We can set the **Host Name** for our server, which affects how it is identified on the local network. Choose a name that is meaningful to you, or simply name it "home-server". Additionally, we can leave the **Domain Name** blank. [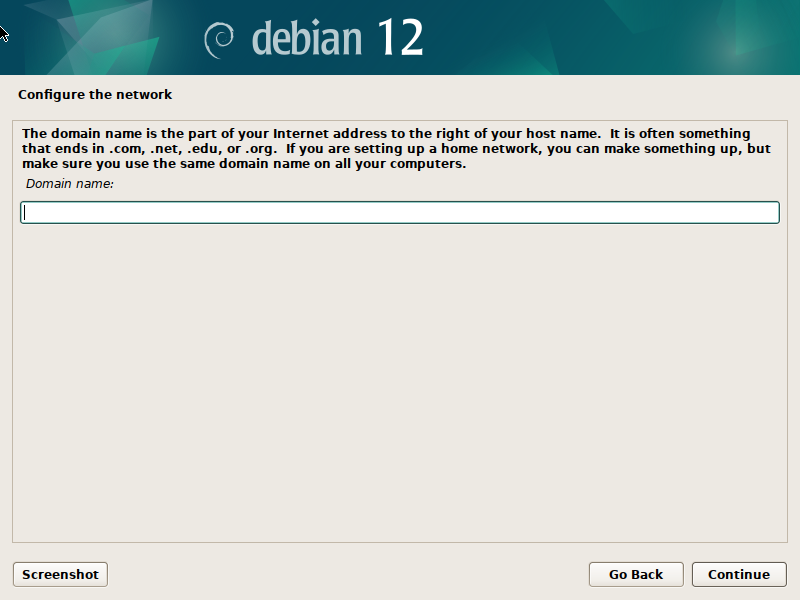](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-17-33.png) Next, we will set a password for the Root account, which is the most powerful account on the server that has direct access to and control over all system functions. [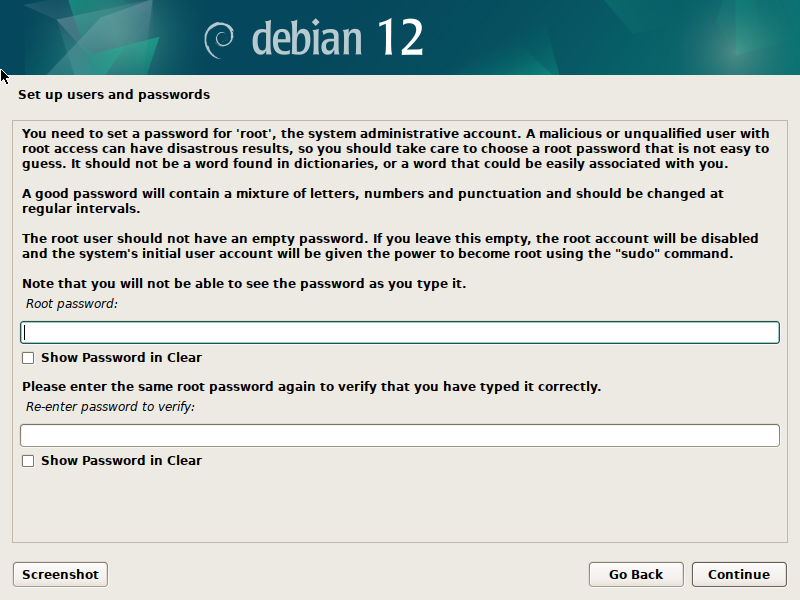](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-18-02.png)We recommend using a password you've never used before that contains letters, numbers and special characters. Store this password in a secure place.
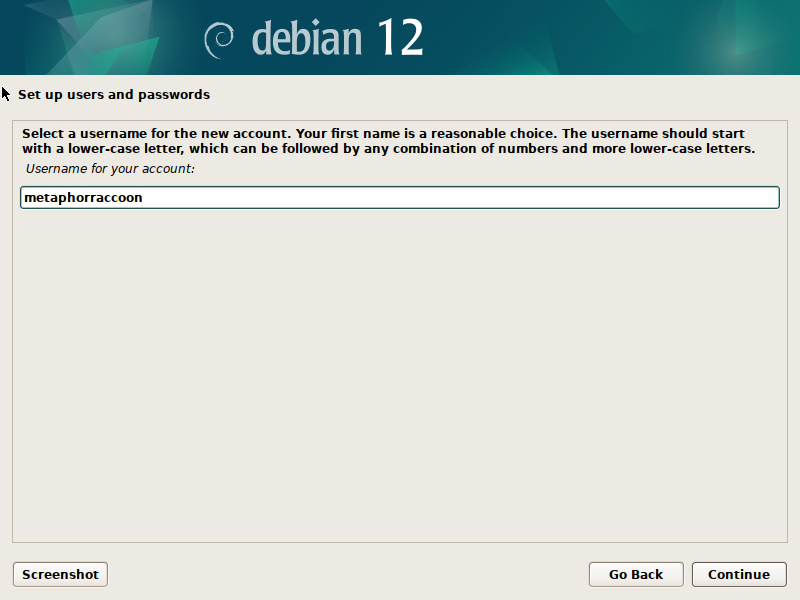
After the **Root** account is secured, we can make our user account. This profile will have fewer access privileges by default to increase server security. As needed, we can log in as Root to do server administrative tasks. Enter your full name, or the friendly name displayed during login, as well as an account user name. On the next page, we can choose and verify this user account's password.We recommend using a different password for your user and root accounts for increased security.
[](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-20-46.png) Once our accounts are finalized, we can choose our server's time zone. [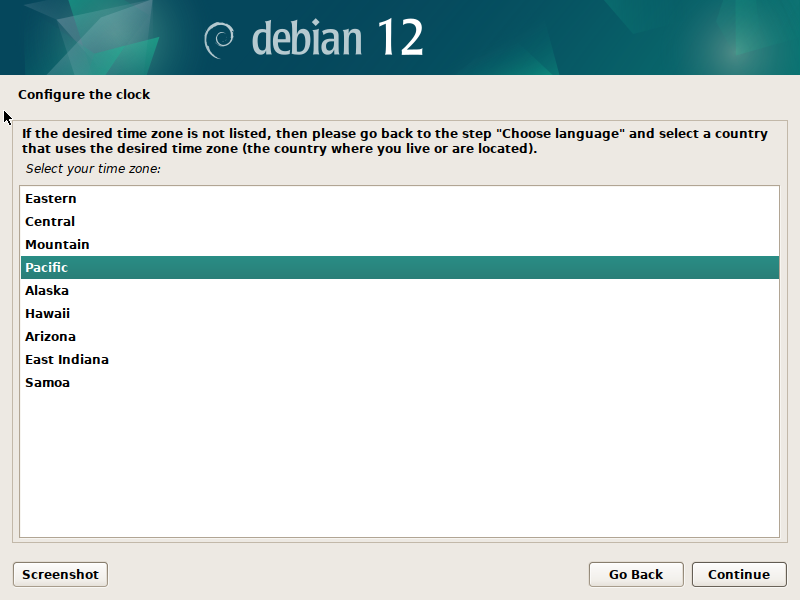](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-22-24.png)**Ensure all non-system hard drives are physically disconnected.** This includes media, documents, and other data storage.
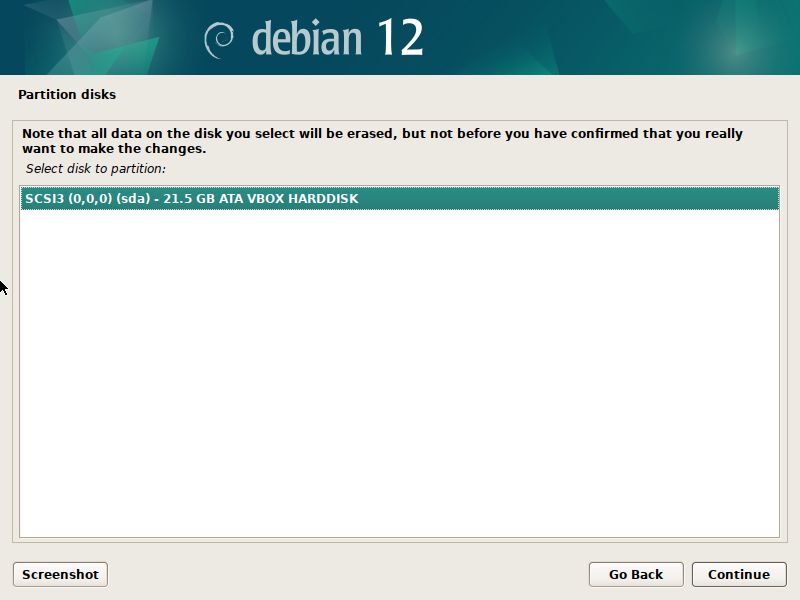
Next, we will need to begin setting up our storage drives for an operating system. The Debian installer will detect any hard drives available in your system. [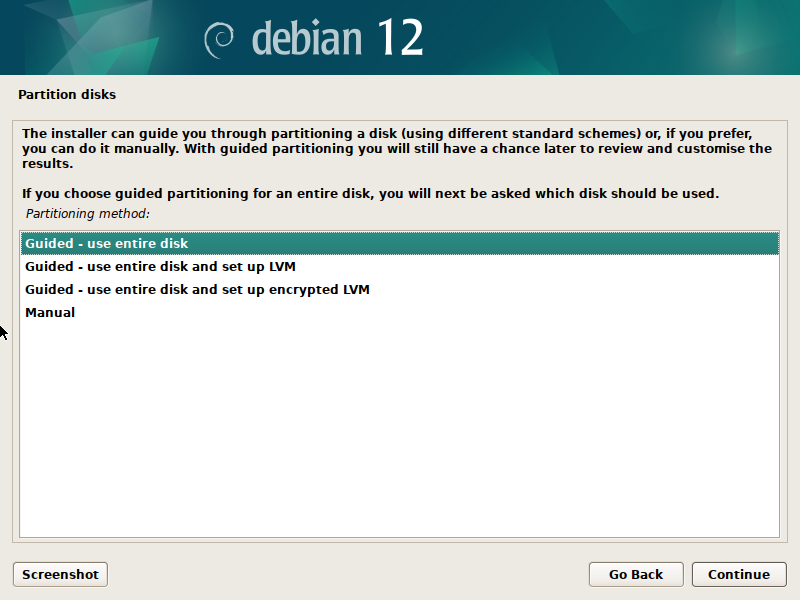](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-23-01.png) We will be choosing "Guided - Entire disk" which will reformat the entire drive for use by the Linux operating system. There should only be one disk available because we disconnected the others.**We are erasing the selected disk.** Always make sure you have backed up all important files from this drive.
[](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-24-24.png) Once we confirm we will installing Debian on this disk drive, we will be asked how we want to partition the drive. We will select "Contiguous - all files in one partition" for simplicity. This is what Debian recommends for users who are new to Linux-based operating systems. [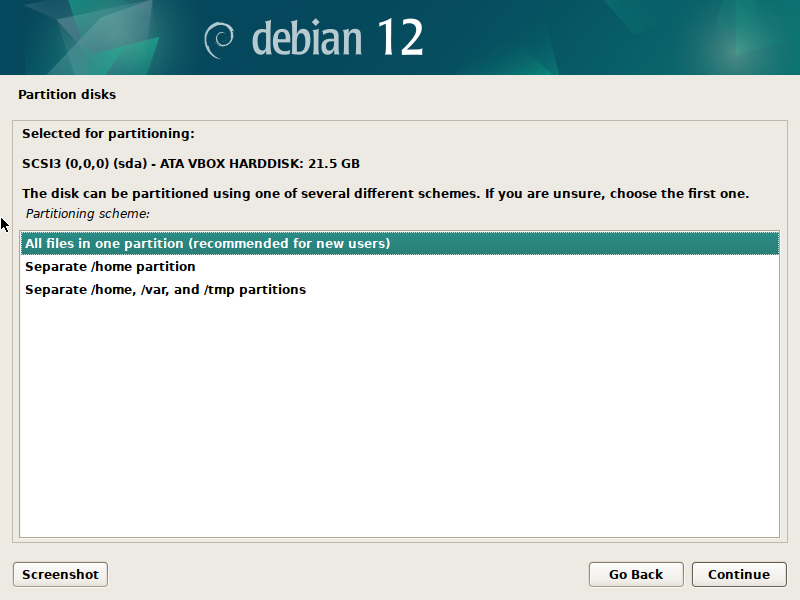](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-26-29.png) Once we hit Continue, we will be given a quick overview of the changes being made. We should have three partitions being created on the hard disk. [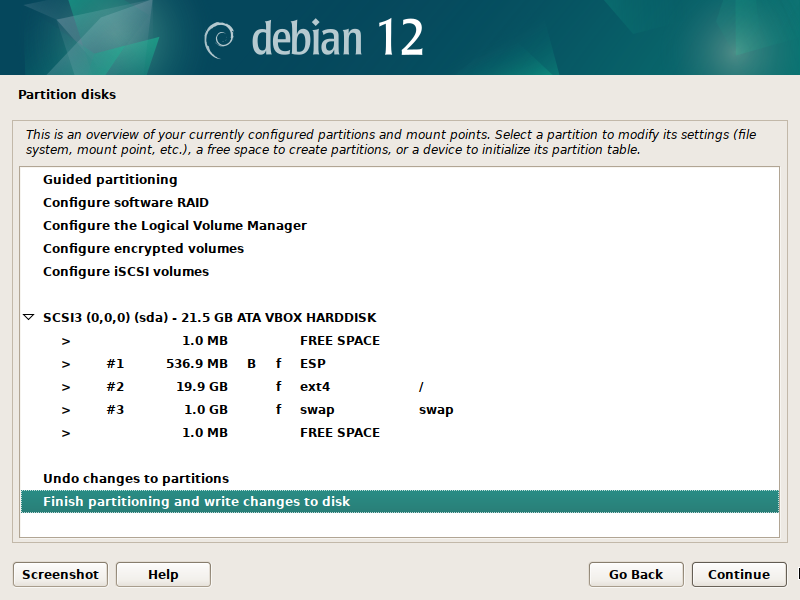](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-28-33.png) After we select Continue, we will be given one final warning about the changes being written to our disk. You will need to select 'yes' before you can move on to the next step. [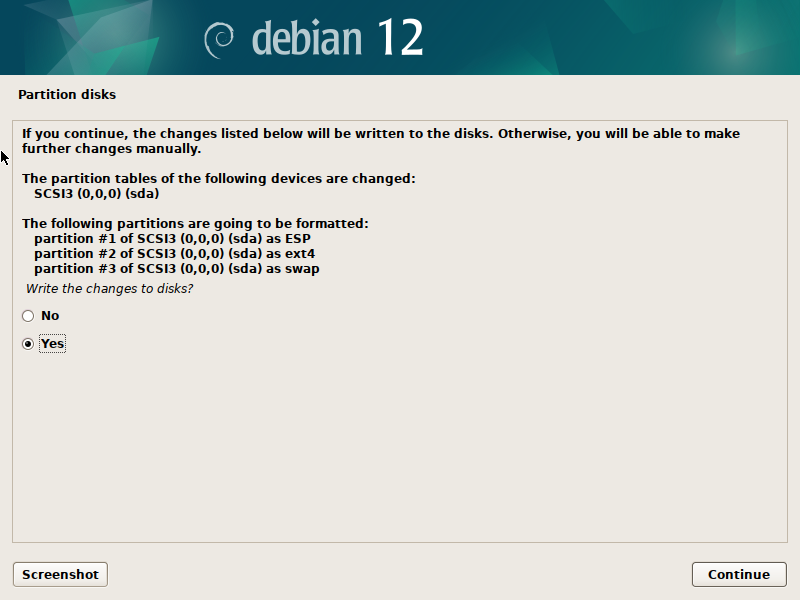](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-29-57.png)**Final Warning** Hitting Continue will erase your drive.
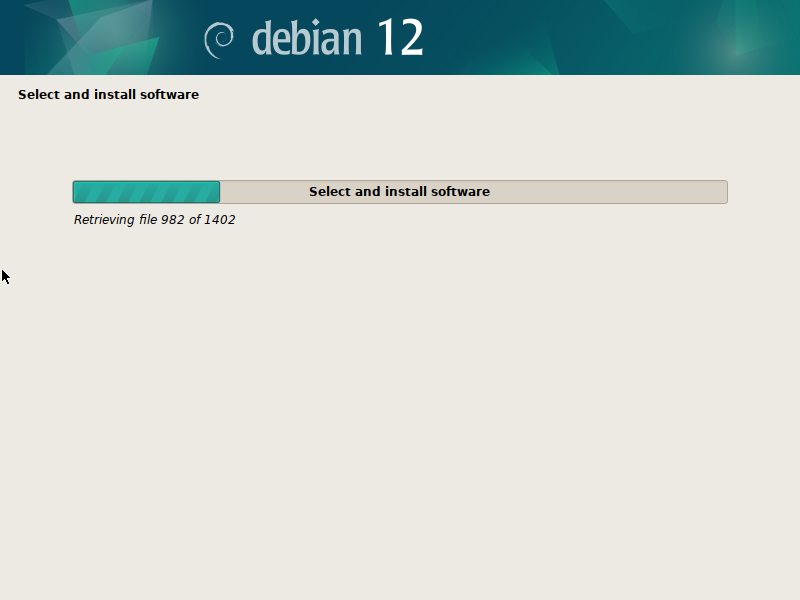
Debian will format your hard drive and begin to install the base operating system on it. [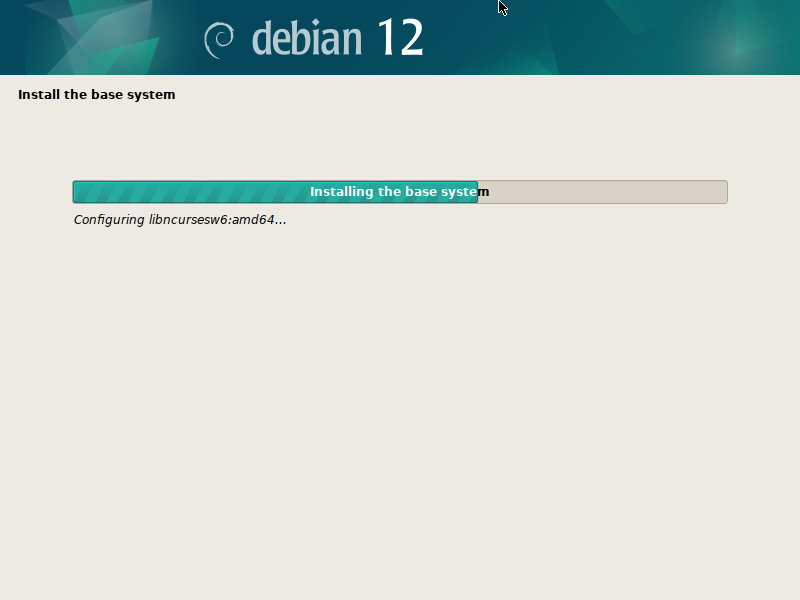](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-30-40.png) You will receive a prompt about configuring the package manager. This is because we are installing from a USB flash drive and we have the option to load additional installation files from another disk. We will select 'no' and continue. [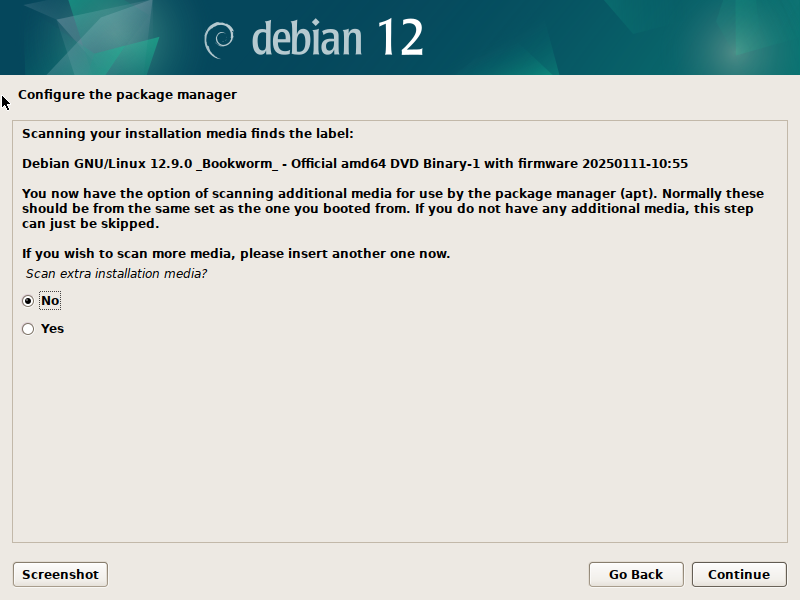](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-34-17.png) On the next page, we can choose to use a network mirror. [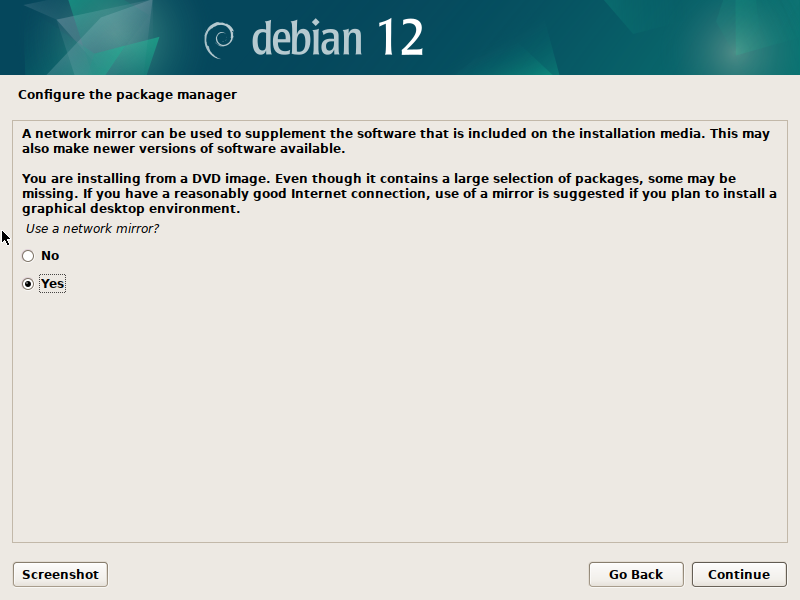](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-34-50.png) It can improve update download speeds by retrieving them from a server closer to your location. This mirror will also be used to download software updates during the install process. Select 'Yes'. [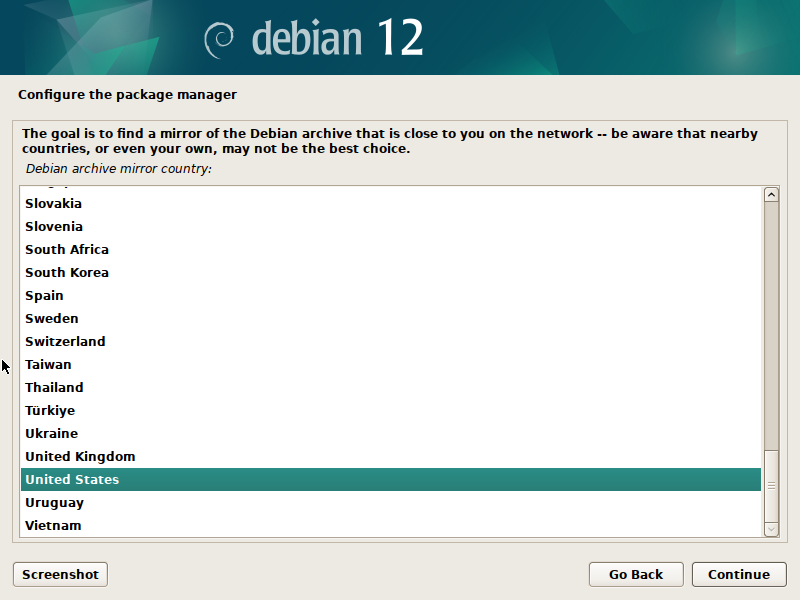](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-38-35.png) Select your country and hit 'next'. From here, we can safely choose the network mirror listed at the top. [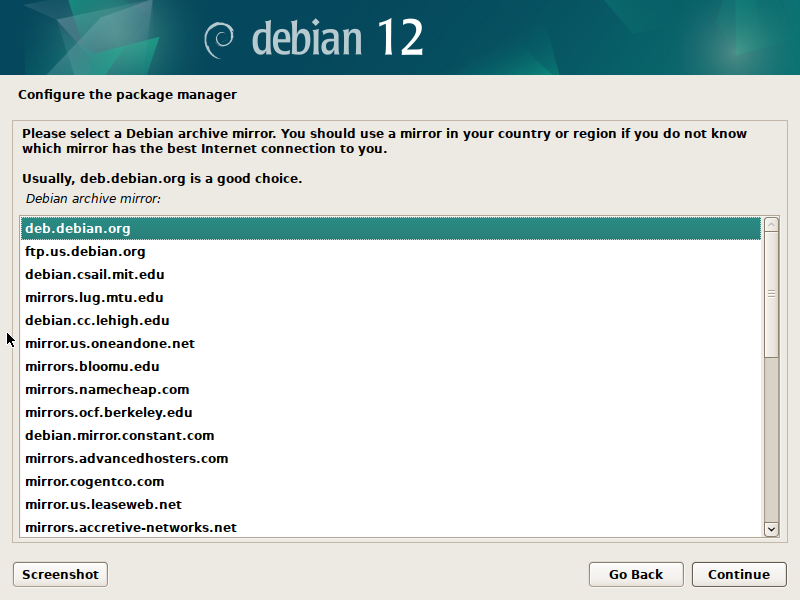](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-43-13.png) Hit 'continue' and you will be asked about an HTTP proxy. We can leave this empty and hit 'continue' again. [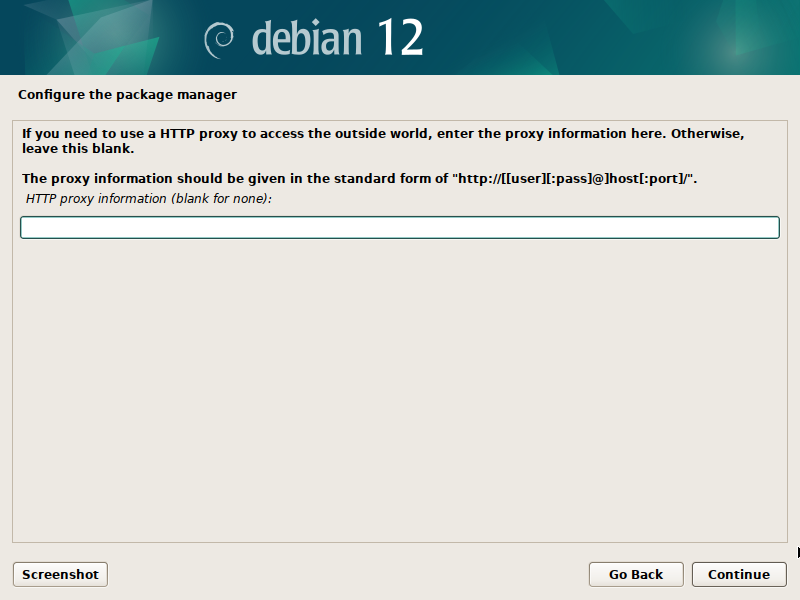](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-44-17.png) The Debian Installer will select software to install and being the process of retrieving updates from the internet as required. [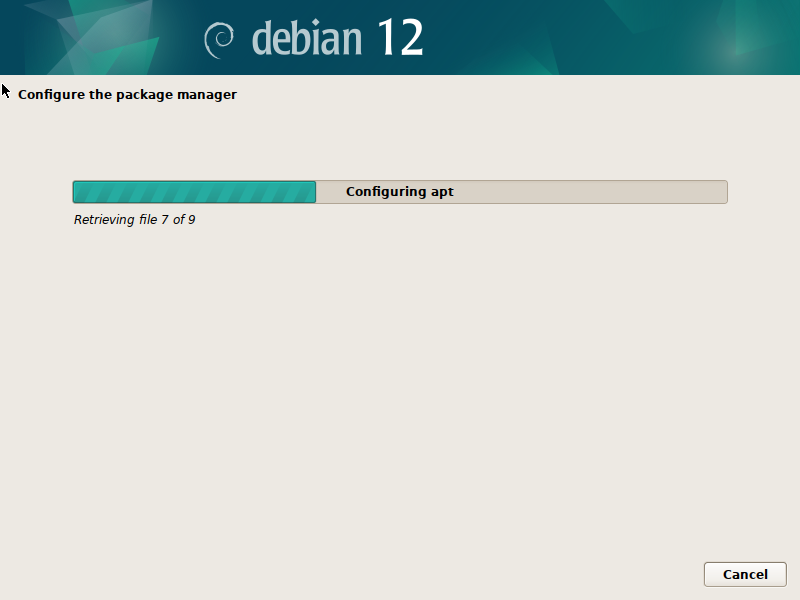](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-49-13.png) Next, we can choose to opt-in to the "[popularity contest](https://popcon.debian.org/)" which periodically returns anonymized software install and usage metrics to Debian for use by developers. [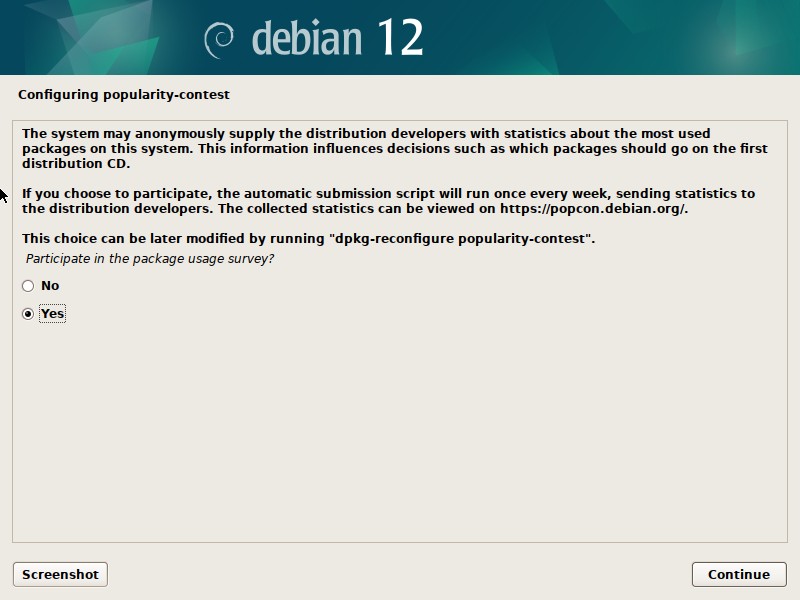](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-50-42.png) Finally, we will be choosing our Desktop Environment. This operating system can act as the foundation for many different Desktop Environments which control the user interface and experience. This is a matter of personal preference that can affect which software is installed by default. For simplicity sake, we will use the default Desktop Environment and select Gnome. On this last screen, we can also choose to install SSH to allow for remote access. We will chose to install it and save a step later. [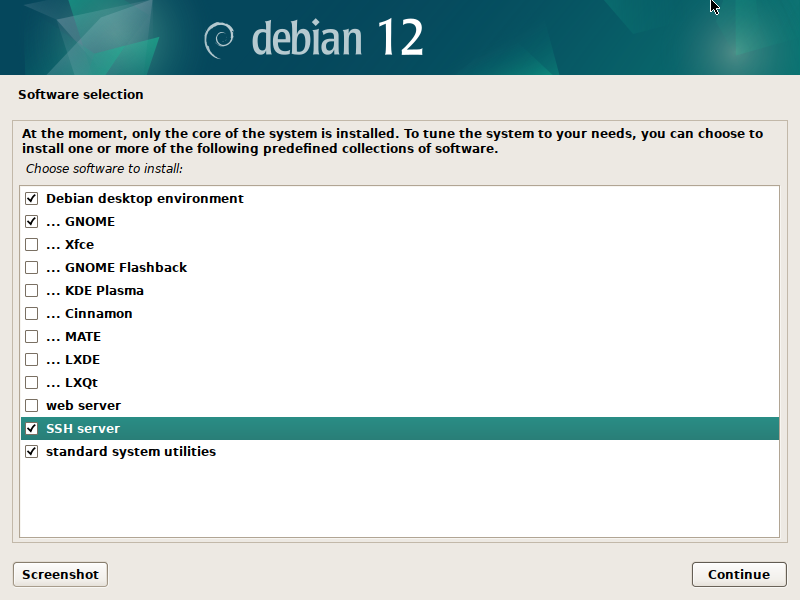](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-51-45.png) We can hit 'Continue' one final time now that everything is configured.Debian will begin the installation process.
[](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-52-45.png) If you are using a BIOS motherboard that doesn't support UEFI, you may have an additional step asking where to install the GRUB bootloader. Select 'Yes'. [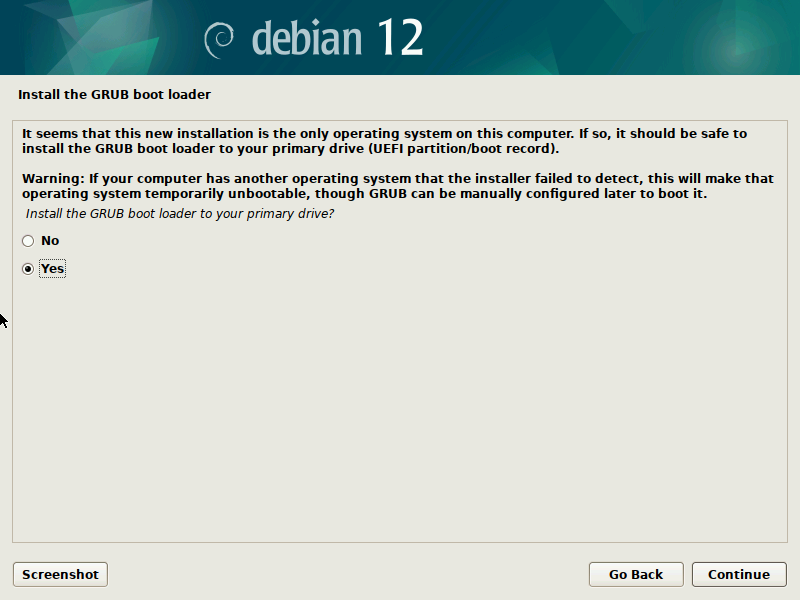](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-plasma-02-04-2025-12-45-31.png) You should select the same storage drive as you installed Debian. This should be the only storage drive listed. [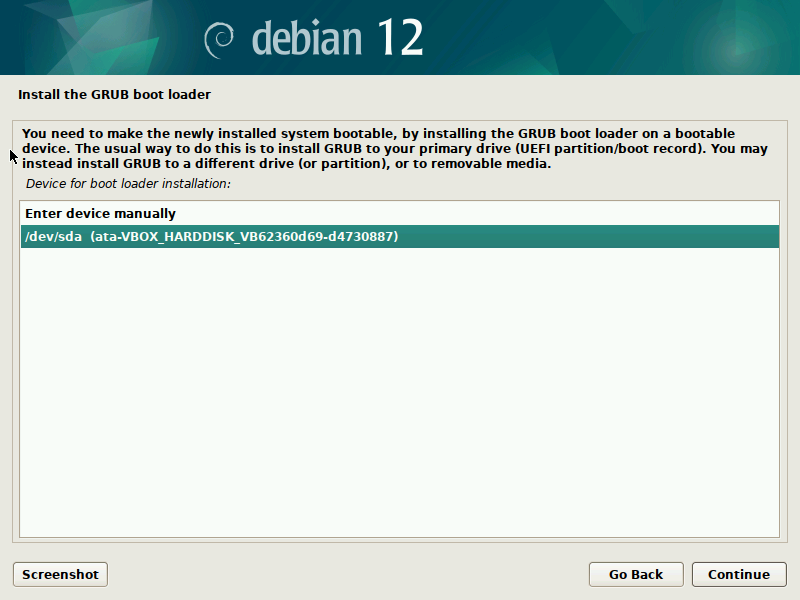](https://hub.subspace.services/uploads/images/gallery/2025-04/virtualbox-plasma-02-04-2025-12-46-22.png) Once the files are copied, the installer will tell us to remove the USB flash drive before restarting the computer to finish the installation. [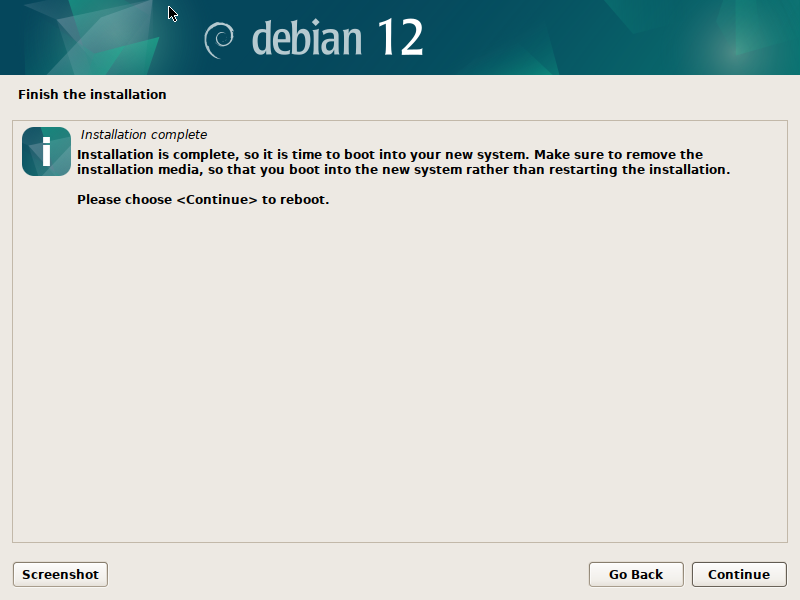](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-17-59-33.png) ## Finalizing Installation Once the computer has started, we should be able to see the GRUB boot loader. After five seconds, it will automatically boot into the Debian operating system. [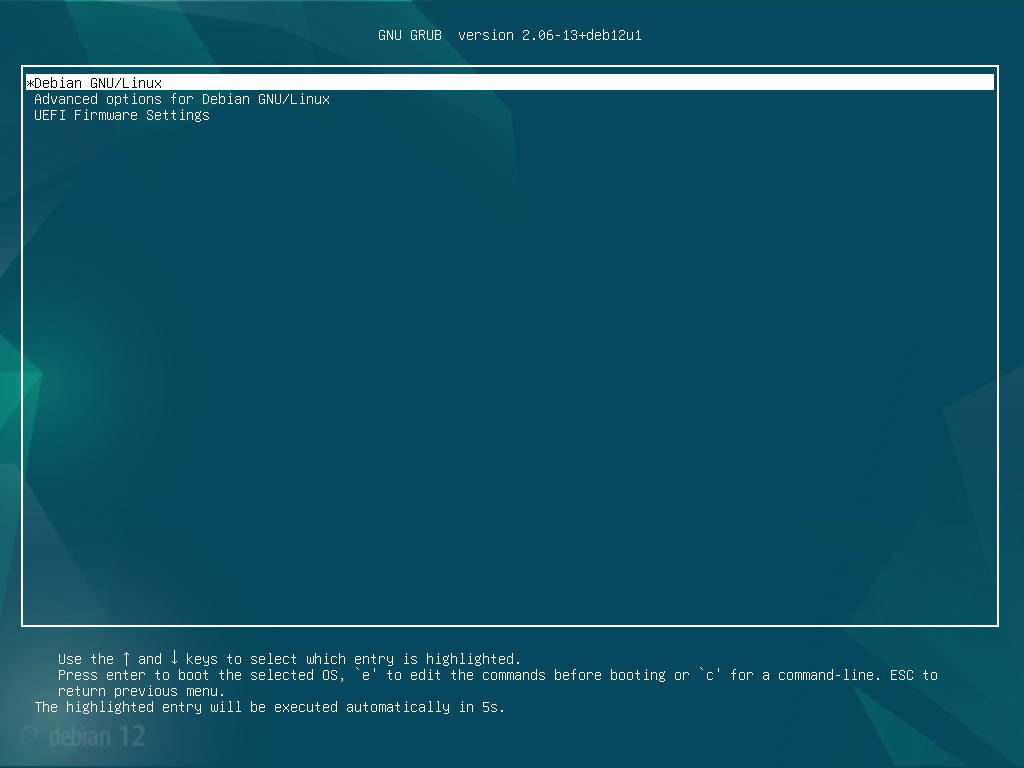](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-18-00-28.png) Now, we need to login with the user account and password we set up during the installation. [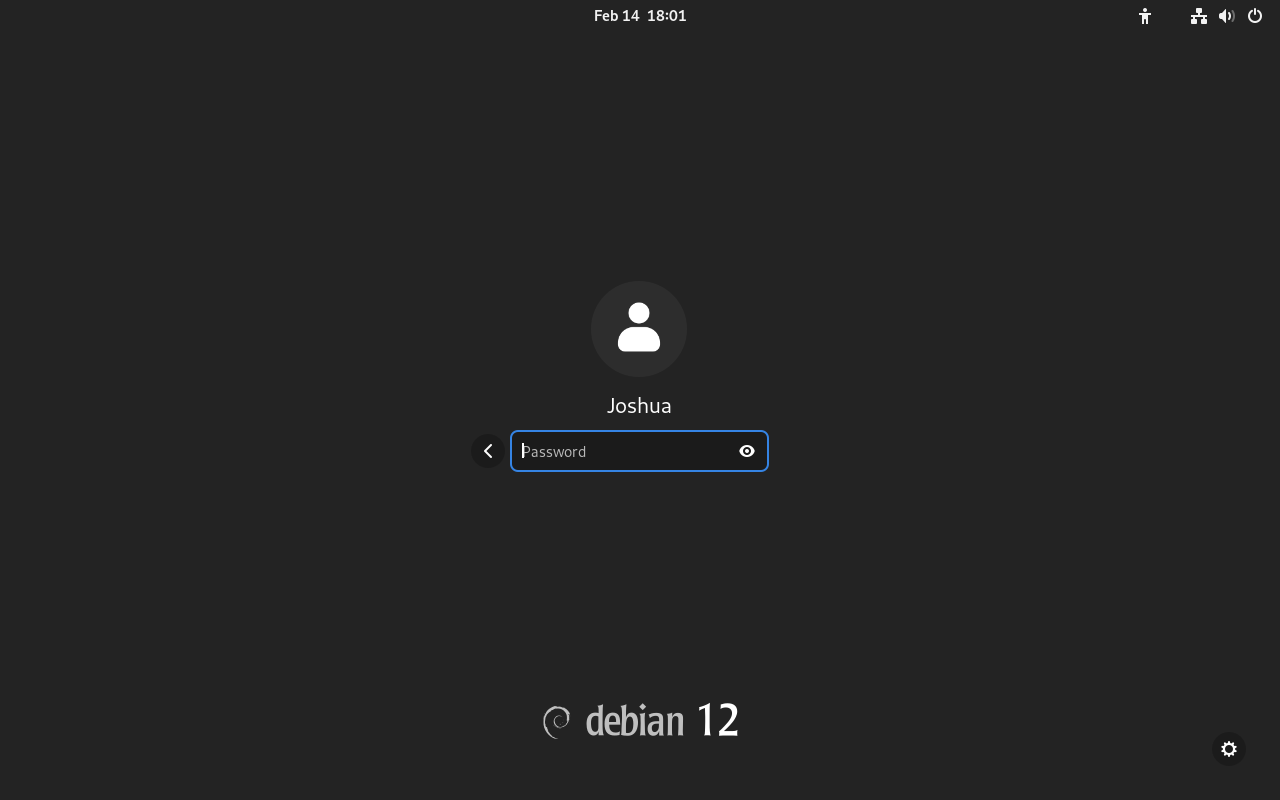](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-18-01-46.png)You cannot access the root account through this login screen.
After logging in, we will be greeted with the welcome screen for our user account setup process. [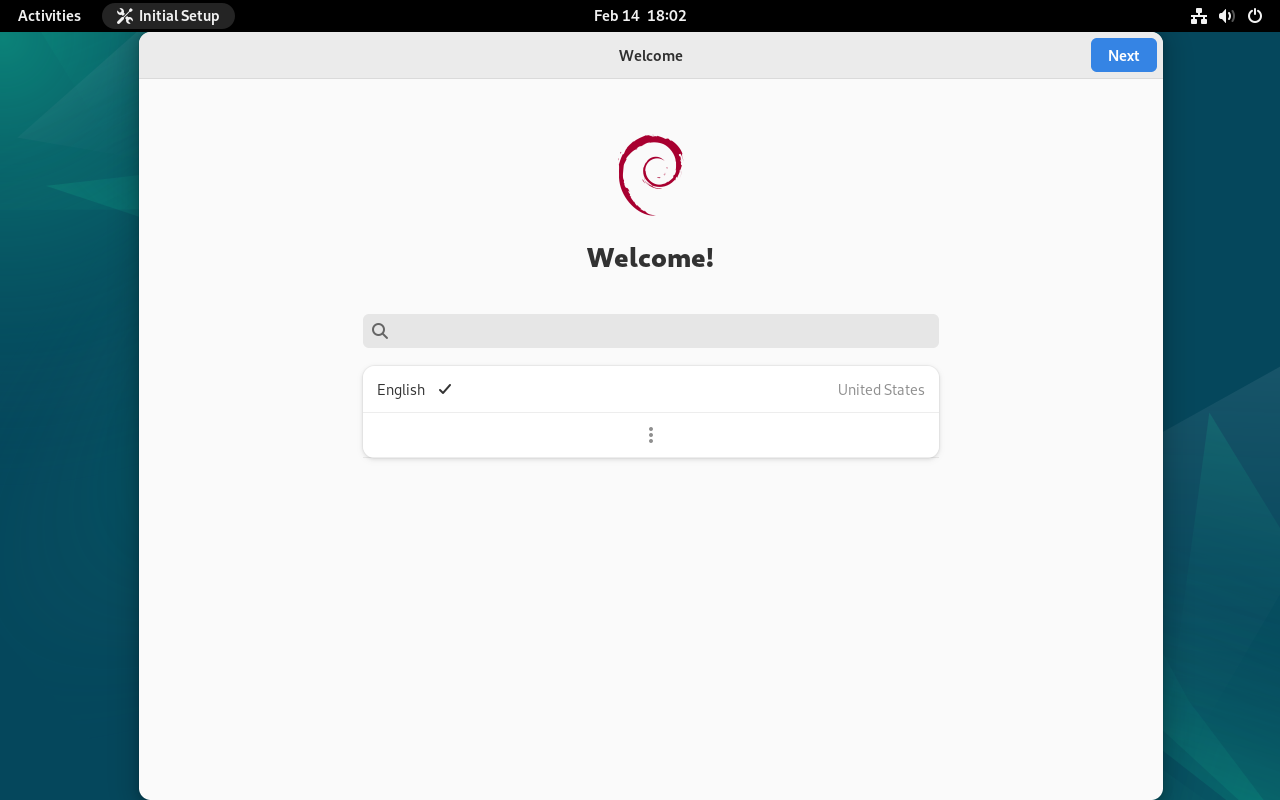](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-18-02-23.png) We can select our keyboard language settings. [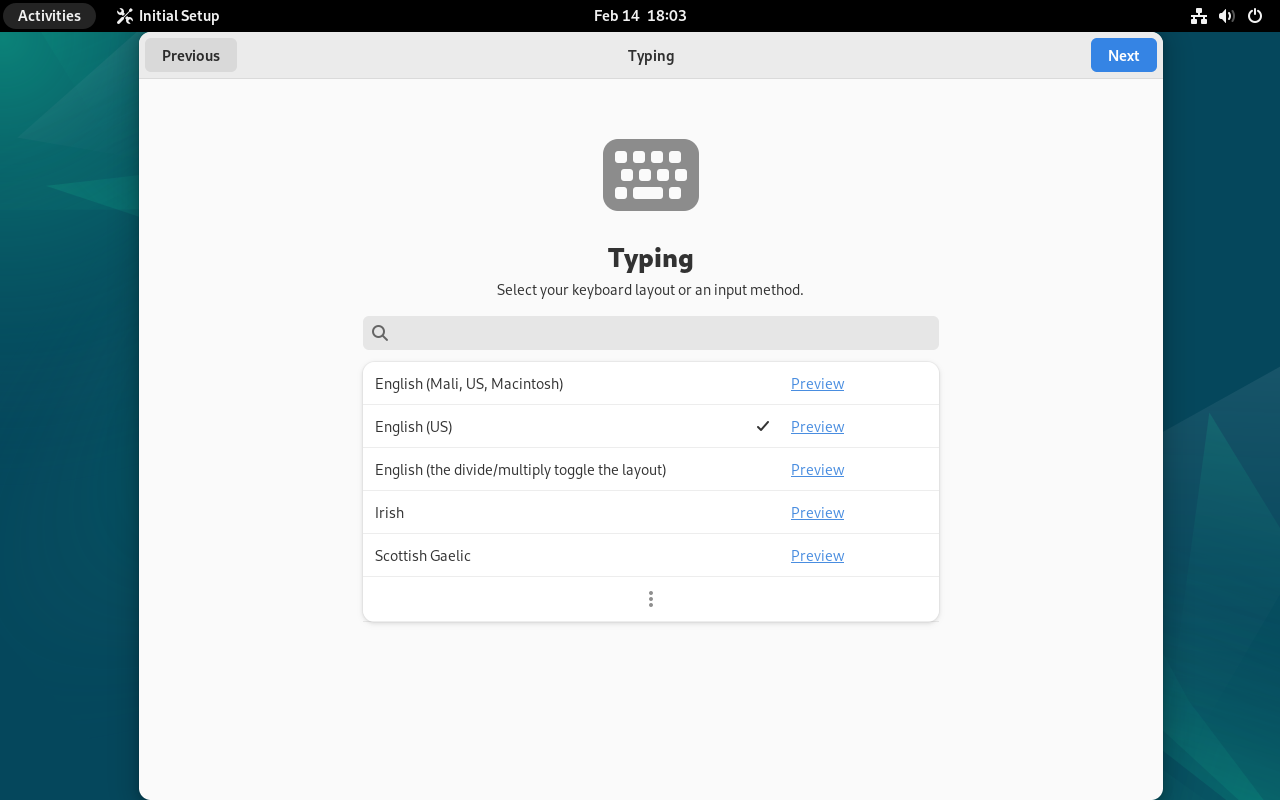](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-18-03-10.png) We can also choose to leave "Location Services" enabled, or disable it for increase privacy. [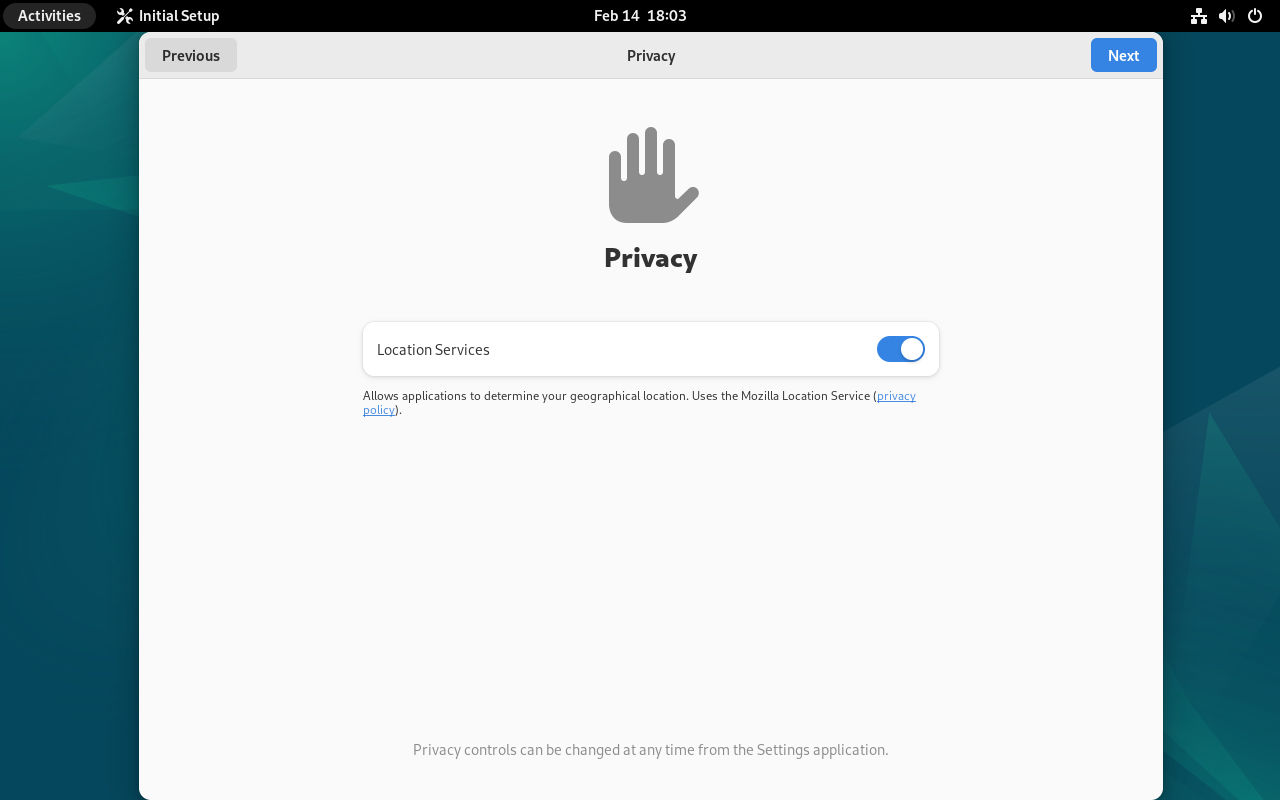](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-18-03-47.png) We will be asked to login to our online accounts, but we can skip this. [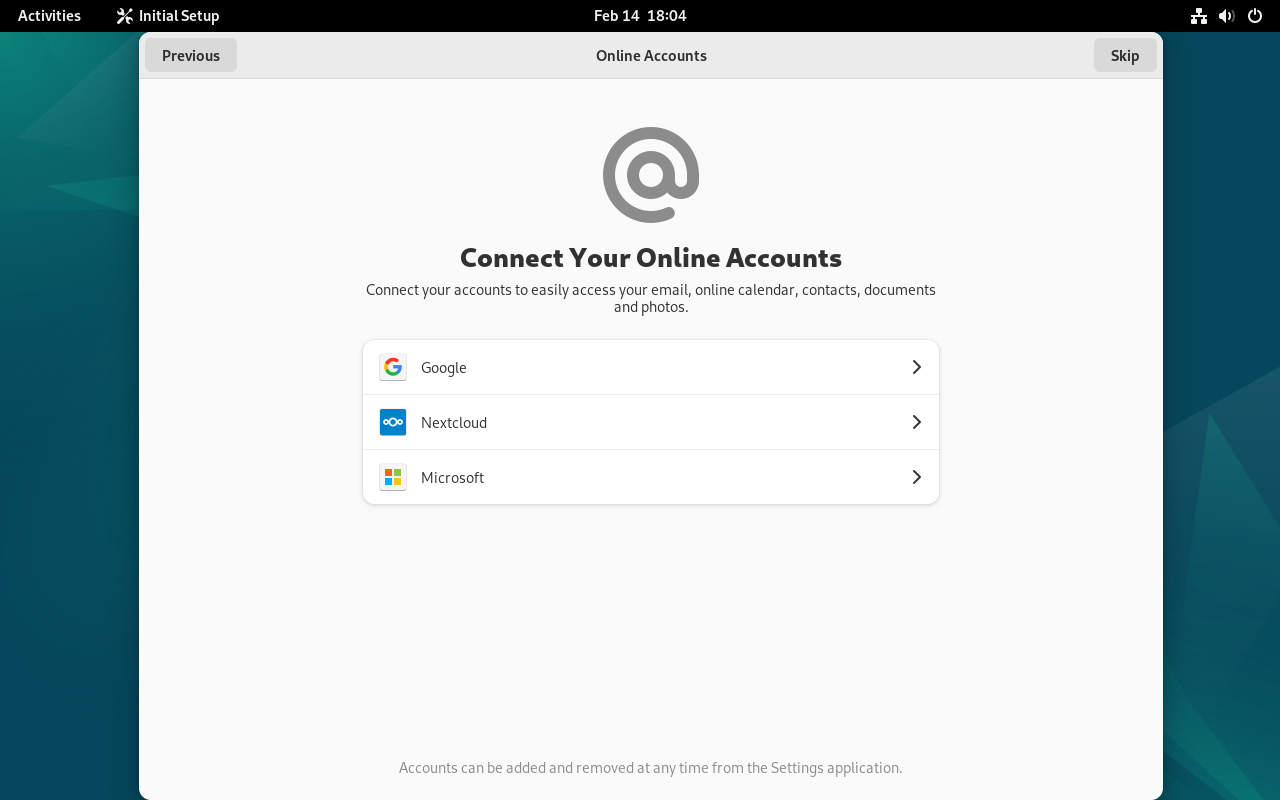](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-18-04-57.png) We can now start using Debian and installing the software necessary to host a home server. [](https://hub.subspace.services/uploads/images/gallery/2025-02/virtualbox-debian-14-02-2025-18-05-23.png) [](https://hub.subspace.services/books/software/chapter/configuring-debian "Next Steps") # Single-Board Computers Raspberry Pi computers use an SD card that needs to be "flashed" with an operating system. This process writes files to the SD card while it's connected to a Windows, MacOS or Linux machine through a USB connection. [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000274.jpg) ## Raspberry Pi Imager This is the official Raspberry Pi solution for flashing image files to the SD card, which is an integral part of the microcomputer ecosystem. This also allows you to quickly configure Raspberry Pi OS, such as configuring Wi-Fi, changing the computer's host name, and enabling SSH for remote access. By default, Wi-Fi and Bluetooth are enabled.You can download [Raspberry Pi Imager](https://www.raspberrypi.com/software/) from their website.
First, you will need to install the Raspberry Pi Imager. [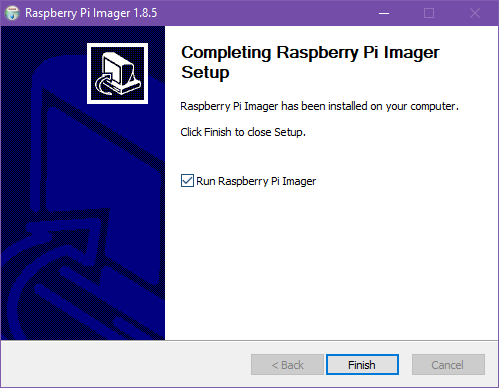](https://hub.subspace.services/uploads/images/gallery/2025-02/y9dimage.png) Once the install process is completed, you can open the Raspberry Pi Imager software.You will be prompted for administrator access to the computer.
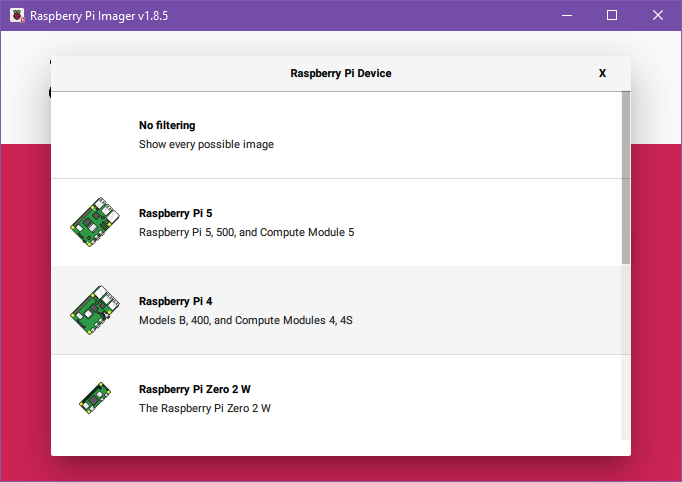
[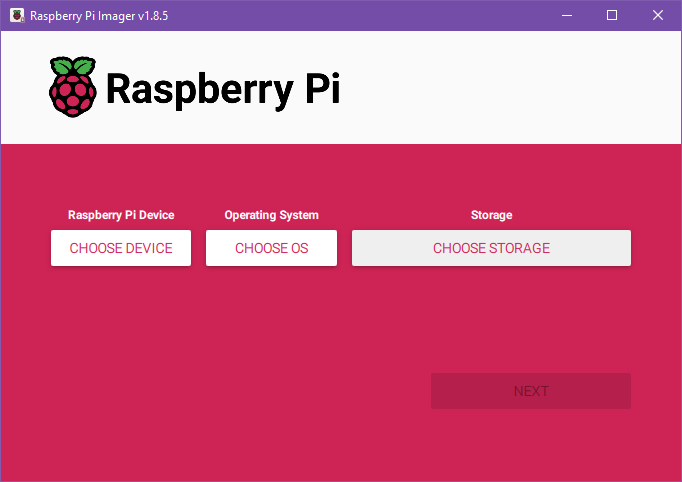](https://hub.subspace.services/uploads/images/gallery/2025-02/w8gimage.png) Now we can attach our MicroSD card to the computer using a USB to MicroSD card adapter. Once we have connected the drive, we can click "Choose Device" to model of Raspberry Pi we are using. [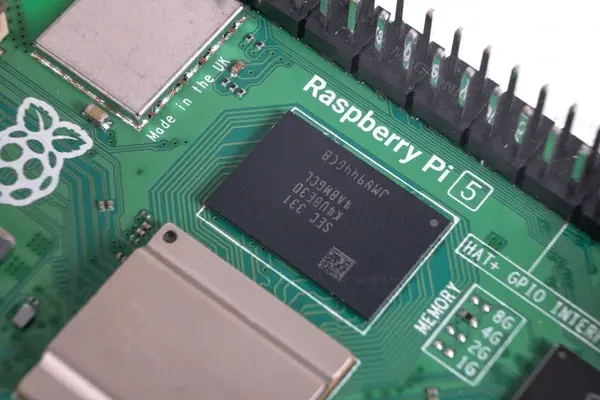](https://hub.subspace.services/uploads/images/gallery/2025-02/raspberry-pi-5-isolated-on-600nw-2389181747.webp) Be sure to select your correct model for best performance. If you are unsure, the model number is printed on the board itself below the GPIO pins.[Raspberry Pi Official installation video](https://www.youtube.com/watch?v=ntaXWS8Lk34)
[](https://hub.subspace.services/uploads/images/gallery/2025-02/q60image.png) With our model selected, we can move on to selecting our operating system. [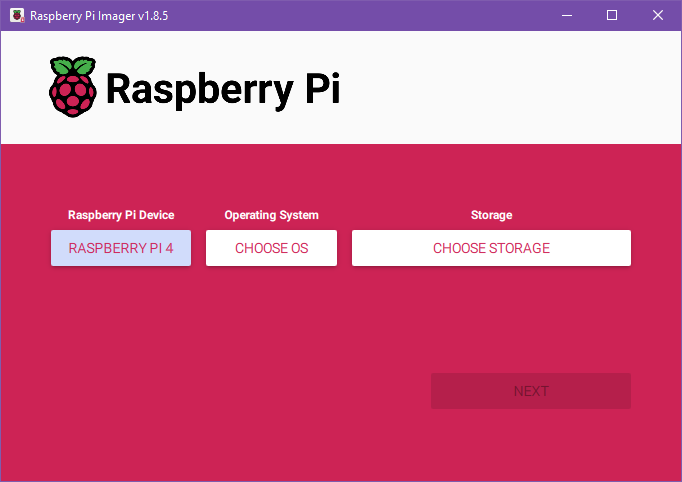](https://hub.subspace.services/uploads/images/gallery/2025-02/9Ojimage.png) We will be using the recommended Raspberry Pi OS (64-bit). Some services do not work on the Raspberry Pi using a 64-bit operating system and this will require using the 32-bit edition, but this should be avoided if not required. [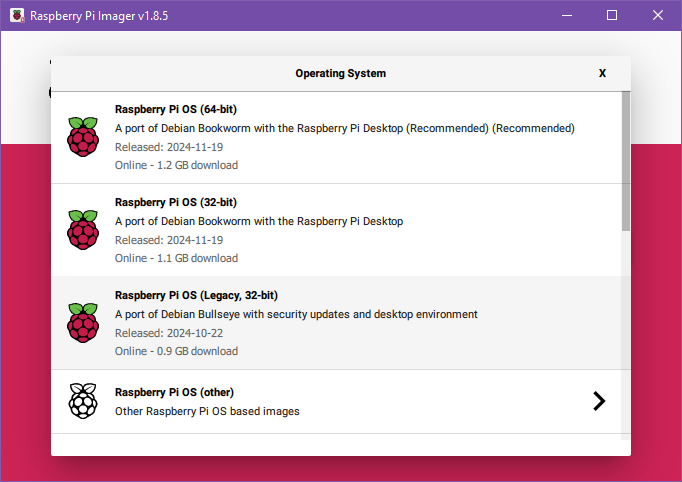](https://hub.subspace.services/uploads/images/gallery/2025-02/2Bximage.png) Finally, we can select the storage device we want to install our operating system. This is the USB to MicroSD card adapter we plugged in. The Raspberry Pi Imager will hide system and internal hard drives. We will select our USB drive. [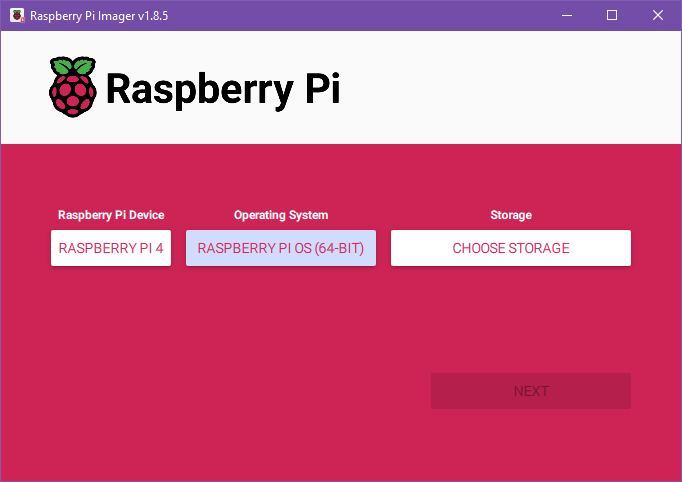](https://hub.subspace.services/uploads/images/gallery/2025-02/5KGimage.png) Depending on how your MicroSD card is formatted and how many devices you have plugged in, this screen may look different. Verify that you are selecting the correct drive. [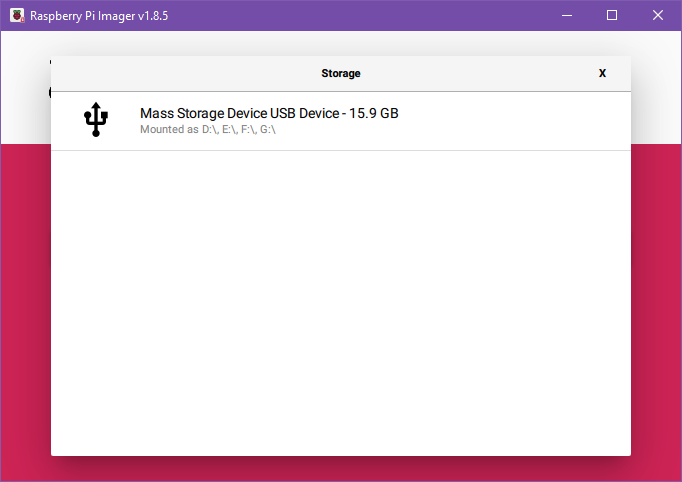](https://hub.subspace.services/uploads/images/gallery/2025-02/wloimage.png)This process will irrevocably erase the data on this SD card. Ensure all important data has been backed up first.
Once our SD card is selected, we can hit "Next" to begin the configuration process. We will be presenting with a pop-up asking us if we want to apply OS customization settings. Select "Edit Settings". [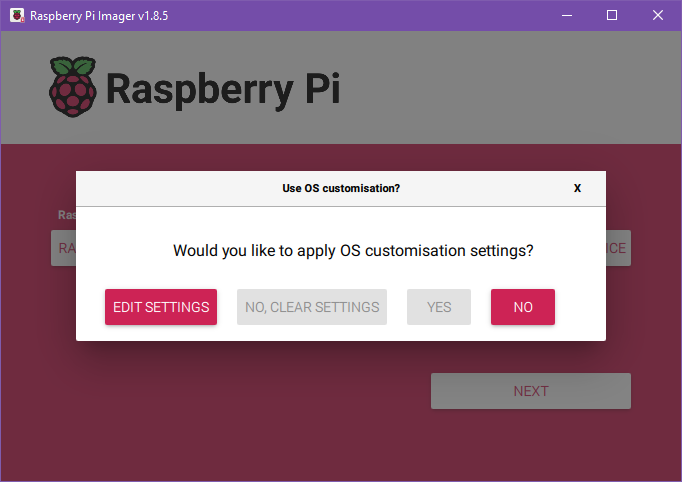](https://hub.subspace.services/uploads/images/gallery/2025-02/VxWimage.png) First, we will need to configure general settings. Our "hostname" signifies how our server will report itself to the local network. Next, we will need to set our username and password. We will not be using Wi-Fi for our server, so we can leave this section blank. Optionally, we can also set the time zone and keyboard layout to use. [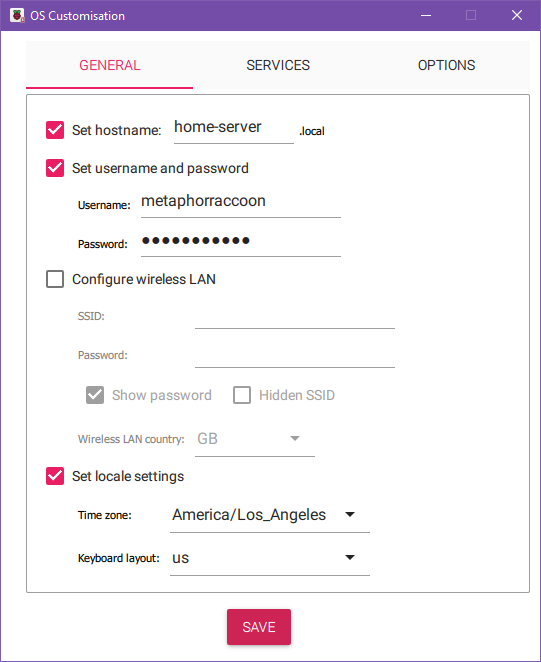](https://hub.subspace.services/uploads/images/gallery/2025-02/ZR9image.png) Under the Services tab, we will be enabling SSH. We can leave this with the default setting to "Use password authentication". [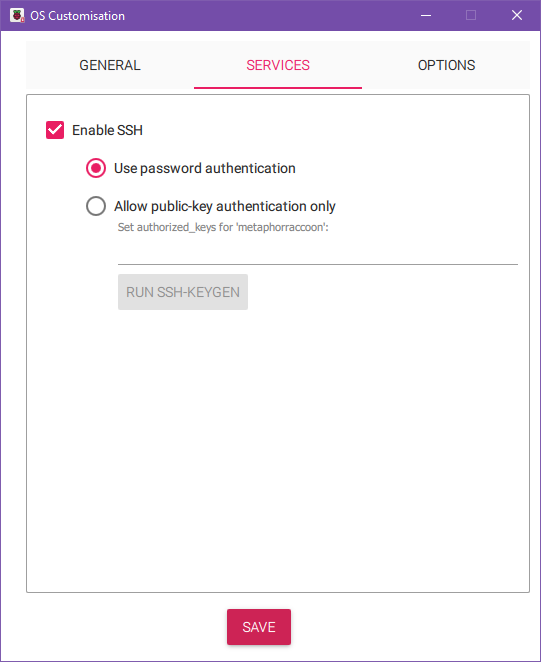](https://hub.subspace.services/uploads/images/gallery/2025-02/wY9image.png) Now, we can hit save to commit these settings. Now, we can hit 'Yes' to proceed with the installation process. [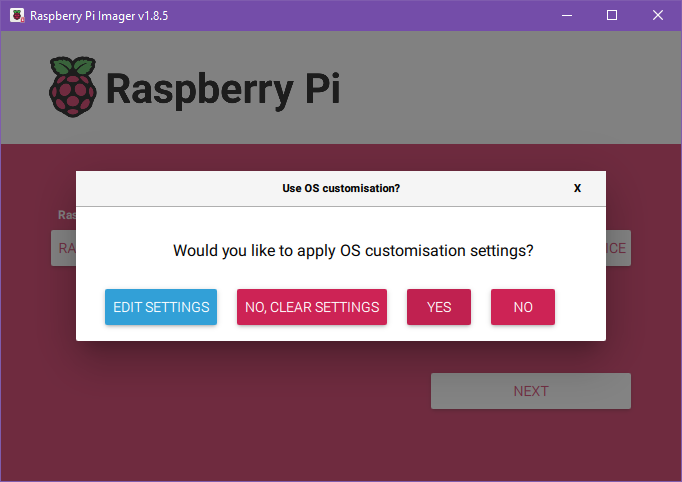](https://hub.subspace.services/uploads/images/gallery/2025-02/EN2image.png) The Raspberry Pi Imager will warn us that all existing data will be erased. If you are sure that this drive can safely be erased, press 'yes' to continue. [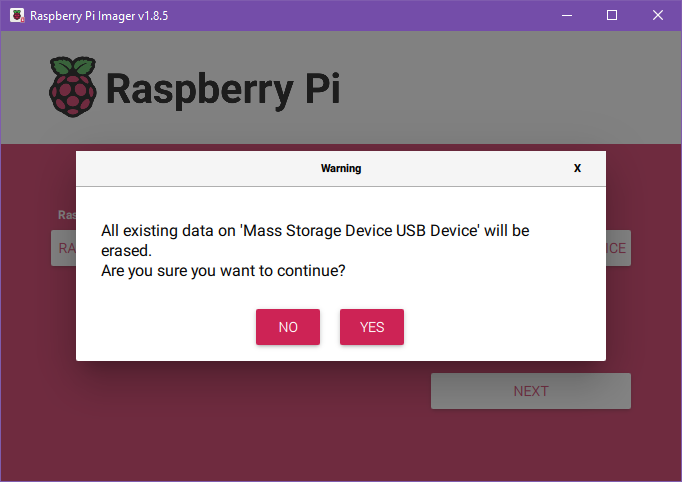](https://hub.subspace.services/uploads/images/gallery/2025-02/v38image.png) This will begin the installation process where the drive is formatted and the appropriate files are copied to the MicroSD card. [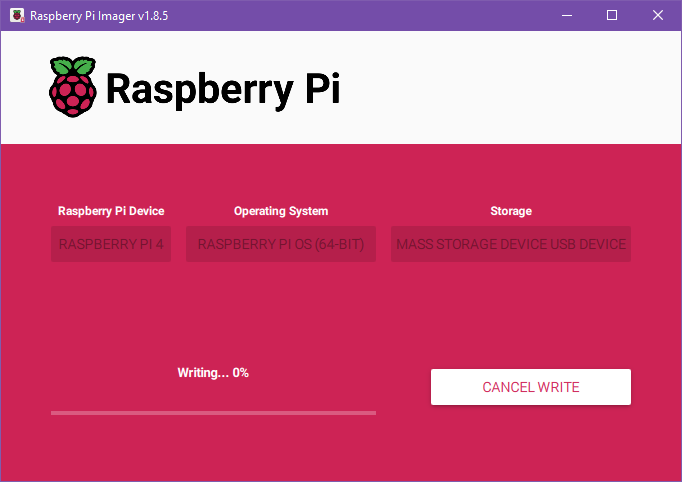](https://hub.subspace.services/uploads/images/gallery/2025-02/zsKimage.png) After the files are copied, the Imager will verify that the files were copied correctly and they were not corrupted. [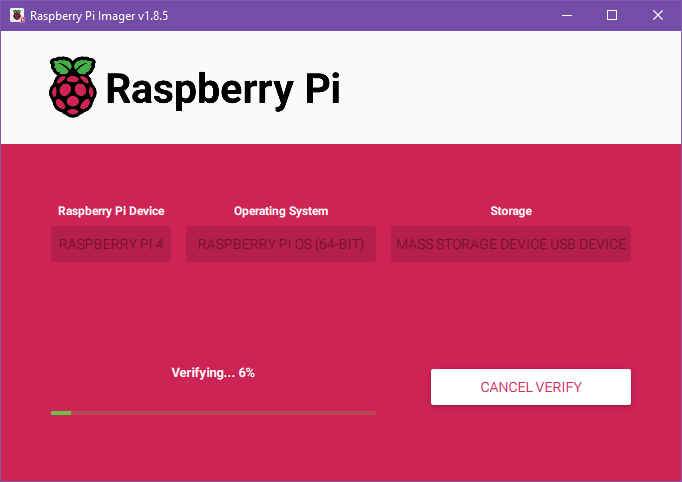](https://hub.subspace.services/uploads/images/gallery/2025-02/HRuimage.png) Once it is finished verifying, we will be alerted that we can remove the MicroSD card by disconnecting the USB adapter. [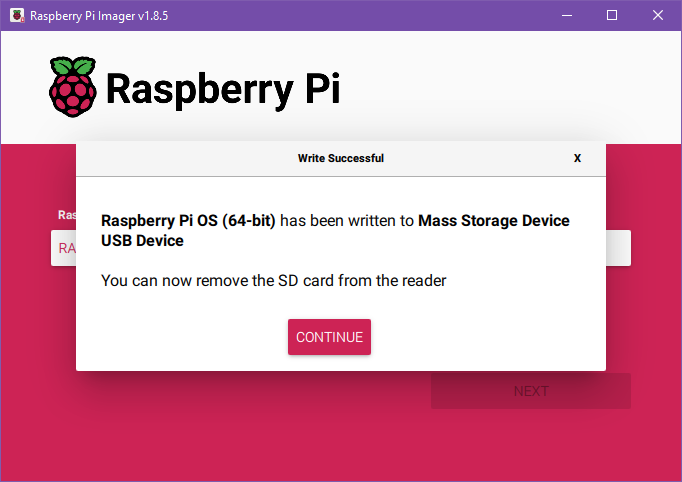](https://hub.subspace.services/uploads/images/gallery/2025-02/8PQimage.png) Now, we can put the MicroSD card into the Raspberry Pi and power it on to begin configuring our operating system. [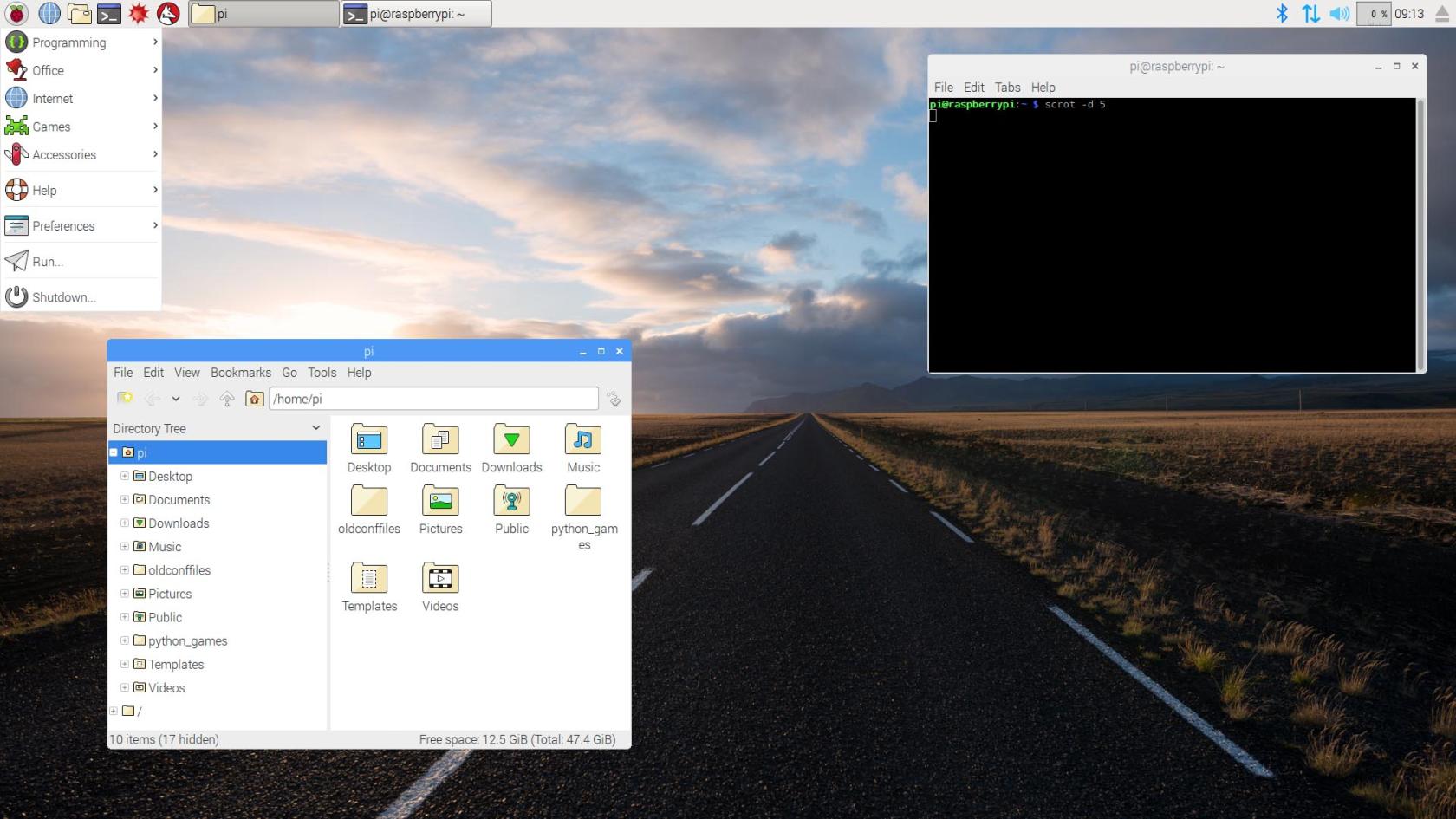](https://hub.subspace.services/uploads/images/gallery/2025-02/newdesk.jpg) [](https://hub.subspace.services/books/software/chapter/configuring-debian "Next Steps") # Configuring Debian We need to make some adjustments to the underlying operating system. # Repositories If you have the [USB flash drive we created to install Debian](https://hub.subspace.services/books/software/page/traditional-computer "Traditional Computer") plugged into the USB port, Debian may default to installing software from this local repository.A "[repository](https://en.m.wikipedia.org/wiki/Software_repository)" is the location that your software manager searches for available software.
Using the repository on your USB flash drive as the default may cause errors when trying to install software that is not locally available. In order to disable it, we need to open the [Synaptic Package Manager](https://en.m.wikipedia.org/wiki/Synaptic_(software)). This program is a visual interface for installing software and managing repositories that is available by default on Debian. When we open it from the Start Menu in the bottom right and navigate to "Administration", and then the program "Synaptic Package Manager". [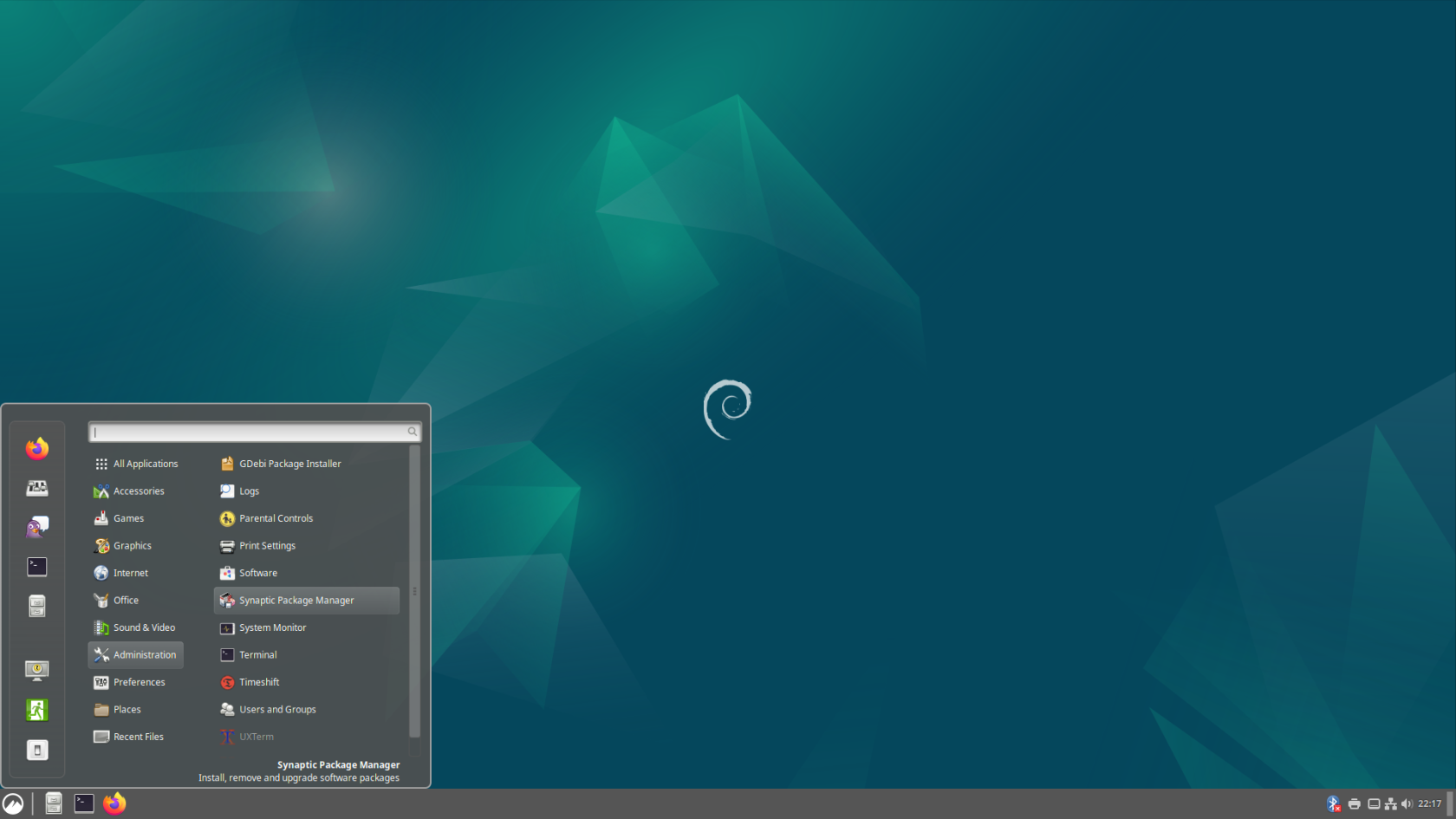](https://hub.subspace.services/uploads/images/gallery/2025-04/screenshot-from-2025-04-14-22-17-39.png)You will need to enter your account password.
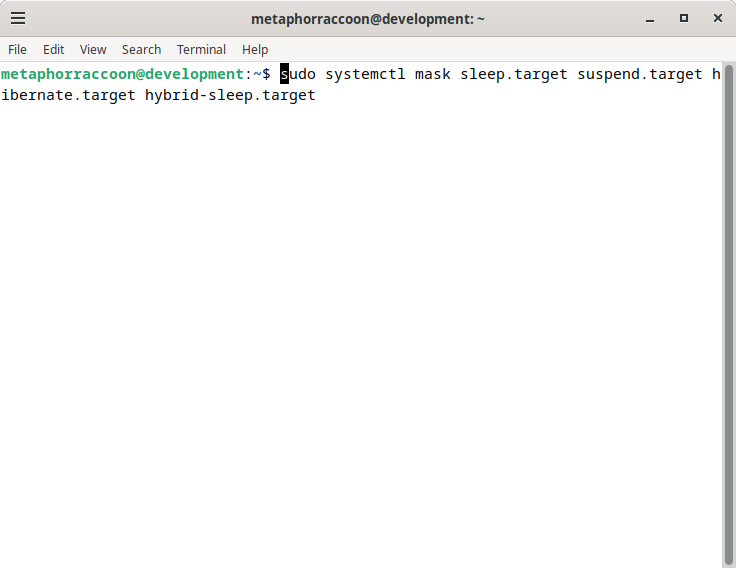
Opening this program will ask us to end the password for the root user account that we created during the [Debian installation process](https://hub.subspace.services/books/software/chapter/installing-an-operating-system "Installing an Operating System"). [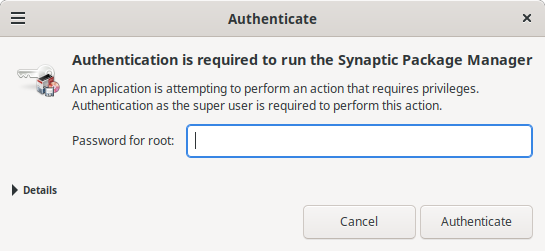](https://hub.subspace.services/uploads/images/gallery/2025-04/aXKimage.png) After we enter the password and open the program, we will be prompted with a help prompt that we can close. Now, we are presented the Synaptic Package Manager that is used to install software. [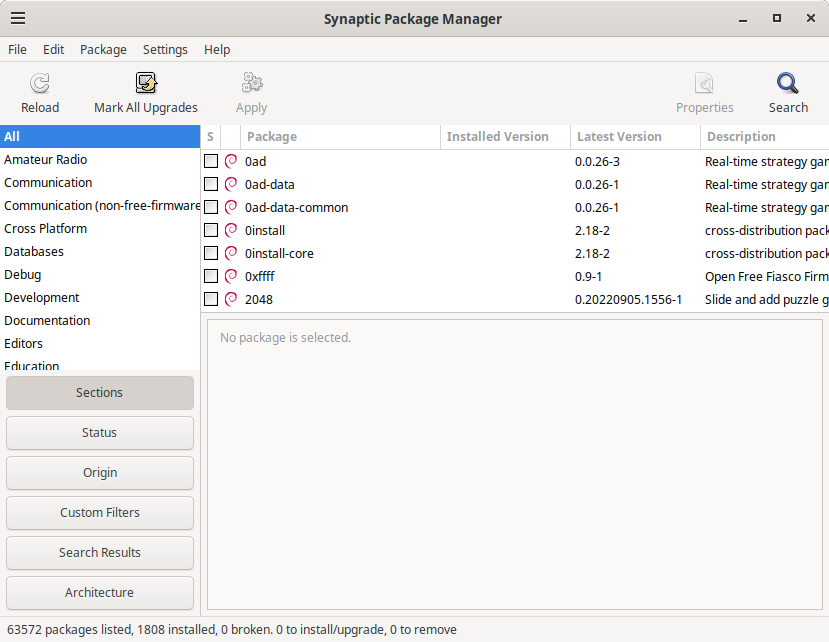](https://hub.subspace.services/uploads/images/gallery/2025-04/YeEimage.png) We are using Synaptic to change the Repositories used by this computer. Under the "Settings" menu, select "Repositories". This will open the "Software & Updates" window. We need to go to the "Other Software" tab and deselect the "**cdrom:**" entry. [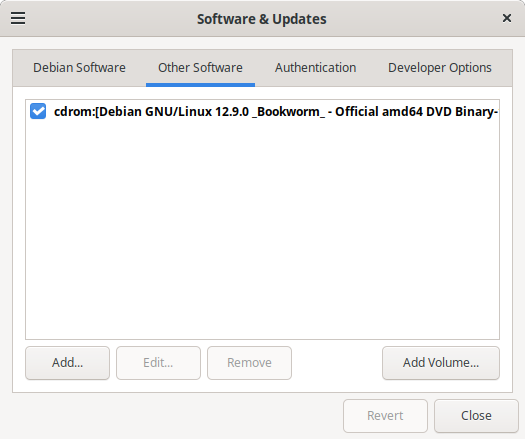](https://hub.subspace.services/uploads/images/gallery/2025-04/4Msimage.png) Once the option is deselected, it will prompt you to reload repository information so it knows what programs are available for download. [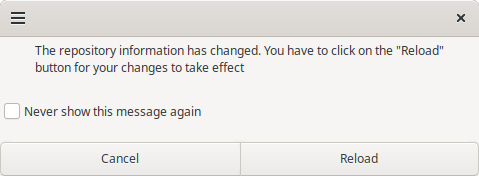](https://hub.subspace.services/uploads/images/gallery/2025-04/9NKimage.png) Once you do that, the system may request to update your repository because it is out of date. This will ensure that you are installing the most up-to-date software. # Administrator Permissions On Debian, our user account cannot run commands as Root through the terminal. We will be changing this for simplicity sake, allowing us to prefix commands with 'sudo' to run them as if they were run by root.Skip this step when using a Raspberry Pi.
We need to open the Terminal application from the side bar of the start menu. [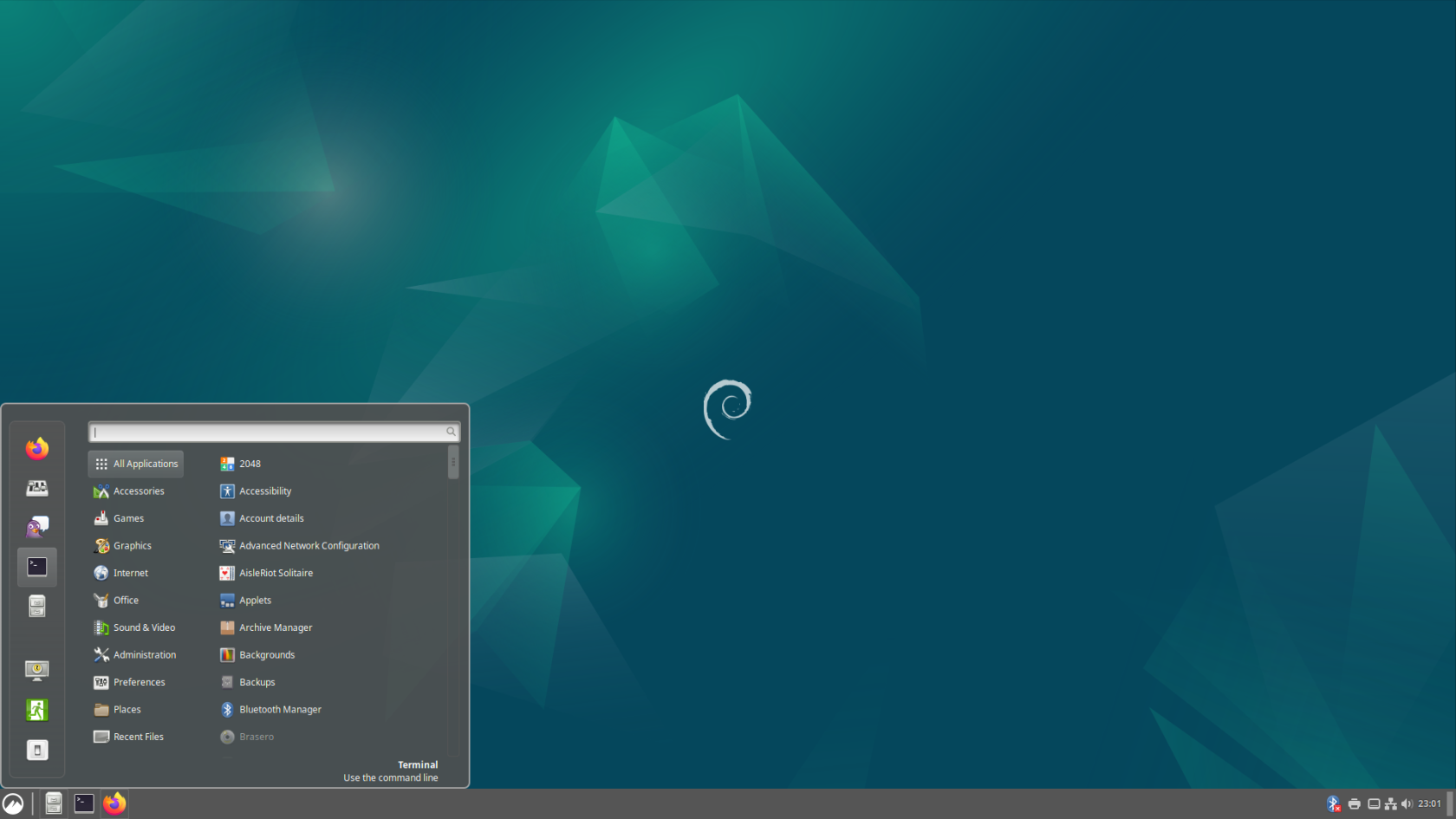](https://hub.subspace.services/uploads/images/gallery/2025-04/screenshot-from-2025-04-14-23-01-20.png) By default, we need temporarily "[substitute users](https://en.m.wikipedia.org/wiki/Su_(Unix))" to perform commands as root. Enter the command: ```bash su root ```| [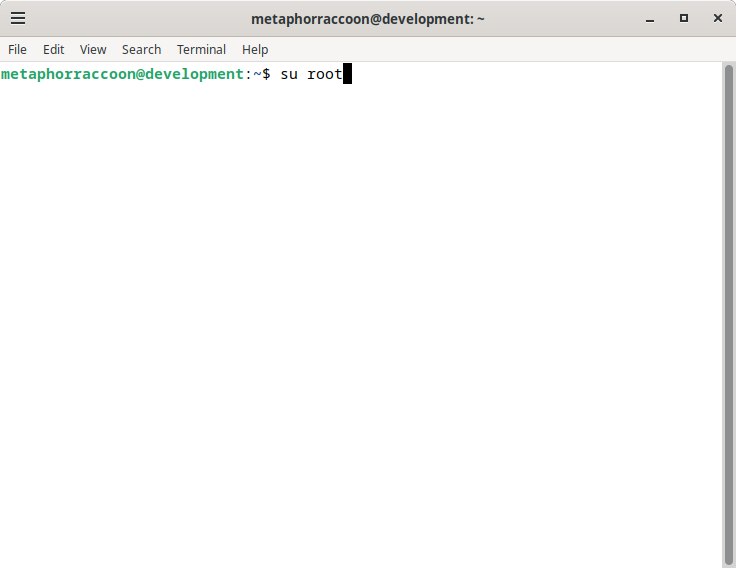](https://hub.subspace.services/uploads/images/gallery/2025-04/MEGimage.png) | [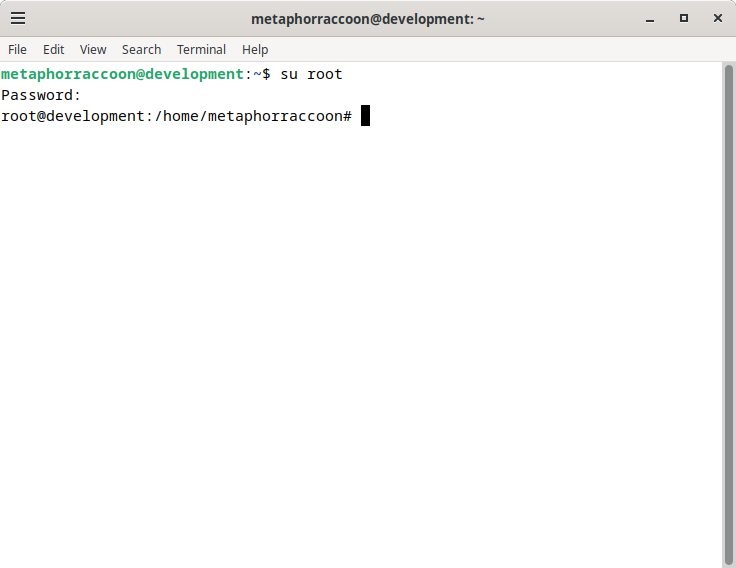](https://hub.subspace.services/uploads/images/gallery/2025-04/Ihpimage.png) |
When you are typing a password through the terminal, it will not display that you have typed any characters.
Now that we are acting as the root account, we can configure our user account to have the permissions to run all these same commands. We will be using an application called "visudo" This command ensures we cannot break permissions on our computer.Learn more about [visudo and the sudoers file](https://www.digitalocean.com/community/tutorials/how-to-edit-the-sudoers-file).
Enter the command: ```bash sudo visudo ```| [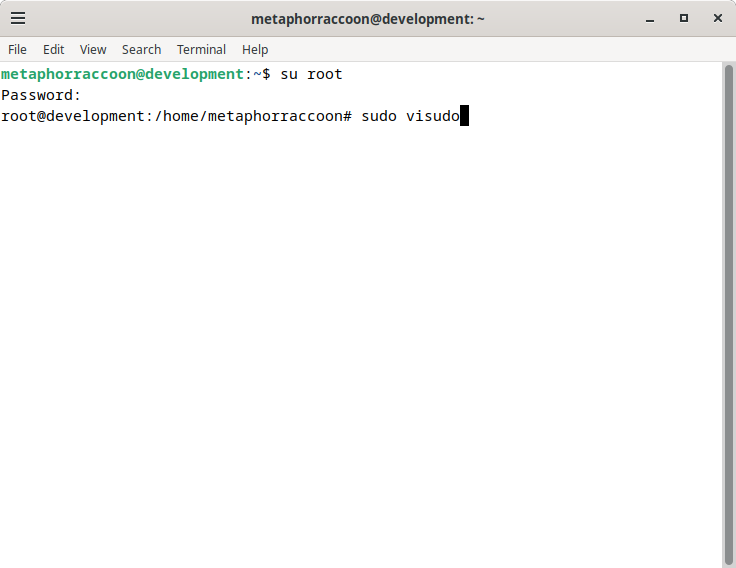](https://hub.subspace.services/uploads/images/gallery/2025-04/CA2image.png) | [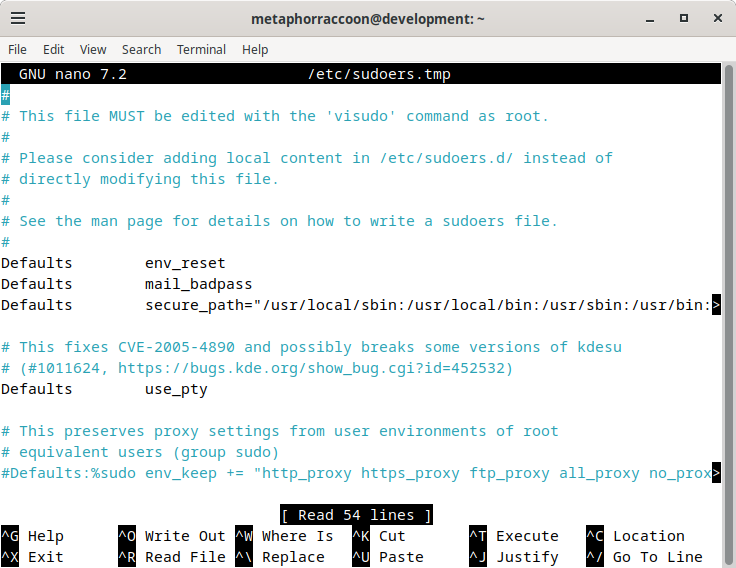](https://hub.subspace.services/uploads/images/gallery/2025-04/Nsoimage.png) |
| [](https://hub.subspace.services/uploads/images/gallery/2025-04/0Ttimage.png) | [](https://hub.subspace.services/uploads/images/gallery/2025-04/R43image.png) |
**Re-install all disk drives.** Make sure to shut down your computer and re-connect any disk drives that were unplugged during the Debian installation.
While Debian can support writing to NTFS disks using the [ntfs-3g](https://www.tuxera.com/company/open-source/) software, it can [decrease overall performance and access speeds](https://en.wikipedia.org/wiki/NTFS-3G). FAT and ExFAT file systems have native support within Debian, but are not an ideal server file system [due to technical limitations](https://support-in.wd.com/app/answers/detailweb/a_id/51807/~/pros-and-cons-of-file-systems-used-with-memory-cards%2C-usb-flash%2C-internal-and). If possible, important data should be copied to an alternate disk so that it can be reformatted as ext4.**Reformatting will erase the disk drive.** You will irrecoverably lose data stored on this drive.
[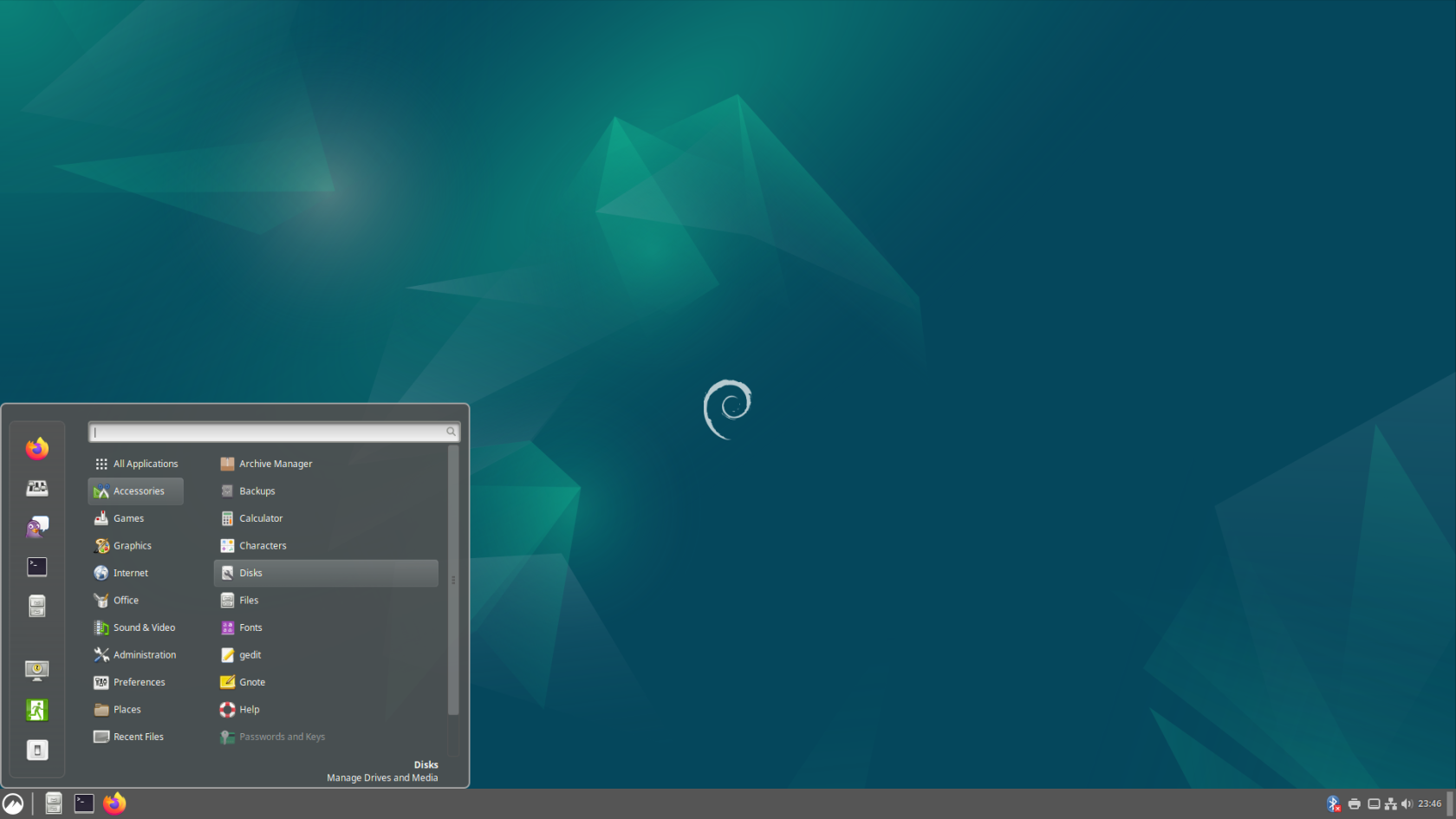](https://hub.subspace.services/uploads/images/gallery/2025-04/screenshot-from-2025-04-14-23-46-56.png) We will be opening the "Disks" application from the Start Menu, under the "Accessories" category. [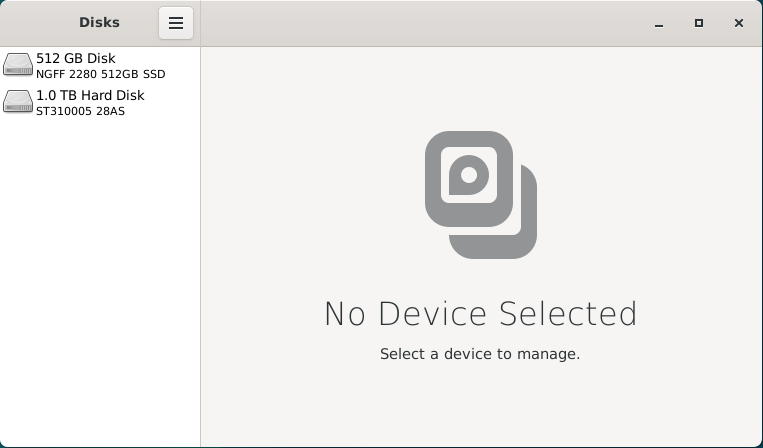](https://hub.subspace.services/uploads/images/gallery/2025-02/invimage.png) This application can be used to verify that the disk is formatted using the FAT, ExFAT or NTFS file system. Once we've done that, we can format the disk drive using the Linux ext4 file system for improved performance and reliability. When we select on the 1.0TB hard drive listed, we will see an overview of the partitions on this disk. There is a small 210MB EFI partition used for system files and a 1000GB partition that takes up the rest of the space. We can also see that the "Storage" partition is formatted using the NTFS file system. [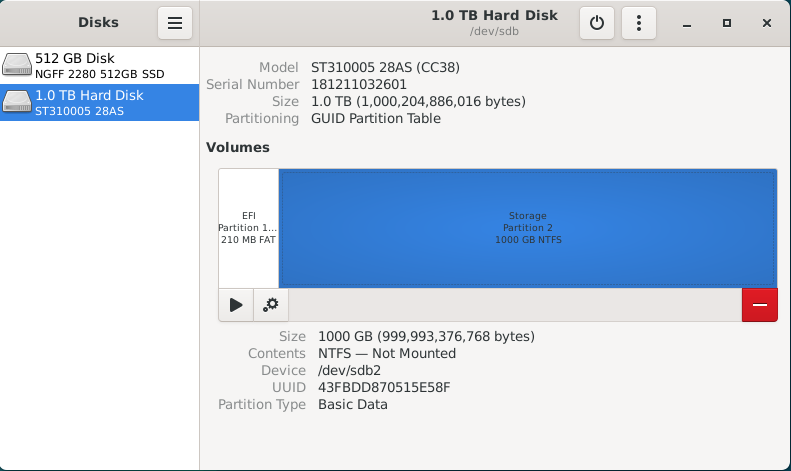](https://hub.subspace.services/uploads/images/gallery/2025-02/JqKimage.png) With the Storage partition selected, we select the red 'minus' icon to 'Delete selected partition'. We will receive a warning that all data on the partition will be erased. Once you are certain there is no important data on that partition, you can hit 'Delete'. [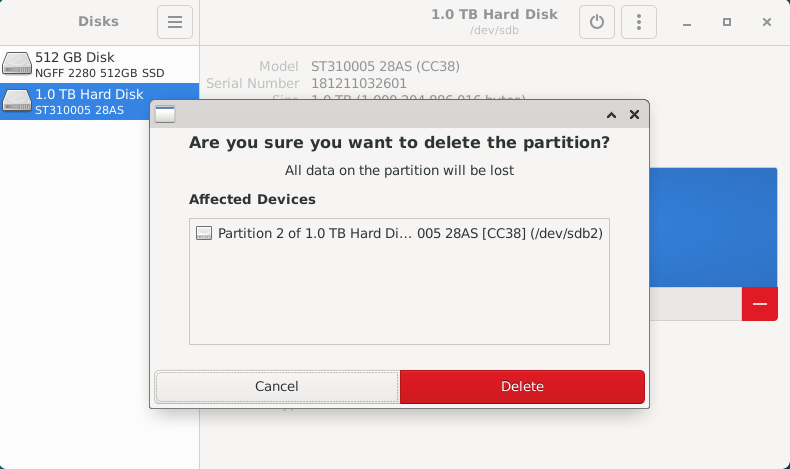](https://hub.subspace.services/uploads/images/gallery/2025-02/Iuzimage.png) If there are other data partitions, aside from the EFI partition, we will need to follow this process to remove them. After all the partitions have been removed from the disk, you will be presented with 1000GB of "Free Space" for us to create a new partition. [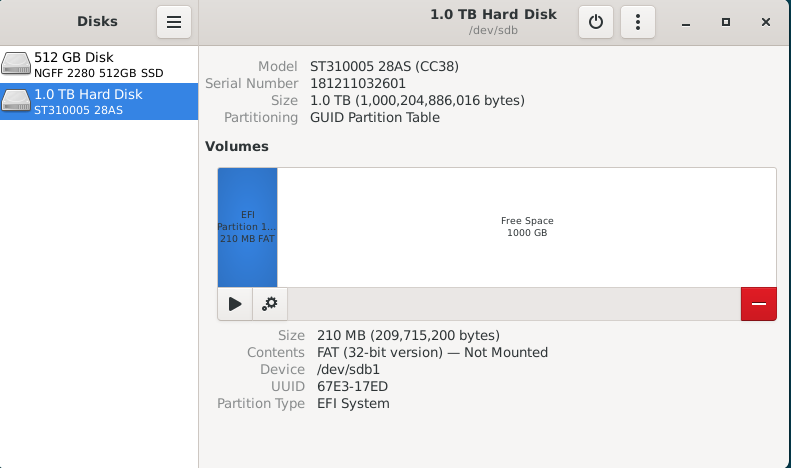](https://hub.subspace.services/uploads/images/gallery/2025-02/iJ9image.png) By selecting "Free Space", we are presented with a 'plus' icon that allows us to "Create partition in unallocated space". [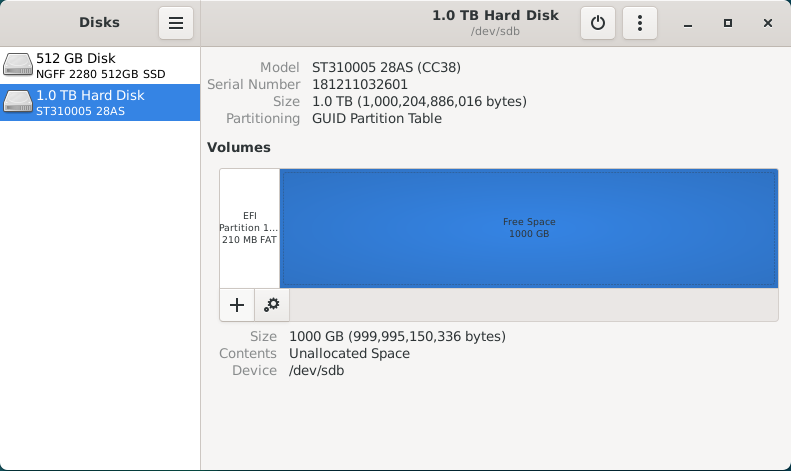](https://hub.subspace.services/uploads/images/gallery/2025-02/lBDimage.png) Clicking this button will open a partition creation wizard. First, we need to select how much space the partition will occupy. For this disk, we want the partition to fill the entire space so we will leave it at the default setting. Hit 'Next'. [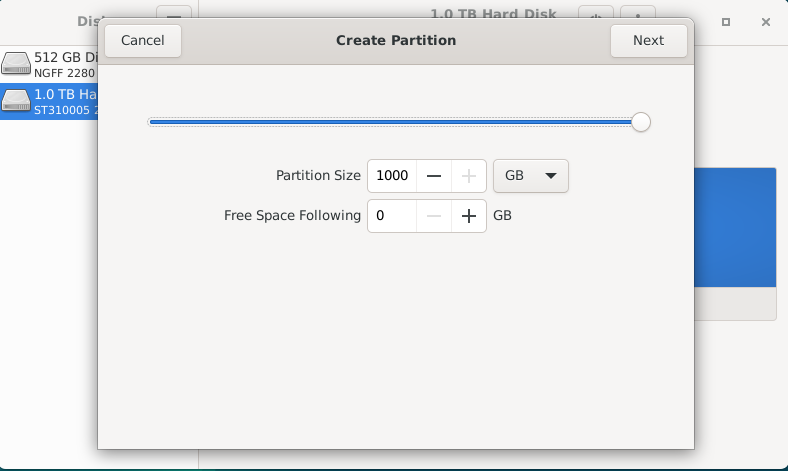](https://hub.subspace.services/uploads/images/gallery/2025-02/MV5image.png) Now, we will need to give a name to the partition and choose the file system type. This name can be anything you want, but simple descriptive language is usually best. We will name the partition "Storage" and choose the Type "Internal disk for use with Linux systems only (Ext4)". Optionally, you can choose to securely write over all the data that was stored on the drive. We do not want to encrypt our volume with LUKS. [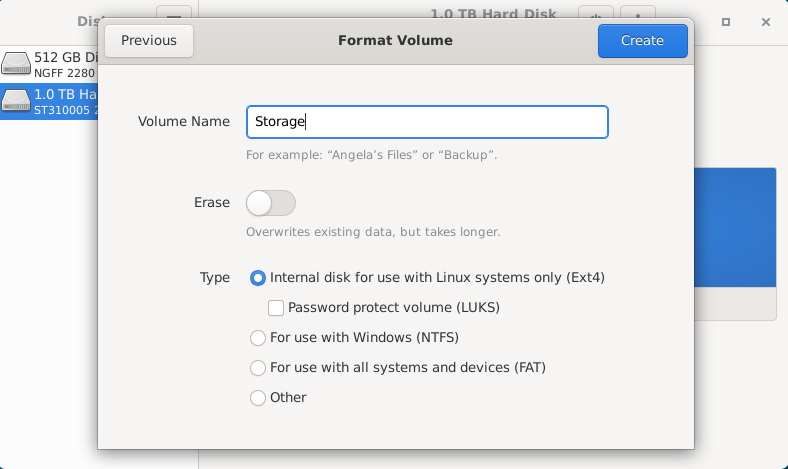](https://hub.subspace.services/uploads/images/gallery/2025-02/zfFimage.png) Once we hit 'Create', it will begin to format the disk with the new partition. [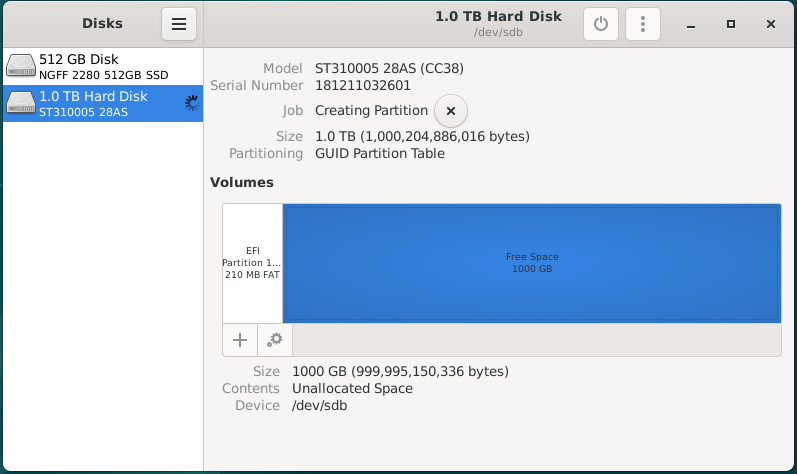](https://hub.subspace.services/uploads/images/gallery/2025-02/K6Pimage.png) Once it's completed the format process, you will have a new 'Storage' partition using the Ext4 file system. [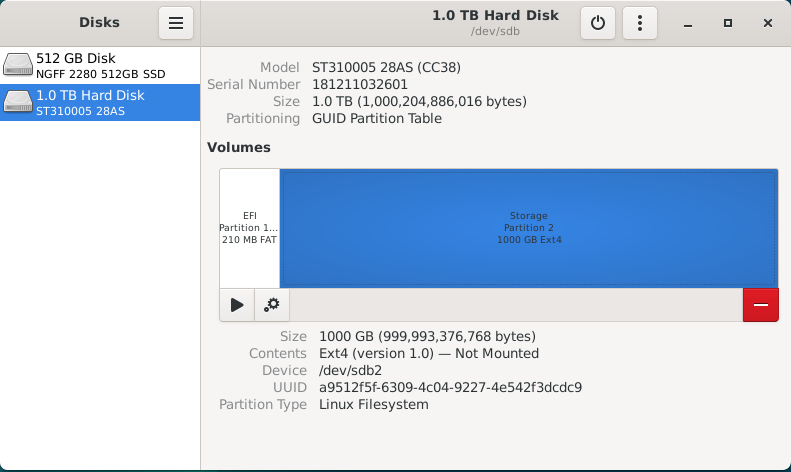](https://hub.subspace.services/uploads/images/gallery/2025-02/ns4image.png) Now, we can move on to mounting these storage disks at a permanent and centralized location. ## Mounting Drives While running a personal cloud or media server, you may need additional hard drives to store movies, television or documents. Whether you are using a USB hard drive or installed a new NVME SSD, they will need a fixed location for accessing their files. By default, internal drives are mounted within the /mnt folder while external hard drives are mounted inside a user folder within /mnt. We need to explicitly mount these disks so that they don't change unexpectedly between system reboots. For simplicity, we want to ensure all of our storage disks is permanently mounted within the /mnt folder. [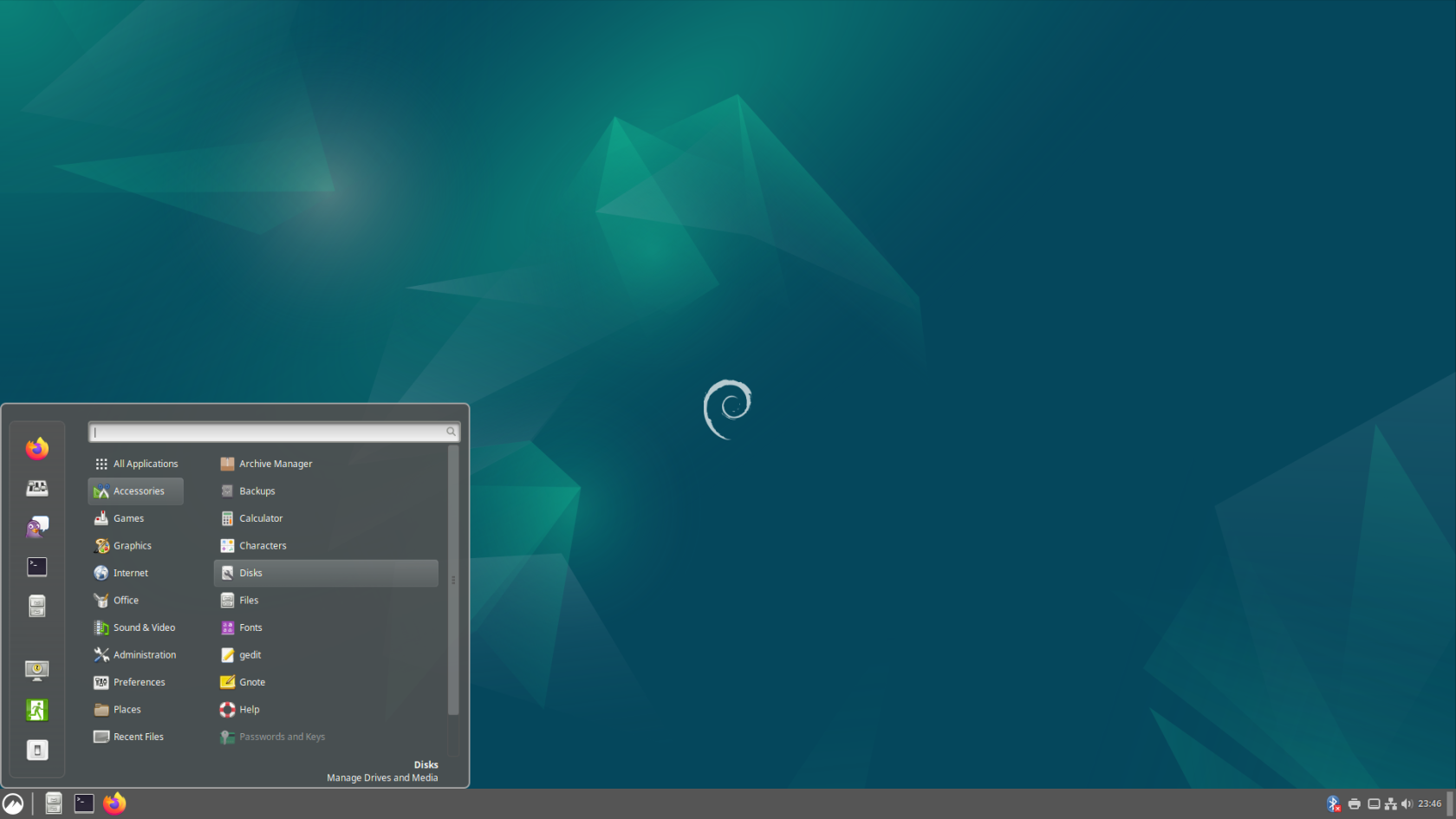](https://hub.subspace.services/uploads/images/gallery/2025-04/screenshot-from-2025-04-14-23-46-56.png) We will be opening the "Disks" application from the Start Menu, under the "Accessories" category. [](https://hub.subspace.services/uploads/images/gallery/2025-02/invimage.png) This application can be used to configure the file path used to mount the hard drive, as well as ensure that it will automatically be mounted each time the computer is started.This application is being run as Root and has the potential to break your Debian install if you aren't careful.
There are currently two disk drives installed into this computer; an SSD for the operating system, as well as an external hard drive for media storage. For this example, we will be changing the mount location for an external USB hard drive to the /mnt folder. We can select the drive from the sidebar and we will be able to inspect all of the partitions on this drive. [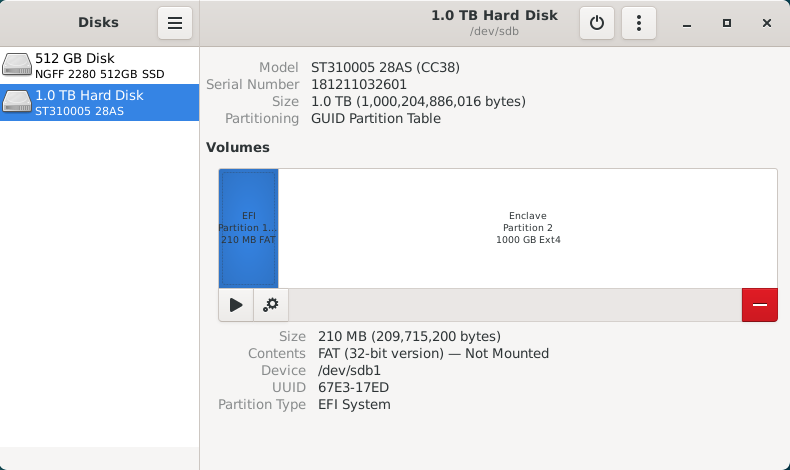](https://hub.subspace.services/uploads/images/gallery/2025-02/EYmimage.png) This drive has a small 210MB EFI partition, which stores system information, as well as a primary 1000GB data partition named "Enclave". We will ignore the EFI partition because it should not be mounted. For continuity, we will be mounting the Enclave partition at "/mnt/enclave". First, we need to select the Enclave partition, then click the gear icon to bring up the "Additional partition options" menu. [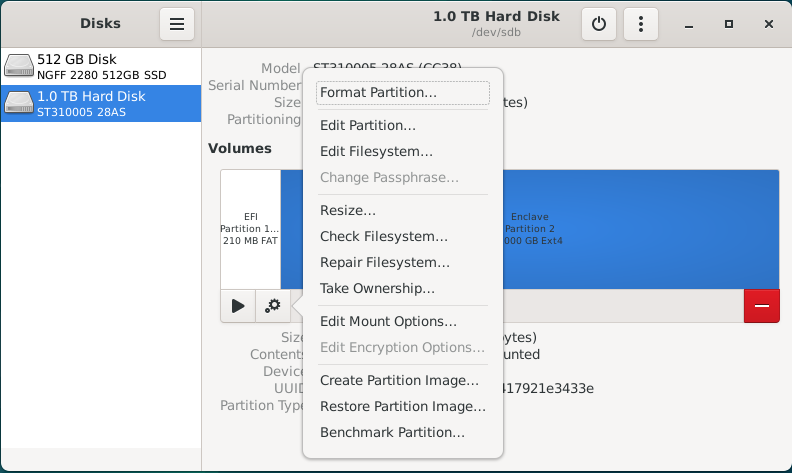](https://hub.subspace.services/uploads/images/gallery/2025-02/VIrimage.png) Once this menu is open, select "Edit Mount Options..." to bring up a screen that will let us configure how the operating system will handle mounting this disk drive. As you can see, the operating system has opted to use the "User Session Defaults" which will mount the USB hard drive within /mnt using a name based on the hard drives model number. [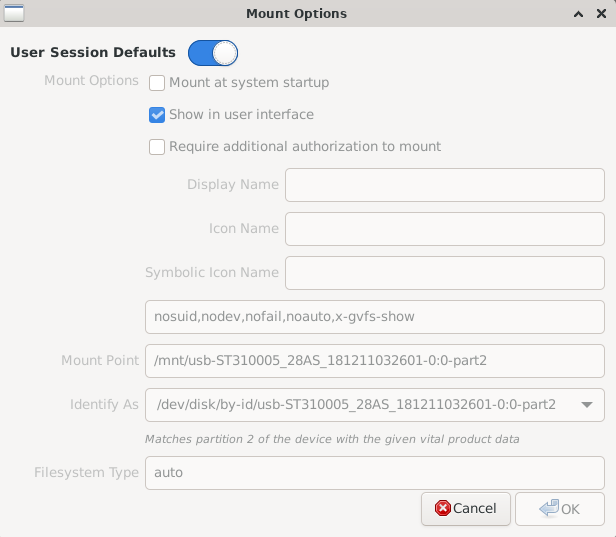](https://hub.subspace.services/uploads/images/gallery/2025-02/3RHimage.png) Deselect the "User Session Defaults" option and you will be able to change these settings. We want to ensure that the "Mount at system startup" and "Show in user interface" option are selected. Next, we will be changing the Mount Point to '/mnt/enclave'. Finally, we will be changing "Identify As" to the option that begins with "/dev/disk/by-uuid/\*". Each hard drive has a [Universally Unique Identifier](https://en.wikipedia.org/wiki/Universally_unique_identifier) that does not change and will ensure that the correct drive is always mounted at the correct location. [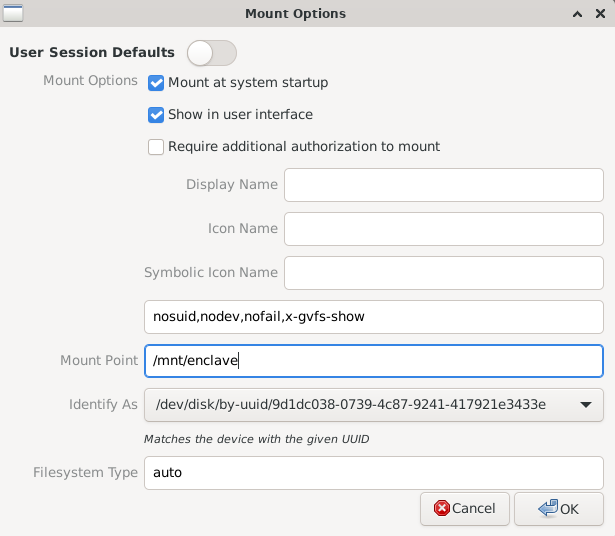](https://hub.subspace.services/uploads/images/gallery/2025-02/8Nximage.png) Once we hit OK, the software will commit these changes to the /etc/fstab – or [File Systems Table](https://en.wikipedia.org/wiki/Fstab) – file. This is a core operating system file that handles the mounting of both local and network drives during the boot process. As we can see, the hard drive we've just finished configuring hasn't been mounted for use yet. [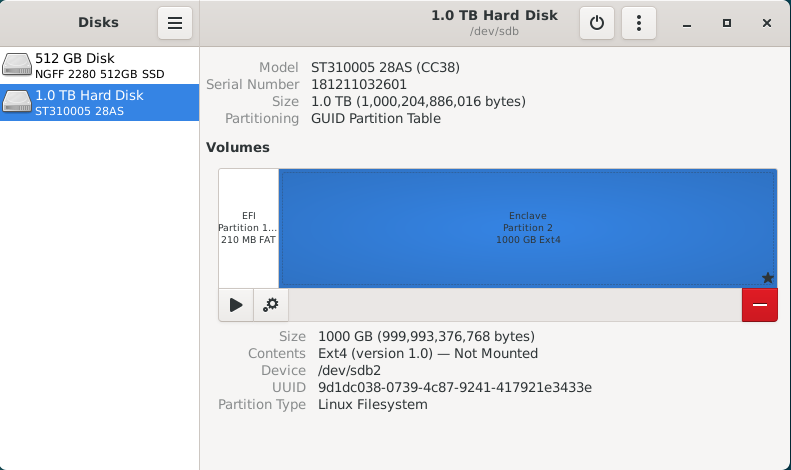](https://hub.subspace.services/uploads/images/gallery/2025-02/1P3image.png) Now we need to hit the "Play" icon labeled as "Mount selected partition" to make it available for use. This will mount the hard drive on your desktop, within the file browser, and the configured "/mnt/enclave" path. [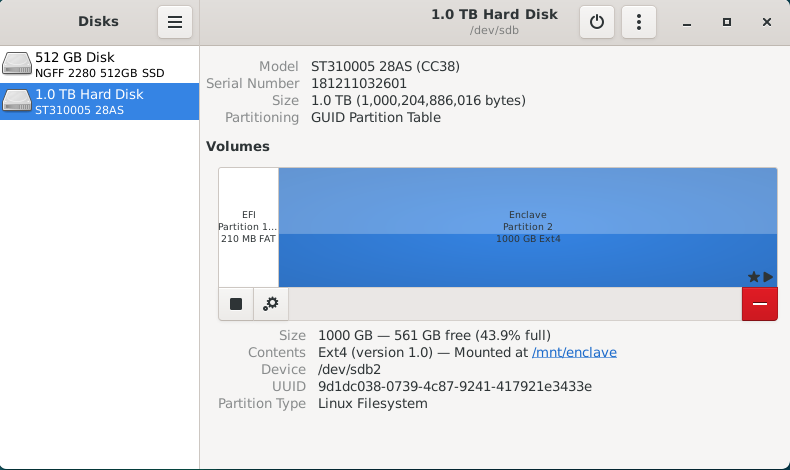](https://hub.subspace.services/uploads/images/gallery/2025-02/L0Timage.png) Next, we can close the Disk Manager. This should bring our terminal window back up. We can run the following command to ensure the data stored on it is accessible to everyone on the local computer: ```bash sudo chmod -R 777 /mnt/enclave ``` You can now navigate to "/mnt/enclave" in the file manager to verify that the directory is accessible. You may want to attempt creating a new folder through the File menu or by right-clicking on the empty space and selecting "New folder". [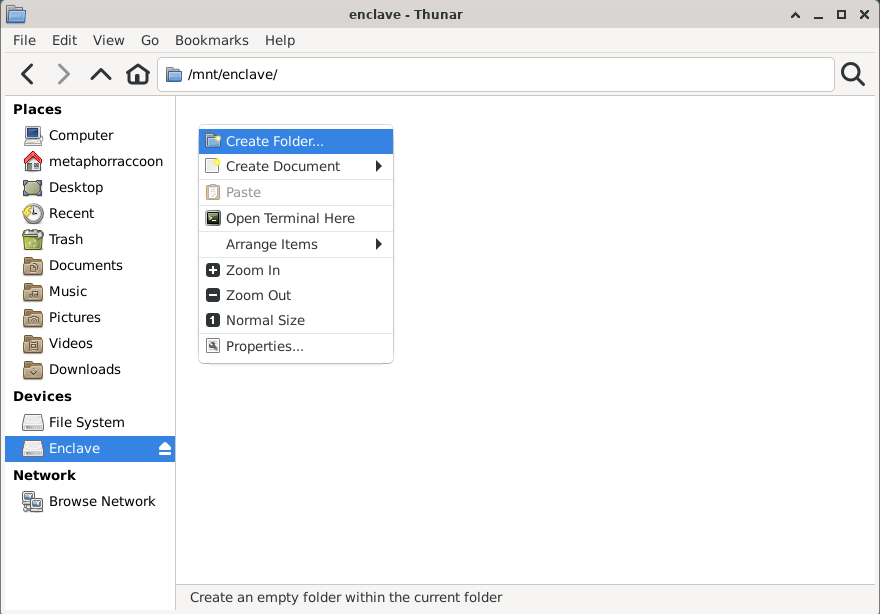](https://hub.subspace.services/uploads/images/gallery/2025-02/ZP1image.png) If you are able to create a new folder, then your new hard drive is setup and ready for use. You can now delete this folder. [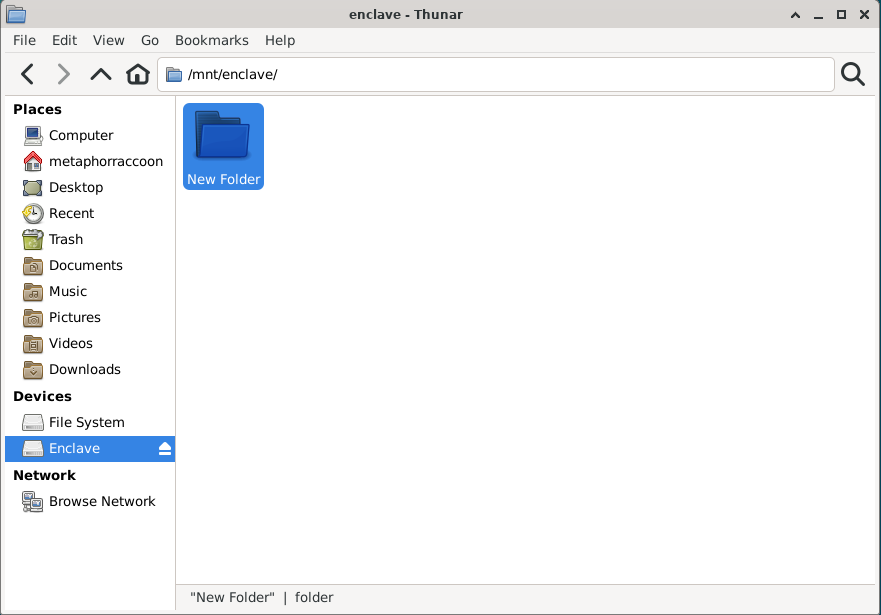](https://hub.subspace.services/uploads/images/gallery/2025-02/03yimage.png) # Graphics Card The Debian operating system comes with innate support for many AMD, Nvidia and Intel graphics hardware. Depending on the manufacturer, the open-source driver's hardware integration and functionality can be limited until proprietary drivers are installed.Skip this step when using a Raspberry Pi.
## AMD/ATI [](https://hub.subspace.services/uploads/images/gallery/2025-02/1000006175.jpg) Modern AMD graphics (2015 or later) are fully supported and run stable out-of-the-box using the [open-source AMDGPU software maintained by Debian](https://wiki.debian.org/AtiHowTo). AMD provide their own proprietary drivers, but they can [cause system instability](https://wiki.debian.org/GraphicsCard) and should be avoided. ## Intel [](https://hub.subspace.services/uploads/images/gallery/2025-02/1000006177.jpg) Integrated graphics, like those found in Intel processors since 1999, are fully supported and run stable out-of-the-box using [X.org's Intel Graphics Driver](https://www.x.org/wiki/IntelGraphicsDriver/). While [older models require a different driver](https://wiki.debian.org/GraphicsCard#Intel), they are still fully supported. ## Nvidia [](https://hub.subspace.services/uploads/images/gallery/2025-02/1000006178.jpg)Nvidia graphic drivers are partly closed-source and privately owned by Nvidia.
Debian can support basic features with most Nvidia graphics card using the open-source [Nouveau Driver](https://nouveau.freedesktop.org/) maintained by freedesktop. This driver has limitations though and may not perform optimally under some conditions. Media applications like [Plex](https://hub.subspace.services/books/media-servers/chapter/plex "Plex") or [Jellyfin](https://hub.subspace.services/books/media-servers/chapter/jellyfin "Jellyfin") require the proprietary Nvidia drivers to be installed on your system. They are also required for [connecting your graphics card to the Docker engine](https://hub.subspace.services/books/software/page/graphic-card-integration "Graphic Card Integration") for use by services. Before you can install the proprietary Nvidia drivers, you need to ensure which graphics card you have and [which driver versions are supported](https://us.download.nvidia.com/XFree86/Linux-x86_64/535.183.01/README/supportedchips.html) for your card. Newer cards work with the unified driver, while legacy cards are supported through specific driver release versions. This can be a finicky process. Debian [provides instructions ](https://wiki.debian.org/NvidiaGraphicsDrivers#Debian_12_.22Bookworm.22)for how to install the Nvidia graphics card drivers. Alternatively, you can use the [nvidia-detect script](https://wiki.debian.org/NvidiaGraphicsDrivers#nvidia-detect) to identify and install the correct drivers. # Networking We need to set a static IP for our server so that we can always access it from the same address.Your server should be plugged in directly to the router with a Cat6 Ethernet cable.
Before we do this, we should verify our current internet connection settings and write down some important details for later. We need to know the computer's current local network IP address and the address for our internet gateway. ## Collecting Information First, we need to install a utility that can quickly output this information for us: ```bash sudo apt install -y net-tools ``` ### Default Network Device Once this completes, we will need to run a command to find out what our default network device is: ```bash ip -o route show | grep default | perl -nle 'if ( /dev\s+(\S+)/ ) {print $1}' ``` This will return the device name about our default network interface which should be our wired connection.You may want a piece of paper to write down notes.
[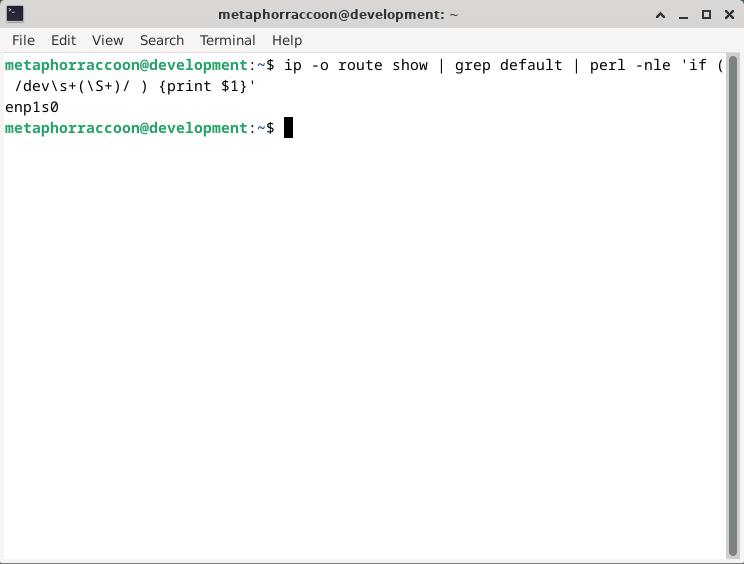](https://hub.subspace.services/uploads/images/gallery/2025-02/CmOimage.png) This shows that our default network interface is named **enp1s0**. Write this down for later.| **Network Device** | enp1s0 |
| **Network Device** | enp1s0 |
| **Gateway** | 192.168.68.1 |
| **Network Device** | enp1s0 |
| **Gateway** | 192.168.68.1 |
| **IP Address** | 192.168.68.100 |
| **Netmask** | 255.255.252.0 |
| **Network Device** | enp1s0 |
| **Gateway** | 192.168.68.1 |
| **IP Address** | 192.168.68.100 |
| **Netmask** | 255.255.252.0 |
| **DNS servers** | 1.1.1.1, 1.0.0.1 |
Reboot the computer to ensure everything is working as intended.
### Verify Connection After restarting your computer, open up the terminal. We will now run two commands to ensure the internet is working and we have the correct local IP address. ```bash ping -c 5 1.1.1.1 ``` This will ensure that our computer has access to the Cloudflare DNS server. We will consider the test has passed if the command reports '0% packet loss'. [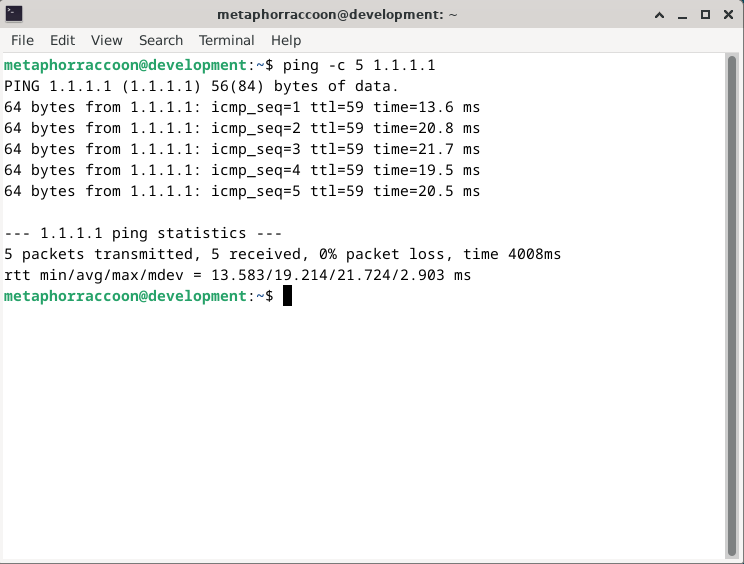](https://hub.subspace.services/uploads/images/gallery/2025-02/XdRimage.png) We can now run one final command to verify our computer is using the static IP address we configured: ```bash ip -o route show | grep default ``` This will show an overview our default internet connection and we can see that it is now labeled as a 'static' connection. [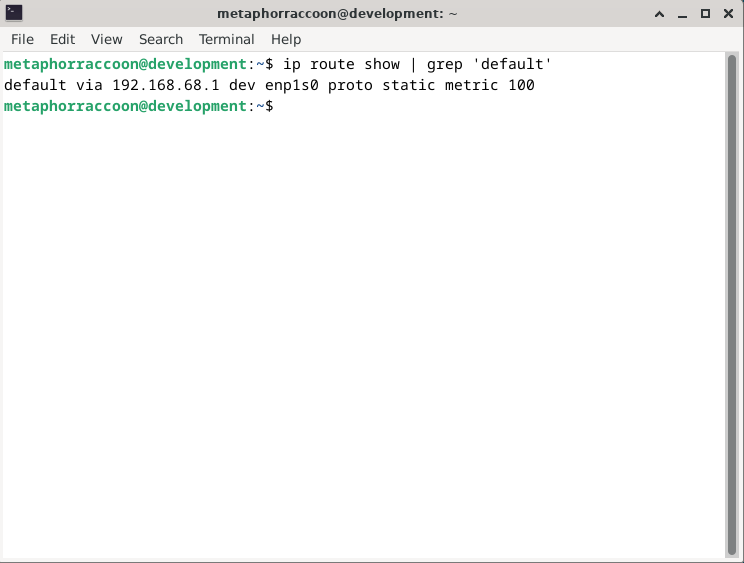](https://hub.subspace.services/uploads/images/gallery/2025-02/rzDimage.png) You now have a computer with a static IP address that will always stay the same. # Building Community The [free and open software community](https://en.m.wikipedia.org/wiki/Free_and_open-source_software) is the culmination of the [free software movement](https://en.m.wikipedia.org/wiki/Free_software_movement), the [open source movement](https://en.m.wikipedia.org/wiki/Open-source_software_movement) and numerous other independent developers who support software freedom. The GNU and Linux projects are the most extensive examples of free and open-source collaboration.| [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000463.png) | [](https://hub.subspace.services/uploads/images/gallery/2025-05/1000000350.png) |
| [](https://hub.subspace.services/uploads/images/gallery/2025-06/1000000614.png) |
| Church | **The Cathedral**
These open-source projects release their source code once it has been finalized, but it is not available to the general public while in active development. This restricts who has the privilege to make changes to the underlying source code to an exclusive group.
The GNU project often uses this philosophy. |
| Storefront | **The Bazaar**
These open-source projects make their source code completely available on the Internet throughout the entire development process. Everyone has access to the source code, but making modifications to it requires oversight by the project.
The Linux kernel uses this philosophy. |
| [](https://hub.subspace.services/uploads/images/gallery/2025-06/1000000624.png) | [](https://hub.subspace.services/uploads/images/gallery/2025-06/1000000623.png) |
| Domino\_mask | **Anonymous** Unless a software project has been intentionally marked as private, the source code is freely available for download by anyone who accesses the repository even if they haven't logged in. |
| person | **User** This is any person who has an account on the platform with a verified email. Each project can configure how unaffiliated users are allowed to interact with the source code. Open-source software debelopers often value diverse perspectives from every day users and explicitly request feedback. |
| deployed\_code\_account | **Collaborator** This is any person that a software project has explicitly chosen to give affiliation status. This can offer fine tuned control to specific developers and provide blanket access to all collaborators. In the case of a private project, this can be used to offer exclusive access to source code. |
| Person\_edit | **Contributor** Once a verified user has submitted a change and it's accepted, they are considered a contributor within that project. Before proposing changes, each user must follow the rules and integrate themselves into the community. These contributions are not limited to source code, but also include stewardship responsibilities – such as bug reports, feature requests and documentation writing. |
| how\_to\_reg | **Trusted Member** This role can vary widely between projects and is often defined more by their responsibilities than their privileges. While an average contributor can suggest changes, these project members are often the ones in charge of actuating them. These tasks often have a greater degree of risk involved and require earning the respect of the community. |
| engineering | **Maintainer** This entity has the significant responsibility of overseeing the project and it's community. While there can only be one primary maintainer, this can represent a collective or organization. They perform technical tasks as well as maintain the project's direction. |
| call\_split | [**Branch**](https://en.m.wikipedia.org/wiki/Branching_(revision_control)) This is an isolated copy of the source code that makes it easier for developers to collaborate on changes without risking damage to the trunk. These help to keep track of what was changed, by who, and for what reason. These exist within a project to facilitate collaboration and coordinate development. |
| call\_merge | [**Merge**](https://en.m.wikipedia.org/wiki/Merge_(revision_control)) Once changes within a branch are finalized and tested to ensure stability, then can be merged back into the main trunk. This allows all software development loose ends to be addressed before creating a final release of the software trunk. |
| Flowchart | [**Fork**](https://en.m.wikipedia.org/wiki/Fork_(software_development)) This is a completely new repository – under new ownership – that is a complete replica of another existing repository. This can happen for a variety of reasons ranging from personal modifications to differing decisions among the development team. Repository forks allow anyone to modify software to their needs and propose changes back to a project they are not a developer on. |
| Commit | [**Commit**](https://en.m.wikipedia.org/wiki/Commit_(version_control)) This is a formal change to source code files on your local repository that are given a unique identification number and maintain a narrative about its history. This builds a foundation of accountability by tracking who made what changes to files when. Traditionally, these contain a message from the developer about their changes and the reasoning behind it. |
| cloud\_upload | [**Push**](https://en.wikipedia.org/wiki/Version_control#Pull,_push) Once you have finalized your commit, the changes can be pushed [upstream](https://en.m.wikipedia.org/wiki/Upstream_(software_development)) to the central repository so they can be accessed by everyone. |
| Cloud\_download | [**Pull**](https://en.wikipedia.org/wiki/Version_control#Pull,_push) When first acquiring the source files from a project's repository, Git on your computer will *pull* the code from the repository. This allows you to modify the files and compile the program yourself from scratch. As a part of the project, you can often commit and push the files directly back to the repository. When you are not affiliated with the project, you can create your own fork and communicate with the parent project about your proposed changes. From there, they can perform a *pull request* to merge the new code created in your personal fork. |
| Support | **User Documentation** While intended for a general audience, this resource can explore the software from multiple distinct perspectives – such as users, systems administrator and support staff. This describes the features of a program and explores how users can fully leverage them. Consider it the contract detailing what the software does. Documentation can fulfill using guides, tutorials, troubleshooting and frequently asked questions. While they are not inherently designed in a specific way, the overall goal to create a resource that is intuitive and accessible – clearing more confusion than it creates. Most incorporate an index for exploring defined concepts or sections. |
| Engineering | **Technical Documentation** Intended primarily for developers, this resource helps to grasp how the programs works internally. This covers the logic behind algorithms, explains how to leverage their API, and details emergent software systems that power the program. Technical documentation may be available on its own wiki or integrated directly into the source code. |
| Volunteer\_activism | **Contribution Guidelines** Open-source software projects often come with information about how you can help contribute to the project. This generally explores the process and guidelines for becoming a contributor, such as how to submit bug reports and feature requests as well as rules and etiquette for communication. |
| Diversity\_3 | **Community Involvement** Many volunteers are looking to give back to the community and find fulfillment through simply being involved with others. They may use the software everyday and want to support it. This can take many forms: participating in hackathons; undertaking code reviews; updating documentation; or simply sharing the word. |
| School | **Continuing Education** Some volunteers are seeking to learn a new skill or further develop one they already have. Established open-source projects often excel at onboarding new community members, providing valuable structure and mentorship. |
| Paid | **Paid Work** Not all people who [contribute to open-source projects are by necessity unpaid volunteers](https://opensourcesurvey.org/2017/). The largest contributions to projects like the Linux kernel are by paid employees working for the companies like IBM and Intel. Similarly, corporate Linux distributions like Red Hat provide paid hours to developing the Kernel for their own software. It is [not uncommon for contracted work](https://opensourcesurvey.org/2017/) to be incorporated into open source software. |
| Interests | **Side Projects** Some developers create their own software to solve a problem and end up sharing their solution freely, while others may seek fulfillment by creating something people like to use. Solving puzzles with a community or fixing an irritating bug can scratch an itch. At the end of the day, it's about personal enrichment. |
| Cognition | **Personal Motivations** Developers may be motivated by personal reasons stemming from emotional, political, social, interpersonal, economic or professional reasons. Contributing to open-source projects can fulfill political agendas, [build up a developer's portfolio](https://www.wired.com/2017/06/diversity-open-source-even-worse-tech-overall/), or create a reputation within the community. |
| Diversity\_2 | **Gender** Even though [programming was originally a femininized profession](https://ieeexplore.ieee.org/document/9354402), there is a critical disparity when it comes to their representation within [computing in general](https://en.m.wikipedia.org/wiki/Gender_disparity_in_computing). This has only grown worse within the free and open-source projects. While researchers and journalists have employed differing methods for understanding this problem, they all reflect the same problem. Within the field of computing, approximately [22% of engineers identify as women](https://www.bls.gov/cps/aa2017/cpsaat11.htm). [Women do not feel that they have equal opportunities](https://www.computer.org/csdl/magazine/co/2022/12/09963732/1Iz0RZM9Wbm) for entering the field. For open-source communities, this drops to estimates ranging from [1%](https://www.math.unipd.it/~bellio/FLOSS%20Final%20Report%20-%20Part%204%20-%20Survey%20of%20Developers.pdf) to [3%](https://www.bls.gov/cps/aa2017/cpsaat11.htm) when creating code. When [taking into account non-software contributions](https://link.springer.com/chapter/10.1007%2F978-3-319-39225-7_13), this may be [upwards of 10%](https://www.win.tue.nl/~aserebre/msr14gregorio.pdf). The [most recent 2021 report](https://www.linuxfoundation.org/wp-content/uploads/LFResearch_DEISurvey_Report_121321_6.pdf) by the Linux Foundation suggests this has risen to 14% – still an incredibly small portion. Despite the recent increase of women in open-source, [only 5% of projects have women](https://biancatrink.github.io/files/papers/TOSEM2021.pdf) as core developers. This is compared to [over 30% of managers in computing](https://www.bls.gov/cps/cpsaat11.htm) being women. When code is [pulled](https://hub.subspace.services/books/software/page/building-community "Building Community") from an external developer's project, [less than 5% of those developers](https://biancatrink.github.io/files/papers/TOSEM2021.pdf) are women. |
| Diversity\_2 | **Queer Identities** There is a diverse spectrum of identities that we embody as we express ourselves. The diversity disparity in computing extends to people who identify as [queer](https://www.ironhack.com/us/blog/lgbtq-representation-in-tech-challenges-and-opportunities) – or do not conform to societal expectations surrounding gender or sexuality. An [estimated 3% of the technology sector](https://www.womentech.net/blog/lgbtq-work-key-stats-and-insights) identify as queer within the tech sector, but this may not be a complete view. Identity can be personal and [nearly half of employees do not feel](https://www.deloitte.com/content/dam/assets-shared/docs/about/2023/deloitte-global-2023-lgbt-inclusion-at-work.pdf?dl=1) comfortable being out with their identities at work. Overall, [queer identities are underrepresented in technology](https://lesbianswhotech.org/about/). Within the [GitHub development community](https://opensourcesurvey.org/2017/), there is more historical data available about how people's identities intersect with their contributions. Here, queer people have begun to find representation with 1% each identifying as transgender or non-binary as well as 7% considering themselves as queer. The [most recent report](https://www.linuxfoundation.org/wp-content/uploads/LFResearch_DEISurvey_Report_121321_6.pdf) from the Linux Foundation suggests that this has been trending upwards. Through their survey, 74% of open-source contributors identify as heterosexual, 16% as queer and 10% choosing not to disclose. |
| Diversity\_2 | **Race and Ethnicity** Similar to computing, there is a dire lack of racial diversity in the open-source communities. Black and Latine people are [greatly underrepresented within software development](https://www.npr.org/sections/codeswitch/2013/12/05/248791579/why-isnt-open-source-a-gateway-for-coders-of-color). When it comes to management positions, the [majority are filled by White men](https://opensourcesurvey.org/2017/). There is surprisingly little hard data available to better understand diversity. [16% of developers identify as a ethnic or national minority](https://opensourcesurvey.org/2017/), compared to the [national total of 34%](https://www.bls.gov/cps/aa2017/cpsaat11.htm). Latine, Black and Indigenous developers [do not feel that they have equal opportunities to participate](https://www.linuxfoundation.org/wp-content/uploads/LFResearch_DEISurvey_Report_121321_6.pdf). |
| Diversity\_2 | **Age** Developers within technology – and open-source software – are predominantly young. Nearly half of professional developers are [between the ages of 25 — 34 years old](https://survey.stackoverflow.co/2023/#age). After the age of 40, [job hunting within the field can be daunting](https://opensource.com/life/16/3/can-we-talk-about-ageism). Within large tech companies, the [median age for workers](https://www.payscale.com/data-packages/top-tech-companies-compared/) is about 30 years old. When it comes to learning how to code, [young adults from 18 — 24 years old](https://survey.stackoverflow.co/2023/#age) make up nearly half of learners. |
| Diversity\_2 | **Disability** With the ability to work remotely on a software project, open-source software has [helped some people contribute more regularly](https://longmoreinstitute.sfsu.edu/archive/there%E2%80%99s-always-something-be-done-liz-henry-being-disabled-tech.html). Within open-source, [surveys show 17% of contributors](https://www.linuxfoundation.org/wp-content/uploads/LFResearch_DEISurvey_Report_121321_6.pdf) have a long-term physical, mental, intellectual, or sensory impairment. |
| Docs | **Document** When it comes to creating inclusive spaces, documentation is [one of the most important steps](https://opensourcesurvey.org/2017/) to help people feel included. When you have come to understand a software program, helping to [create concise documentation](https://insights.stackoverflow.com/survey/2019#:~:text=Over%2040%25%20of%20respondents%20have,and%20Kotlin%20have%20the%20fewest) can help to remove barriers to entry. - Can you help to [assess technical jargon](https://opensource.com/article/17/9/diversity-and-inclusion-innovation) that may feel exclusionary? - Can you help streamline complex descriptions and guides? - Can you translate the existing documentation into [another language](https://opensource.com/article/17/9/diversity-and-inclusion-innovation)? |
| Code | **Develop** If you are comfortable with project development, many open-source software will welcome input from the community. This can mean giving feedback and interacting with polls as well as contributing source code. If in doubt, many projects will detail their policies on their wiki or through their repository using a [contributing.md file](https://docs.github.com/en/communities/setting-up-your-project-for-healthy-contributions/setting-guidelines-for-repository-contributors). - Can you provide constructive feedback about what you do or don't like? - Can you offer any information about bugs you encounter in the software? - Can you communicate your ideas for how a new feature could elevate the software to the next level? - Can you suggest code to fix bugs, build new features or improve efficiency? - Can you mentor new talent and help guide them towards leadership? |
| Volunteer\_activism | **Advocate** By taking the time to learn about a situation, we can use our voice to try and impart change within the communities we want to see succeed. This can help to create environments where we all feel safe and equipped to collaborate. - Can you build pressure to create or enforce a clear code of conduct within this community project? - Can you suggest [project-wide strategies ](https://opensource.com/article/17/9/diversity-and-inclusion-innovation)for handling toxic behavior? - Can you advocate for changes that [embed diversity and inclusion](https://opensource.com/article/17/9/diversity-and-inclusion-innovation) principles into the development process? - Can you facilitate awareness for others about these critical shortfalls within open-source community projects? - Can you promote diverse role models that can help people see themselves as part of technology? - Can you convince the project to commit to continued focus on creating inclusive community spaces? |
| Savings | **Fund** Directly contributing financial support to specific projects – as well as non-profit funds – can be an impactful yet simple way to contribute to project you want to see succeed. - Can you make a one-time donation? - Can you afford to maintain a recurrent sponsorship? - Can you support any non-profit funds dedicated to crowdsourcing for open-source projects – like [Open Collective](https://opencollective.com/search) and [Software in the Public Interest](https://www.spi-inc.org/donations/)? - Can you fund [organizations focused on improvising diversity](https://www.cio.com/article/191030/make-an-impact-10-tech-focused-di-nonprofits-worth-donating-to.html) within technology – such as [Women in Linux](https://www.pledge.to/women-in-linux-4579), [LGBT Tech](https://www.lgbttech.org/donate), or [Blacks in Technology](https://blacksintechnology.org/donate-2/)? |
| Event | **Plan** Creating an inclusive space is a commitment that is never truly finished and we must continue to make conscious decisions that can lead us to a more equitable future. - Can you create opportunities to include diverse perspectives in the project? - Can you champion role models that center underrepresented people? - Can you form a call to action from within the project to create tangible supports for the many dimensions of diversity within a community? - Can you focus on building equitable learning opportunities that enable people to integrate into the community? - Can you organize accessible events that help introduce mentors to potential new contributors? |
| Forum | **Communicate** Open-source projects are often decentralized, meaning that much of the development happens online through both real-time conversation and asynchronous messaging. If you are good with people, there are so many ways you can help out the open-source community. - Push back against the [myth that open-source is a meritocracy](https://web.archive.org/web/20221004224856/https://www2.deloitte.com/au/en/blog/diversity-inclusion-blog/2019/meritocracy-unraveling-paradox.html). - Integrate into the conversation through forums, mailing lists and chat apps. - Enforce the code of conduct by pressing back on toxic behaviors and getting the maintainers involved. - Even if you cannot code, creating a positive environment for contributors can be as simple as a thank you. - Help get people new to the community up to speed by helping navigate the available documentation. - Attend events and get involved in talks about the project's future. - Be a nexus connecting people within the community based on their skills. |
This is [same technology that major companies use](https://www.docker.com/customer-stories/) to host their websites.
Containers allow administrators to quickly deploy software on nearly any hardware environment from a Raspberry Pi to a full blade server cluster. Docker Engine interfaces directly with the [Linux kernel](https://hub.subspace.services/books/software/page/what-is-linux "What is Linux?") to access the drivers that communicate with your computer's hardware. The mechanism that virtual containers employ is fundamentally different than a [virtual machine](https://en.m.wikipedia.org/wiki/System_virtual_machine), an older technology that performs a similar function. ## Virtual Systems Virtual machines use a "[hypervisor](https://en.m.wikipedia.org/wiki/Hypervisor)" to emulate the virtual hardware necessary to "host" its own "guest" kernel and operating system. This happens under the supervision of your "host" operating system and incurs a great deal of computational overhead. You are essentially using your computer to emulate a fully isolated system with its own hardware, firmware and software that must be juggled.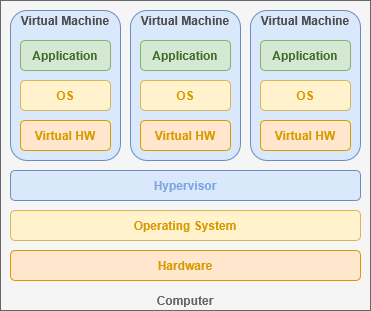
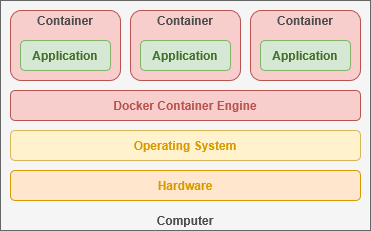
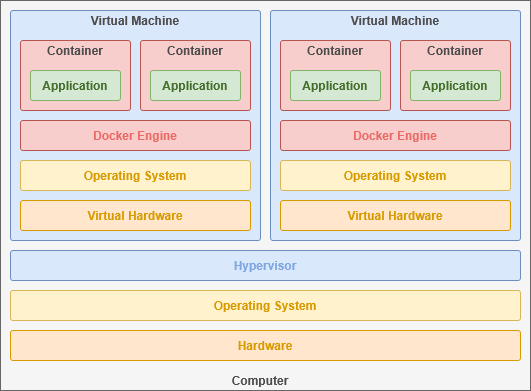
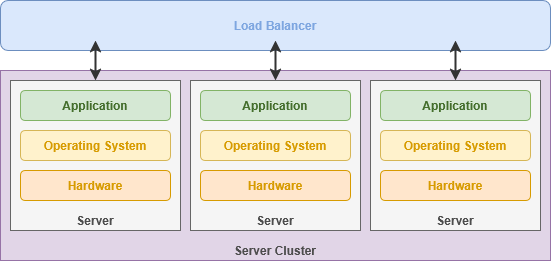
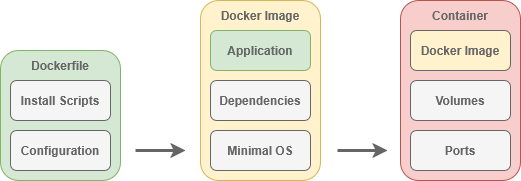
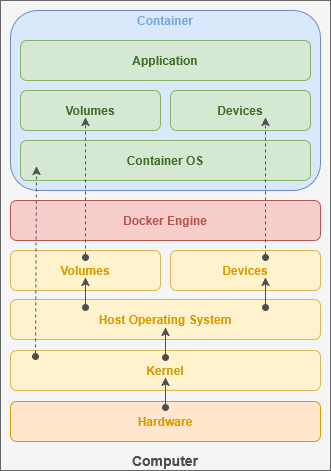
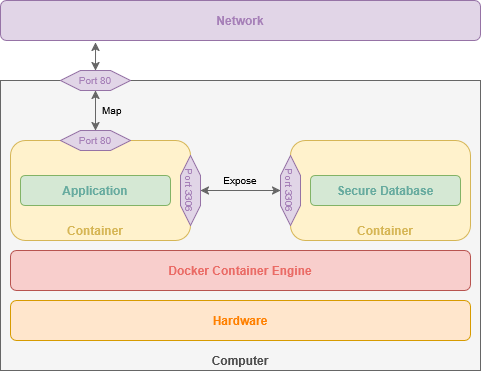
Mapping an [nginx](https://hub.subspace.services/books/nginx "nginx") container – which uses port 80 – to port 4000 on your host computer would be: *"4000:80".*
### Isolated Systems By leveraging ports, we can access multiple services hosted from the same machine, each running in their own container. This is a common practice – known as a Docker Stack – that allows you to deploy new containers as well as define the virtual private networks connecting them. Conceptually, a stack sits a level higher than containers and can consist of several containers that work in tandem.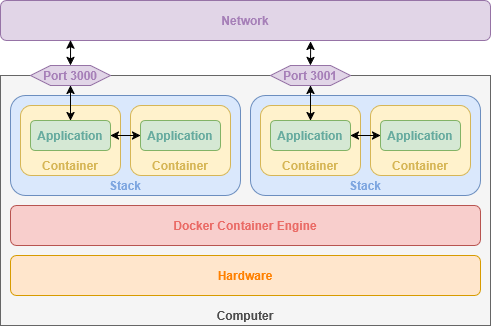
| --it | Keeps the container's shell accessible through the terminal |
| -d | Runs container in the background |
| -p | Opens a port on the container, connecting a port from the container to an external port on our host computer. This allows the service to be accessible by other computers on your network. |
| --name | Name to use for the container |
| -v | Links a directory or file from our host computer to the container so it can access it. |
| scr.io/linuxserver/nginx:latest | The Docker image to use for creating the container |
You can find the [official Docker installation guide](https://docs.docker.com/engine/install/debian/#install-using-the-convenience-script) on their website.
## Preparation First, we need to open our terminal to install a small application called *curl* that can be used to download files through the terminal. Enter this command and hit enter to automatically install the curl software: ```bash sudo apt-get install -y curl ```You will be prompted to enter your password.
| [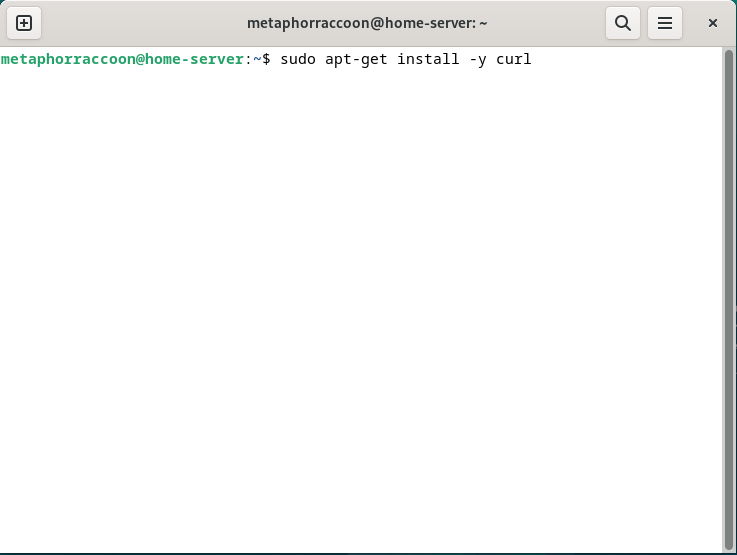](https://hub.subspace.services/uploads/images/gallery/2025-04/yk7image.png) | [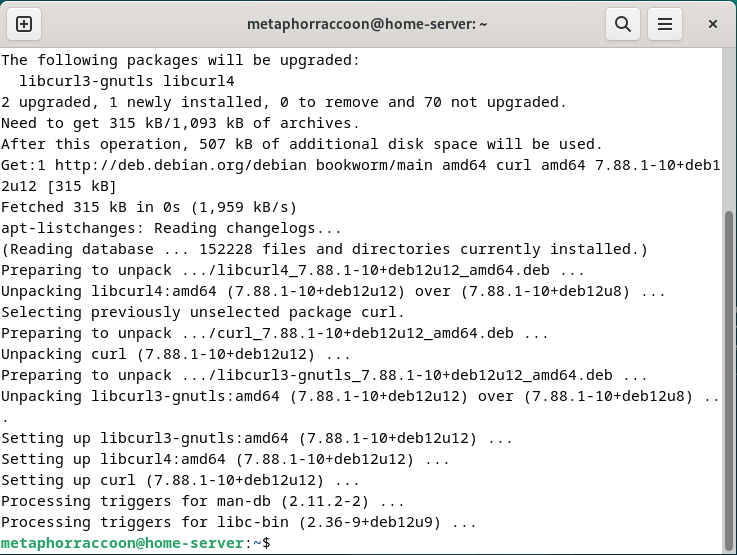](https://hub.subspace.services/uploads/images/gallery/2025-04/v72image.png) |
This requires that the [proprietary Nvidia drivers are installed](https://hub.subspace.services/books/software/page/graphics-card "Setting Up Your Graphics Card") and working correctly.
The process for [installing the required software](https://docs.nvidia.com/datacenter/cloud-native/container-toolkit/latest/install-guide.html) is detailed in their documentation. Once installed, the graphics card can be attached to Docker containers. # Creating Your First Container We will be installing [Portainer](https://www.portainer.io/), an open-source web application that makes it easy to manage Docker from your browser. [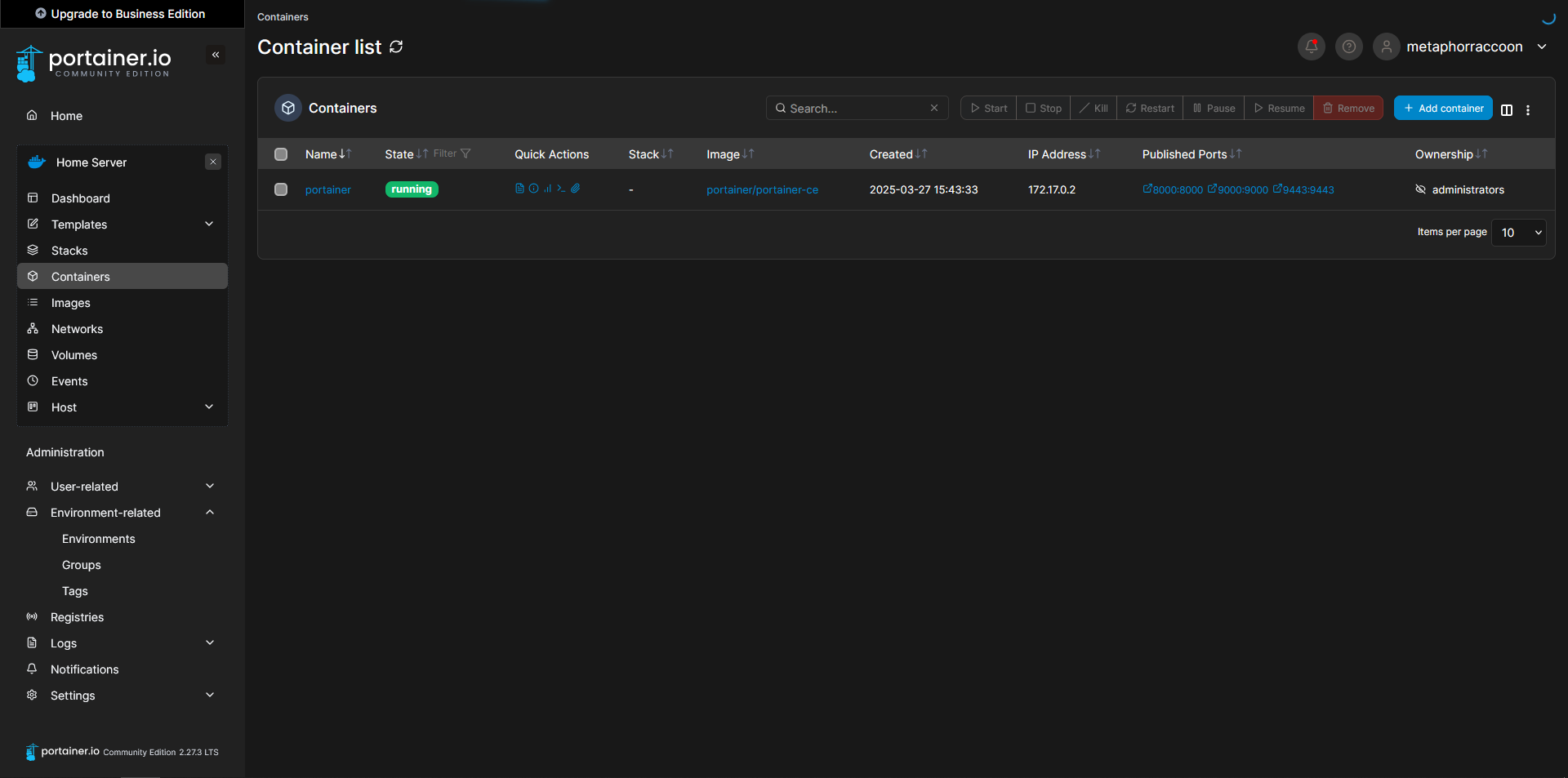](https://hub.subspace.services/uploads/images/gallery/2025-03/capture9.PNG) ## Starting Portainer We are adding port 9000 which isn't used by default. This allows Portainer to be accessed through HTTP instead of HTTPS.You can find the [official Portainer installation guide](https://docs.portainer.io/start/install-ce/server/docker/linux) on their website.
Using the terminal, we will issue the command to start our new Docker container: ```bash sudo docker run -d -p 8000:8000 -p 9000:9000 -p 9443:9443 --name=portainer --restart=always -v /var/run/docker.sock:/var/run/docker.sock -v /srv/portainer:/data portainer/portainer-ce ``` Docker will download the image and start the container. [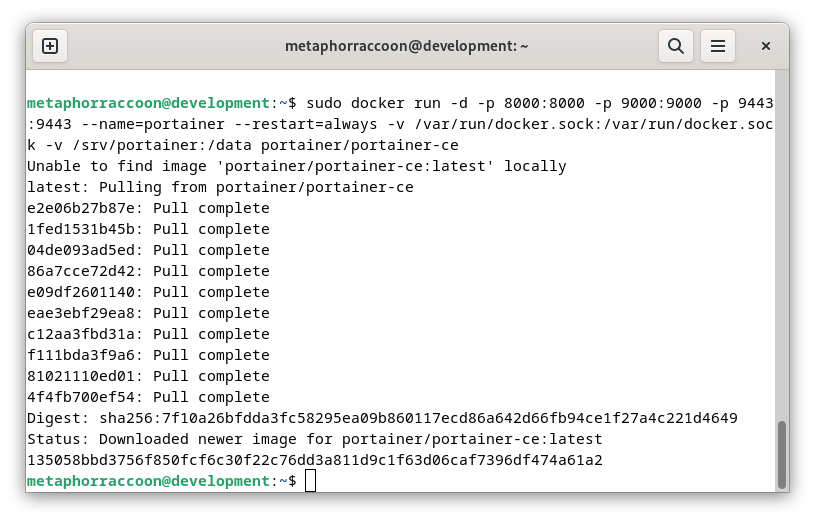](https://hub.subspace.services/uploads/images/gallery/2025-03/nyIimage.png)Once the command has finished, we can verify that Portainer is operational by querying Docker's running containers: ```bash sudo docker ps ``` [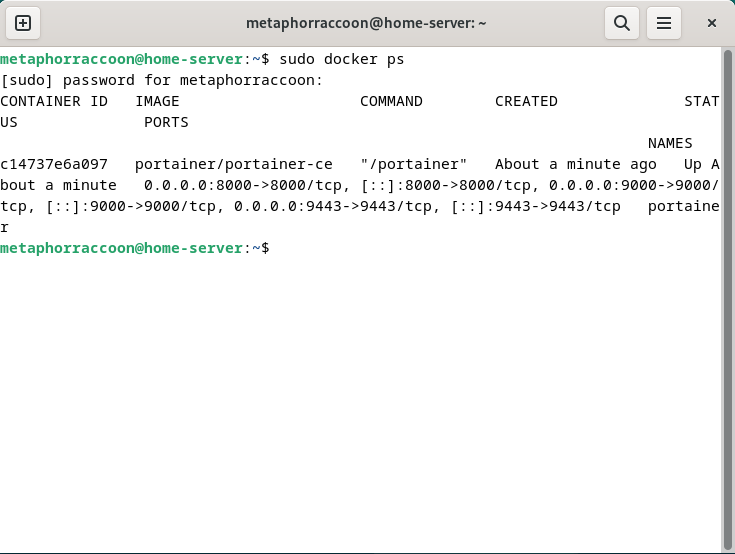](https://hub.subspace.services/uploads/images/gallery/2025-04/DX0image.png) The command should return our running Portainer container and show that it's available under four different ports. ## Creating an Admin Account In order to configure our instance of Portainer, we will need to open a web browser.We recommend [Mozilla Firefox,](https://www.mozilla.org/en-US/firefox/) but [Google Chrome](https://www.google.com/chrome/) will also work.
Once the web browser is open, go to [http://localhost:9000/](http://localhost:9000/) to load Portainer. [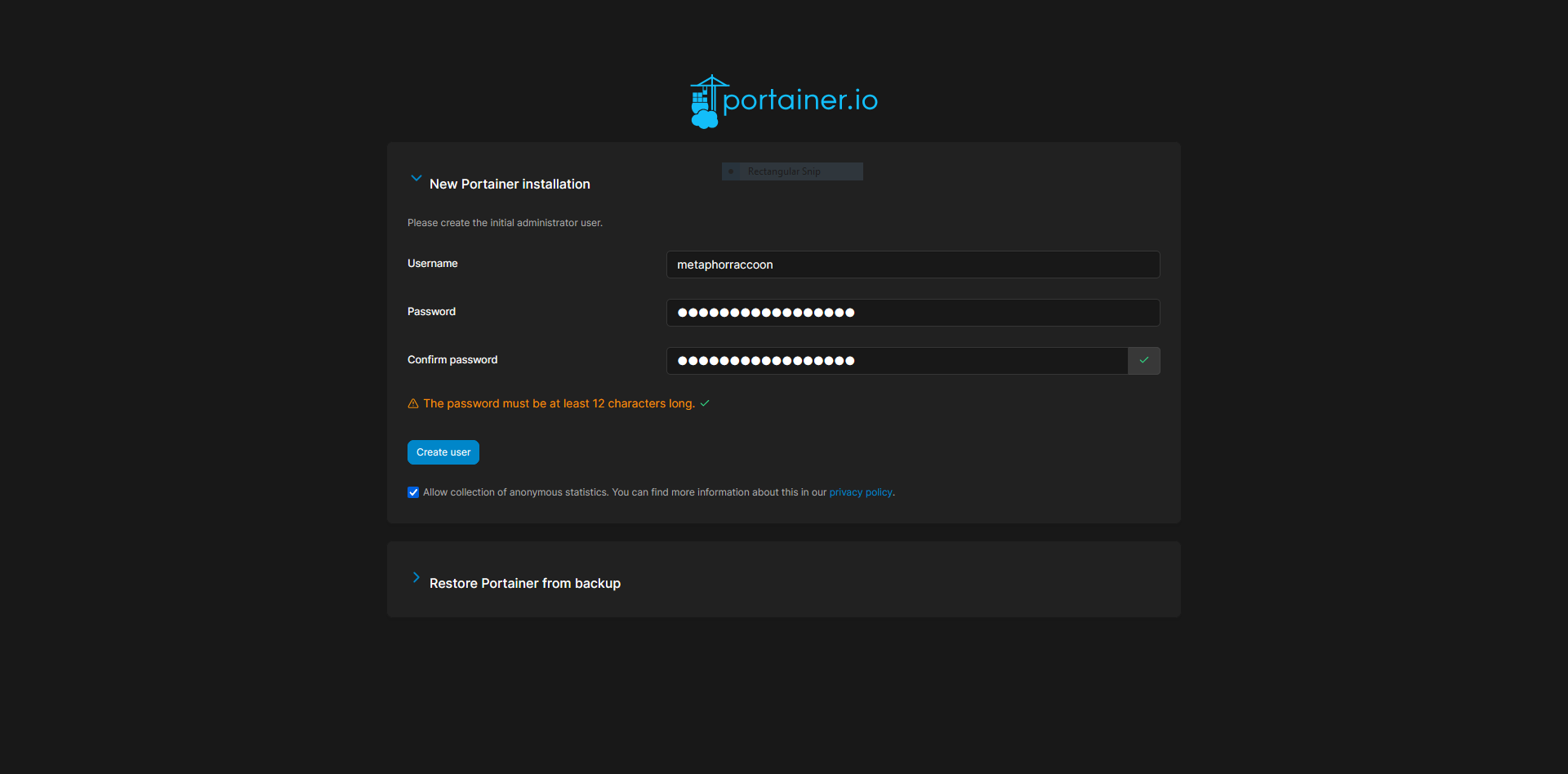](https://hub.subspace.services/uploads/images/gallery/2025-03/QSTcapture.PNG) Here, we are instructed to create an administrator account and set a secure password. This will be used in the future to login to Portainer.**The account creation wizard will time-out if not completed quickly.** If this happens, restart Portainer with the command: *docker restart portainer*.
[](https://hub.subspace.services/uploads/images/gallery/2025-03/jC5capture2.PNG) ## Adding Docker Once we have created an account, we will be able to select our Docker service. If everything is working as expected, you should be able to click 'Get Started' to use the local Docker service. [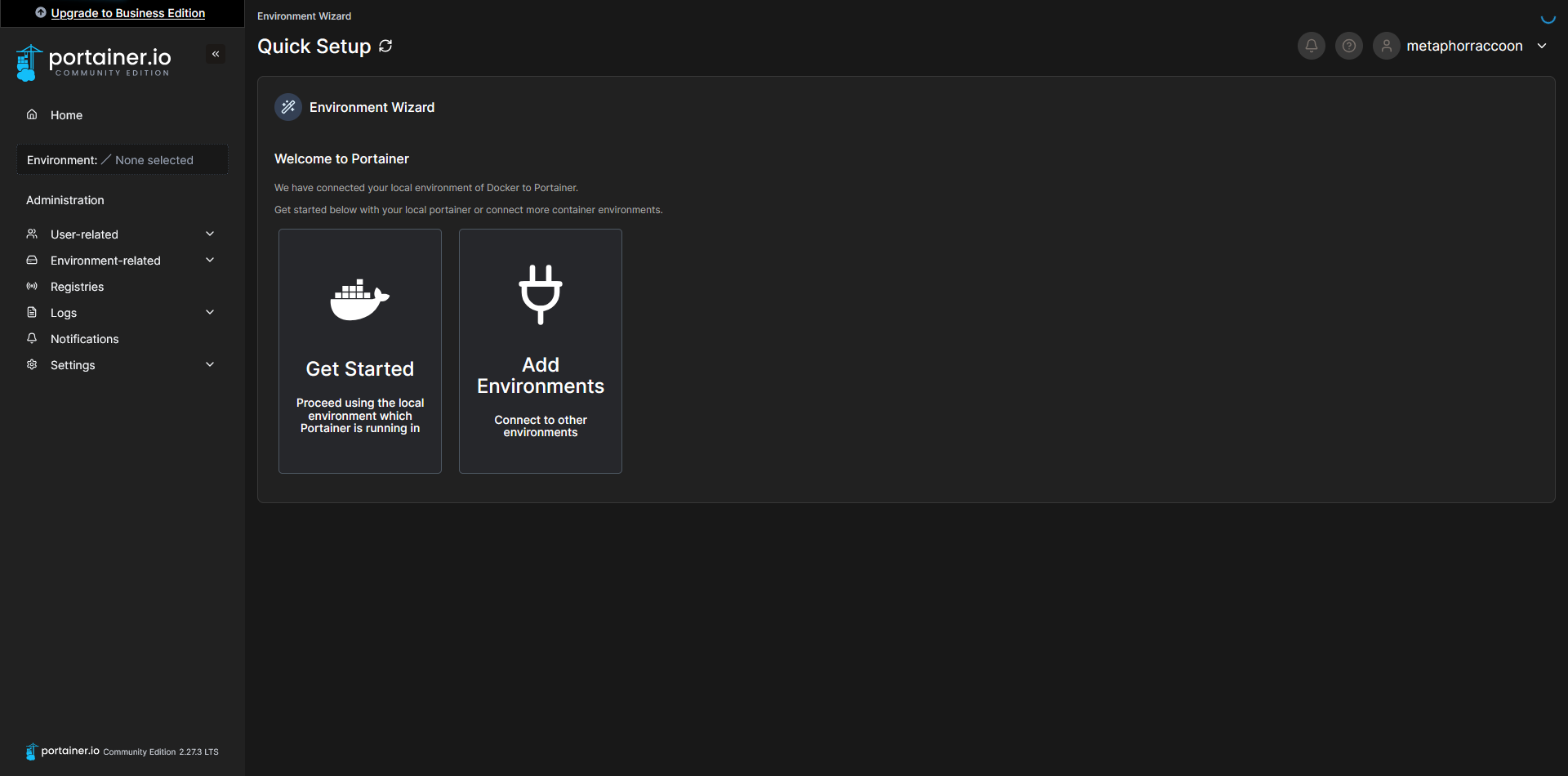](https://hub.subspace.services/uploads/images/gallery/2025-03/Q0jcapture3.PNG) This will bring you to a list of Docker installations that are available to Portainer.You can use the [Portainer Agent](https://docs.portainer.io/admin/environments/add/docker/agent) to control Docker on additional servers.
[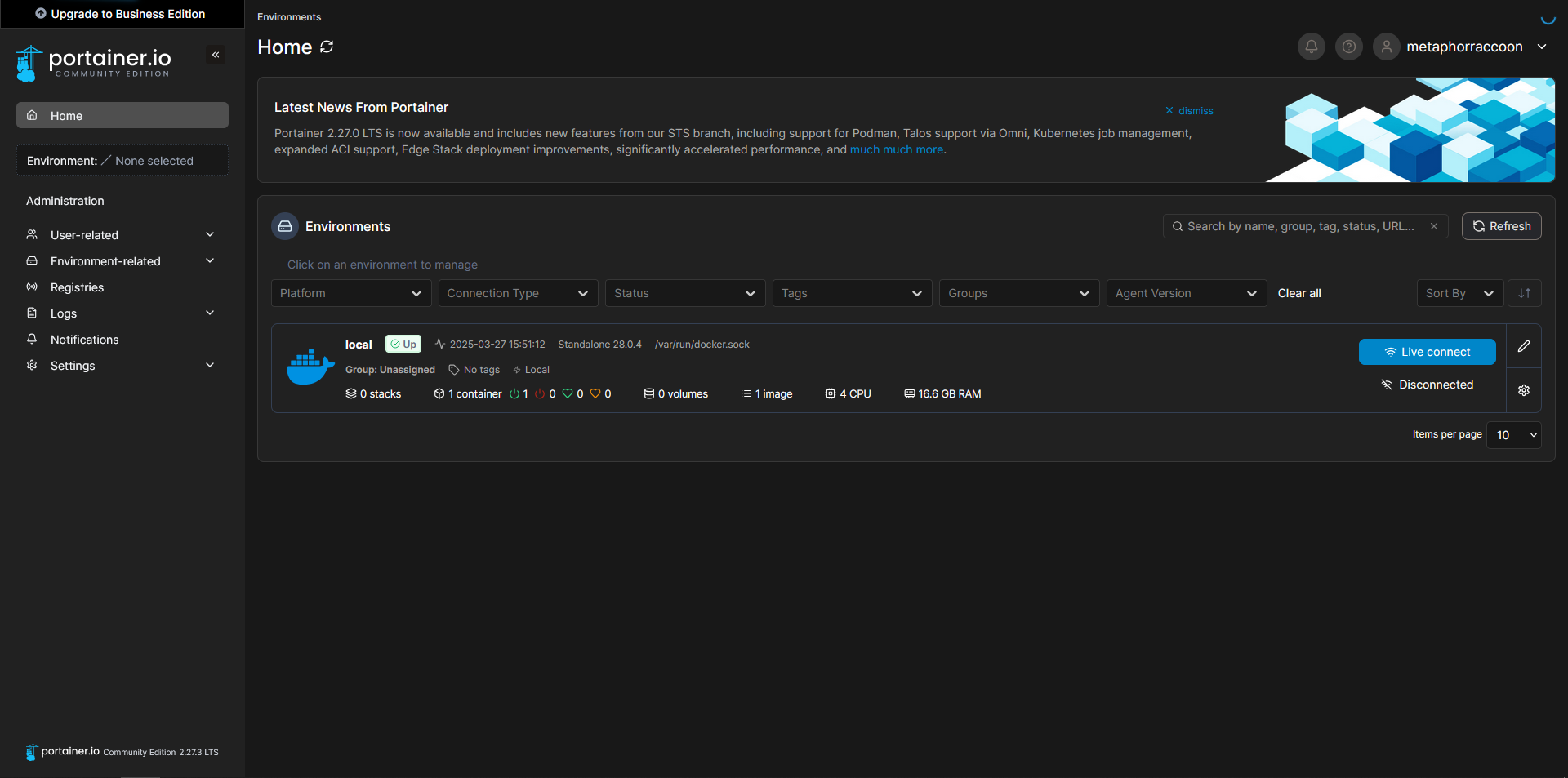](https://hub.subspace.services/uploads/images/gallery/2025-03/oADcapture4.PNG) Now, we can configure the name of our Docker server, for personal preference, as well as set the root IP address of our server so we can quickly access our services from Portainer. Select the pencil icon next to your "local" Environment. [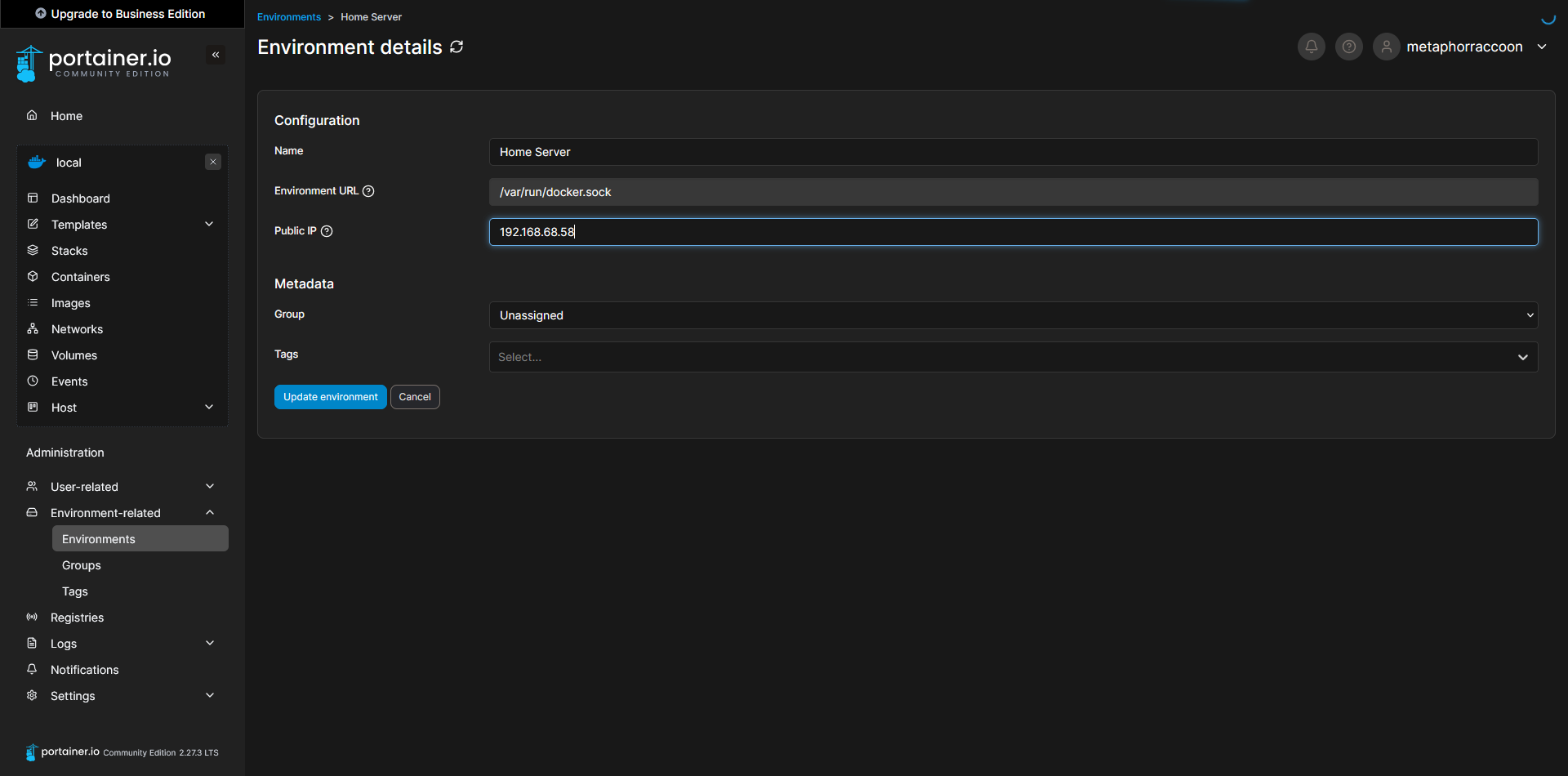](https://hub.subspace.services/uploads/images/gallery/2025-03/capture7.PNG) If you are unsure about the LAN IP address [we selected earlier](https://hub.subspace.services/books/software/page/networking "Static Network IP"), you can run the command below to obtain it: ```bash ip -o route show | grep default ``` [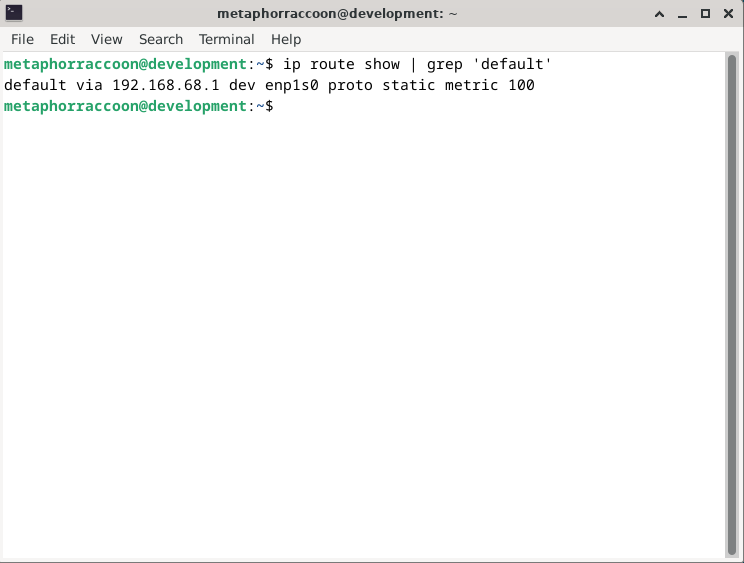](https://hub.subspace.services/uploads/images/gallery/2025-02/rzDimage.png) Once you have completed that, you can save the settings to apply them. When returning to the home screen, we can see that our settings were updated. [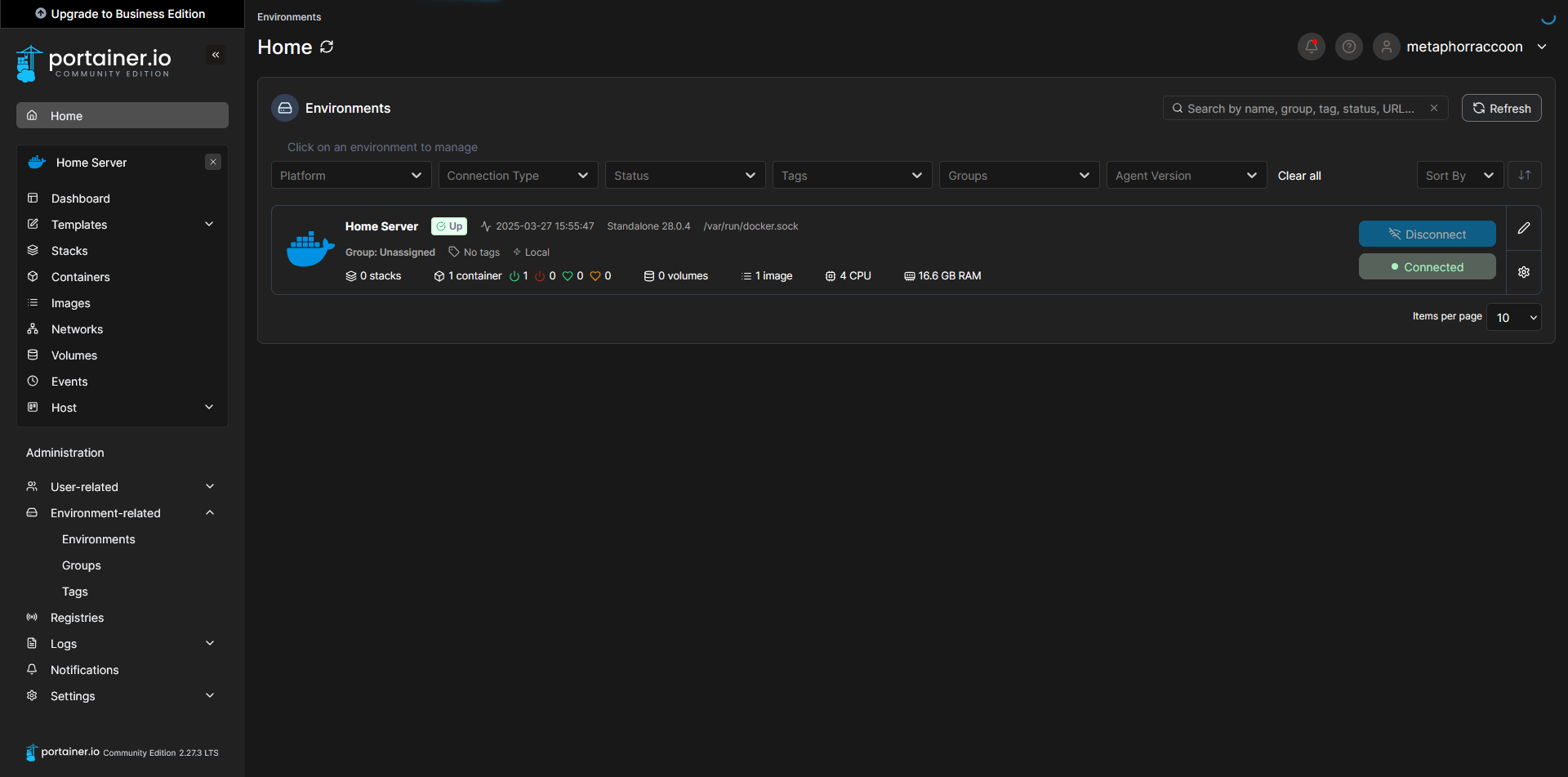](https://hub.subspace.services/uploads/images/gallery/2025-03/capture8.PNG) Clicking on our Docker environment – named "Home Server" here – will pull up a list of our running containers. You can see the first and only one listed is our newly created Portainer installation. [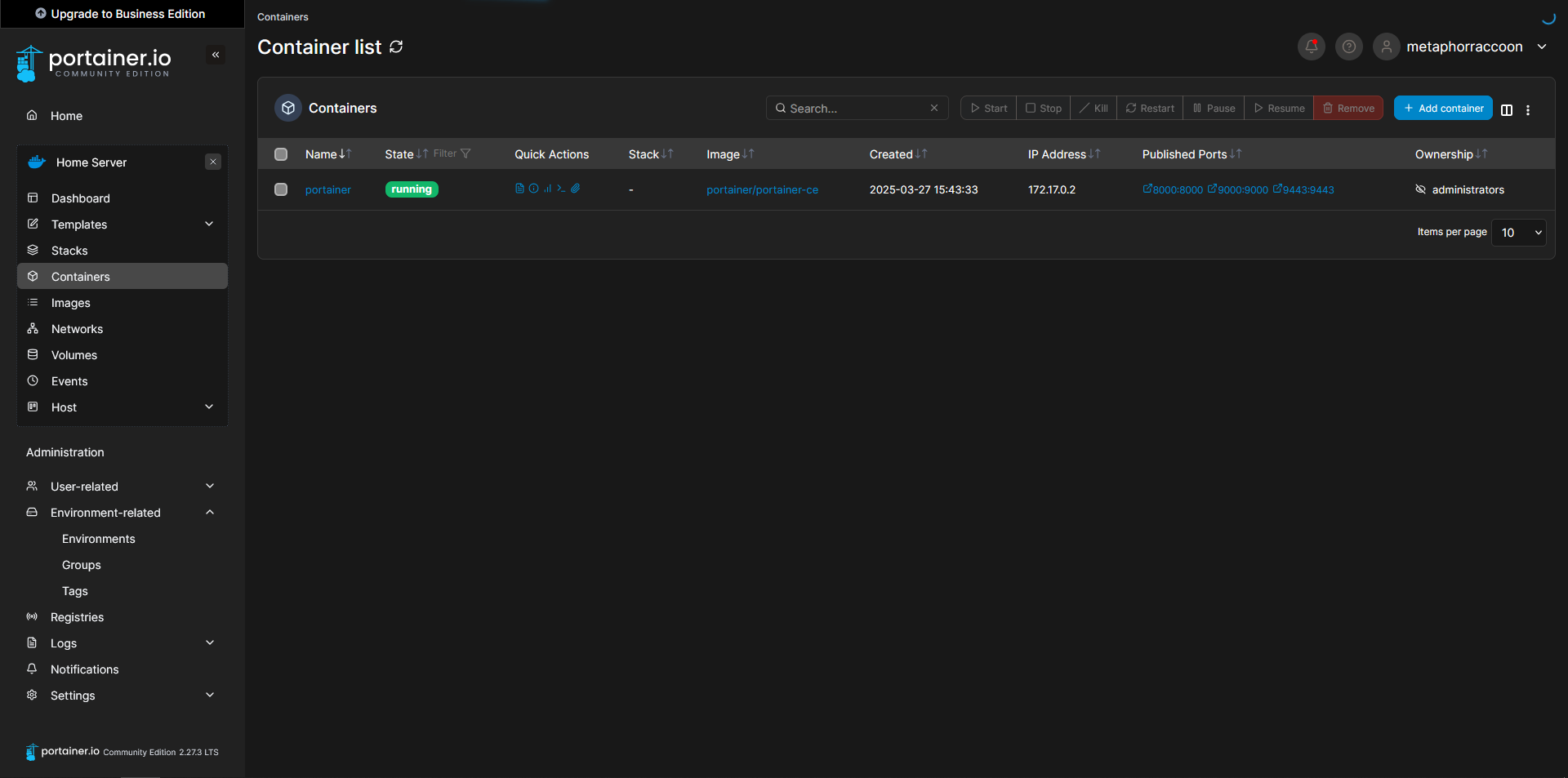](https://hub.subspace.services/uploads/images/gallery/2025-03/capture9.PNG) Clicking on "8000:8000" under assigned ports will open this port using your web browser. In this instance, it should open Portainer in a new tab. [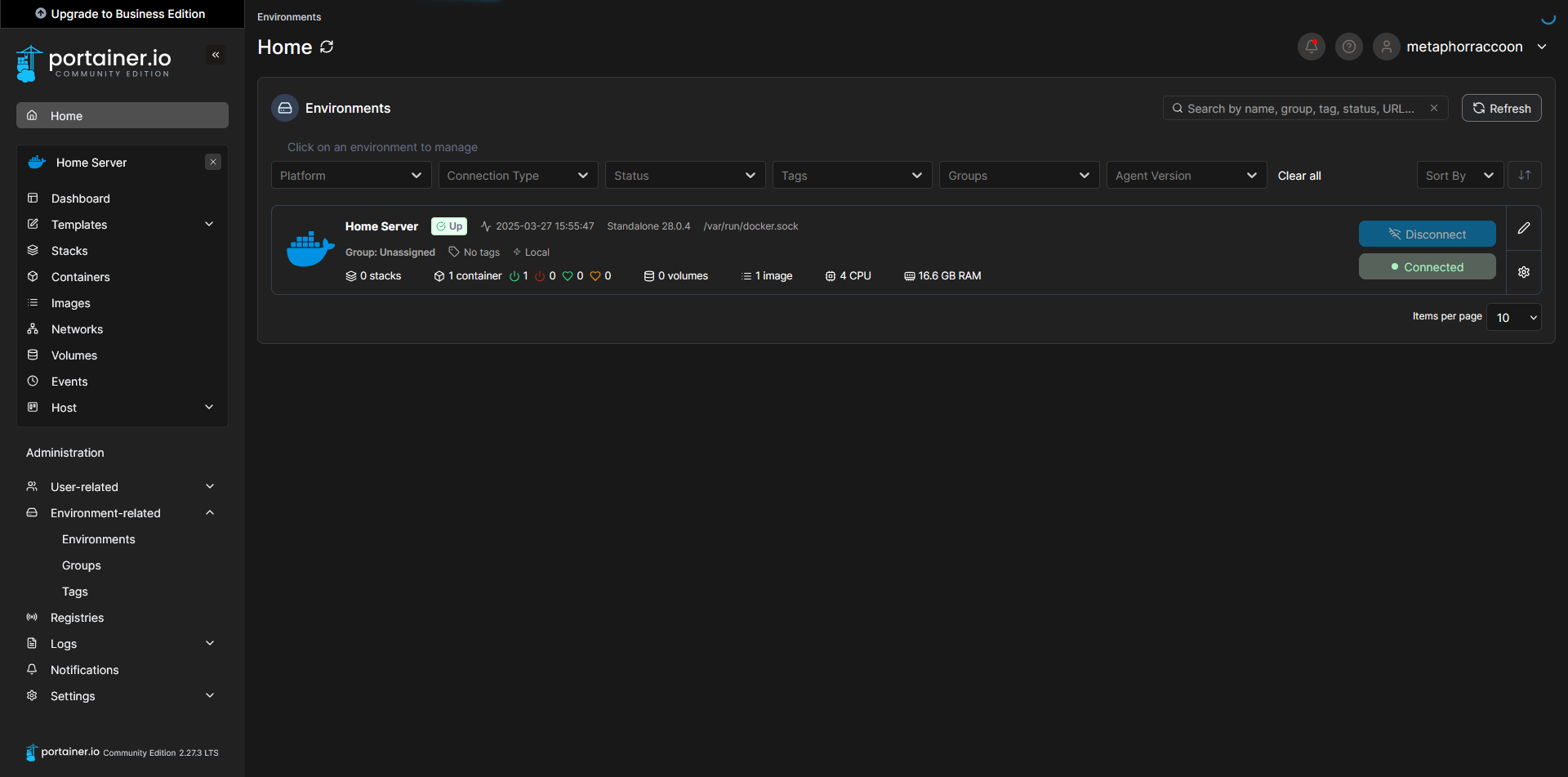](https://hub.subspace.services/uploads/images/gallery/2025-03/capture8.PNG) # Next Steps Now that we have created a solid server foundation, we can begin to install our desired services through [Portainer](https://hub.subspace.services/books/portainer "Portainer"). We will use [Docker Compose](https://hub.subspace.services/books/software/page/what-is-docker "What is Docker?") markup to quickly self-host new web applications. [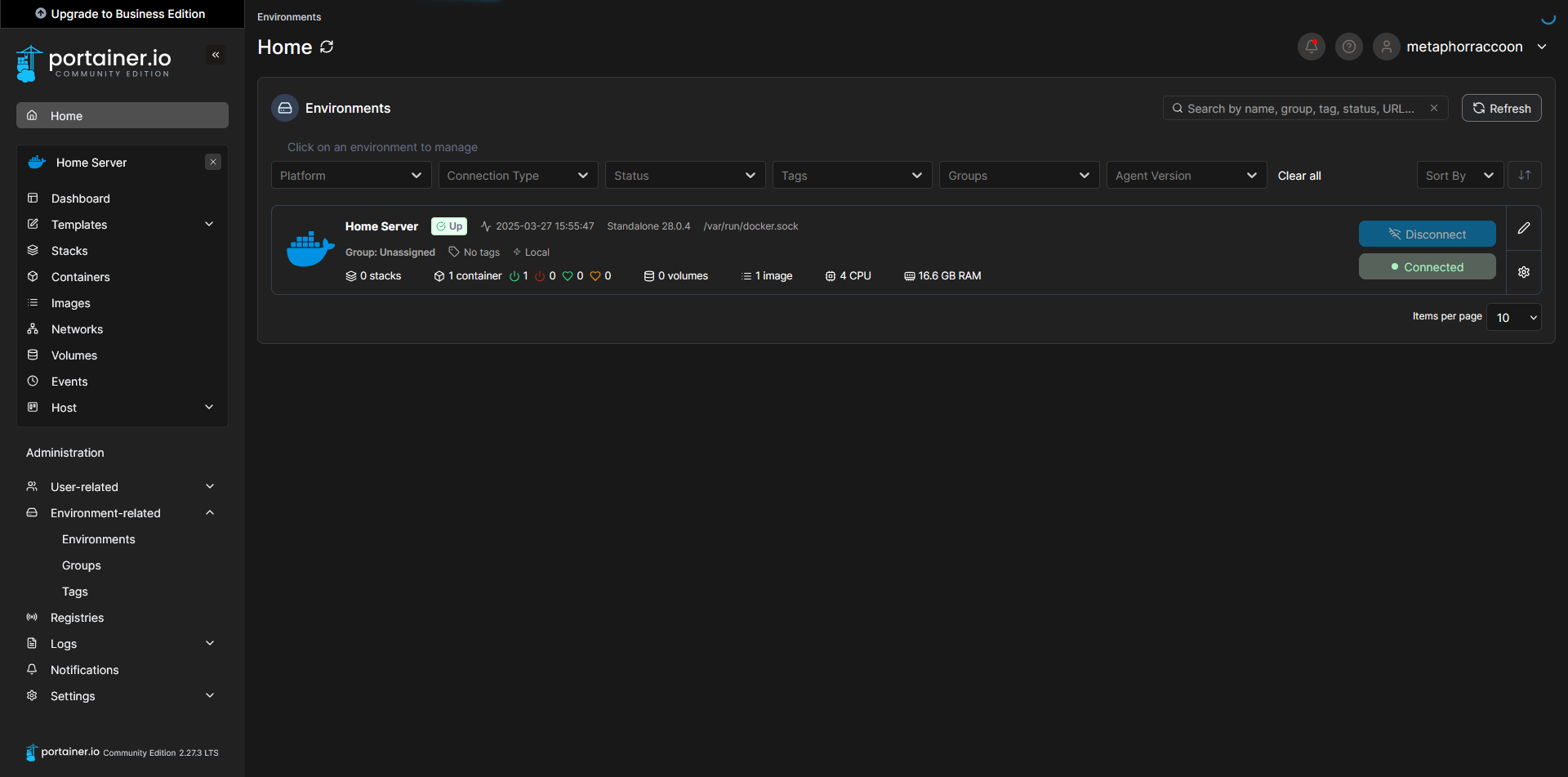](https://hub.subspace.services/uploads/images/gallery/2025-03/capture8.PNG) [](https://hub.subspace.services/books/services "Next Steps")